In what is actually a scenario of hackers obtaining hacked, a notable underground on the net criminal forum by the name of Maza has been compromised by unknown attackers, making it the fourth forum to have been breached since the get started of the year.
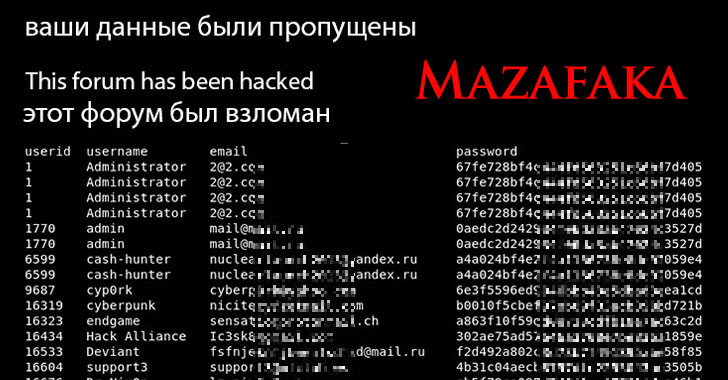
The intrusion is mentioned to have transpired on March 3, with details about the discussion board members — such as usernames, email addresses, and hashed passwords — publicly disclosed on a breach notification web page place up by the attackers, stating “Your knowledge has been leaked” and “This discussion board has been hacked.”
“The announcement was accompanied by a PDF file allegedly containing a part of forum user info. The file comprised more than 3,000 rows, containing usernames, partially obfuscated password hashes, email addresses and other get hold of information,” cybersecurity company Intel 471 claimed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
At first called Mazafaka, Maza is an elite, invite-only Russian-language cybercrime discussion board known to be operational as early as 2003, performing as an distinctive online space for exploit actors to trade ransomware-as-a-support equipment and perform other types of illicit cyber operations.
The advancement comes near on the heels of successful breaches of other community forums, which includes that of Verified, Crdclub, and Exploit.
Confirmed is stated to have been breached on January 20, 2021, with the actor driving the attack professing obtain to the full databases on a different popular forum called Raid Community forums, in addition to transferring $150,000 worth of cryptocurrency from Verified’s bitcoin wallet to their have. The forum, even so, staged a return final thirty day period on February 18 with a improve in possession, according to Flashpoint.
Then once more, in February, a cybercrime discussion board by the identify of Crdclub disclosed an attack that resulted in the compromise of an administrator account with the target of defrauding its members. No other particular details appears to have been plundered.
“By undertaking so, the actor guiding the attack was able to entice discussion board consumers to use a money transfer provider that was allegedly vouched for by the forum’s admins,” Intel 471 reported. “That was a lie, and resulted in an not known amount of cash staying diverted from the forum.”
Finally, earlier this week, the Exploit cybercrime forum sustained an attack that associated an clear compromise of a proxy server employed for safeguarding the discussion board from dispersed denial-of-services (DDoS) attacks.
Aspects are fuzzy as to the perpetrators of the attacks, with forum customers speculating that it could be the do the job of a government intelligence company, when also distressing about the chance that their genuine-environment identities could be exposed in the wake of the leaks.
Flashpoint researchers famous that the Russian sentences on the Maza forum’s notification web site were being probably translated applying an on the web translator, but included it’s unclear if this indicates the involvement of a non-Russian speaking actor or if it was intentionally made use of to mislead attribution.
“Even though Intel 471 just isn’t conscious of anybody claiming obligation for the breaches, whomever is guiding the actions has indirectly supplied researchers an advantage,” the firm concluded. “Any information unearthed from the breaches aids in the battle versus these criminals because of to the additional visibility it gives security groups who are tracking actors that populate these message boards.”
Uncovered this post attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to go through extra special content material we put up.
Some components of this article are sourced from:
thehackernews.com

 SITA Supply Chain Breach Hits Multiple Airlines
SITA Supply Chain Breach Hits Multiple Airlines