Infection chains associated with the multi-function Qakbot malware have been broken down into “distinctive constructing blocks,” an hard work that Microsoft mentioned will support to detect and block the risk in an productive way proactively.
The Microsoft 365 Defender Menace Intelligence Staff dubbed Qakbot a “customizable chameleon that adapts to go well with the demands of the numerous menace actor teams that utilize it.”
Qakbot is thought to be the development of a monetarily enthusiastic cybercriminal danger group identified as Gold Lagoon. It is a prevalent information-stealing malware that, in modern decades, has grow to be a precursor to many critical and widespread ransomware attacks, presenting a malware set up-as-a-provider that permits many campaigns.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Initial found in 2007, the modular malware — like TrickBot — has progressed from its early roots as a banking trojan to become a Swiss Military knife able of information exfiltration and performing as a shipping mechanism for the next stage payloads, which includes ransomware. Also noteworthy is its tactic of hijacking victims’ respectable email threads from Outlook shoppers via an Email Collector element and working with individuals threads as phishing lures to infect other devices.
“Compromising IMAP products and services and email provider companies (ESPs), or hijacking email threads permits attackers to leverage the trust a probable target has in persons they have corresponded with just before, and it also lets for the impersonation of a compromised corporation,” Pattern Micro scientists Ian Kenefick and Vladimir Kropotov comprehensive very last thirty day period. “In fact, meant targets will be considerably far more very likely to open up emails from a identified sender.”
Qakbot action tracked by the cybersecurity business above a 7 month period among March 25, 2021, and October 25, 2021, present that the U.S., Japan, Germany, India, Taiwan, Italy, South Korea, Turkey, Spain, and France are the major targeted nations, with the intrusions mostly placing telecommunications, technology, and schooling sectors.
Extra lately, spam campaigns have resulted in the deployment of a new loader termed SQUIRRELWAFFLE that enables the attackers to achieve an preliminary foothold into company networks and drop destructive payloads, this sort of as Qakbot and Cobalt Strike, on infected methods.
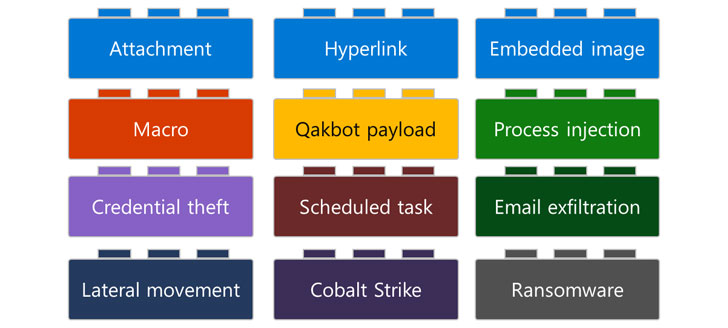
Now in accordance to Microsoft, the attack chains involving Qakbot comprise of numerous building blocks that chart the different phases of the compromise, appropriate from the approaches adopted to distribute the malware — backlinks, attachments, or embedded images — in advance of carrying out an array of article-exploitation actions this kind of as credential theft, email exfiltration, lateral movement, and the deployment of Cobalt Strike beacons and ransomware.
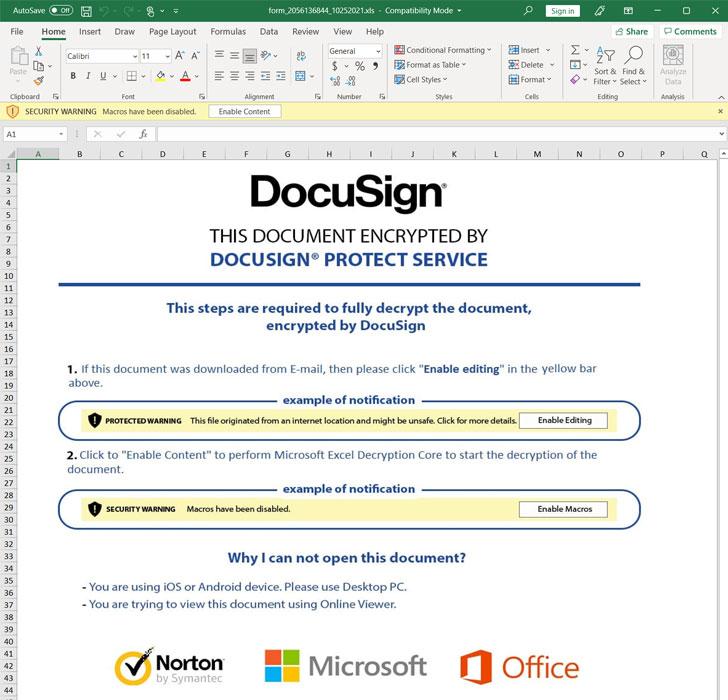
The Redmond-based mostly enterprise observed that Qakbot-linked email messages despatched by the attackers may, at periods, come with a ZIP archive file attachment that consists of a spreadsheet that contains Excel 4. macros, an preliminary access vector that’s commonly abused in phishing attacks. Irrespective of the mechanism utilized to supply the malware, the strategies have in frequent their use of destructive Excel 4. macros.

Though macros are turned off by default in Microsoft Business, recipients of the email messages are prompted to empower the macro to look at the document’s genuine content. This triggers the upcoming phase of the onslaught to down load the destructive payloads from 1 or extra attacker-managed domains.
Far more normally than not, Qakbot is just the first move in what is aspect of a bigger attack, with the danger actors utilizing the original foothold facilitated by the malware to set up supplemental payloads or offer the entry to the greatest bidder on underground boards who can then leverage it for their individual finishes. In June 2021, company security organization Proofpoint uncovered how ransomware actors are progressively shifting from using email messages as an intrusion route to buying obtain from cybercriminal enterprises that have previously infiltrated key entities.
“Qakbot’s modularity and adaptability could pose a problem for security analysts and defenders simply because concurrent Qakbot campaigns could seem strikingly different on each and every afflicted product, noticeably impacting how these defenders answer to these attacks,” the scientists said. “Consequently, a deeper knowing of Qakbot is paramount in constructing a thorough and coordinated defense strategy versus it.”
Uncovered this posting interesting? Adhere to THN on Fb, Twitter and LinkedIn to read far more exceptional written content we put up.
Some components of this article are sourced from:
thehackernews.com


 The risks and strategies of using privacy as a business differentiator
The risks and strategies of using privacy as a business differentiator