Microsoft has disclosed aspects of a now-patched security flaw in Apple macOS that could be exploited by an attacker to get around security protections imposed to protect against the execution of malicious programs.
The shortcoming, dubbed Achilles (CVE-2022-42821, CVSS score: 5.5), was addressed by the iPhone maker in macOS Ventura 13, Monterey 12.6.2, and Big Sur 11.7.2, describing it as a logic issue that could be weaponized by an app to circumvent Gatekeeper checks.
“Gatekeeper bypasses these kinds of as this could be leveraged as a vector for original entry by malware and other threats and could assist increase the good results rate of destructive campaigns and attacks on macOS,” Jonathan Bar Or of the Microsoft 365 Defender Investigation Staff mentioned.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Gatekeeper is a security mechanism created to assure that only trustworthy applications run on the functioning process. This is enforced by suggests of an prolonged attribute called “com.apple.quarantine” that is assigned to documents downloaded from the internet. It is analogous to the Mark of the Web (MotW) flag in Windows.
Consequently when an unsuspecting consumer downloads a probably unsafe app that impersonates a piece of legit computer software, the Gatekeeper element helps prevent the apps from currently being operate as it really is not validly signed and notarized by Apple.
Even in situations where an app is accredited by Apple, people are shown a prompt when it can be introduced for the very first time to find their specific consent.
Presented the critical function played by Gatekeeper in macOS, it truly is challenging not to picture the effects of sidestepping the security barrier, which could successfully allow danger actors to deploy malware on the machines.
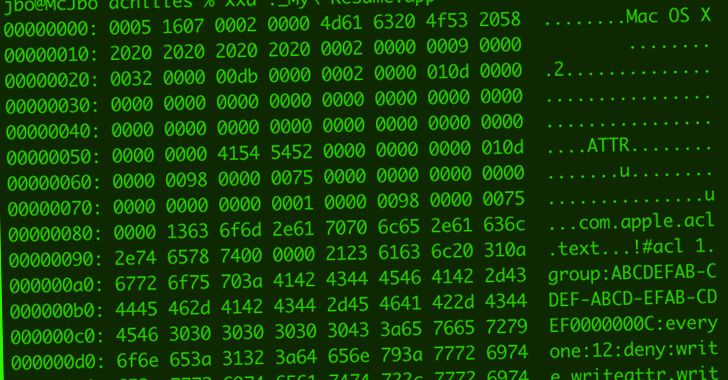
The Achilles vulnerability discovered by Microsoft exploits a permission model termed Accessibility Handle Lists (ACLs) to insert exceptionally restrictive permissions to a downloaded file (i.e., “every person deny compose,writeattr,writeextattr,writesecurity,chown”), thus blocking Safari from placing the quarantine prolonged attribute.
In a hypothetical attack state of affairs, an adversary could embrace the approach to craft a rogue app and host it on a server, which could then be shipped to a achievable target by way of social engineering, destructive advertisements, or a watering hole.
The technique also circumvents Apple’s freshly released Lockdown Manner in macOS Ventura – an decide-in restrictive location to counter zero-simply click exploits – necessitating that users utilize the most up-to-date updates to mitigate threats.
“Faux applications continue to be a person of the top rated entry vectors on macOS, indicating Gatekeeper bypass methods are an interesting and even a needed capacity for adversaries to leverage in attacks,” Bar Or reported.
Discovered this post intriguing? Follow us on Twitter and LinkedIn to read much more special content we article.
Some parts of this short article are sourced from:
thehackernews.com

 Researchers Discover Malicious PyPI Package Posing as SentinelOne SDK to Steal Data
Researchers Discover Malicious PyPI Package Posing as SentinelOne SDK to Steal Data