Microsoft on Wednesday disclosed details of a now-patched “superior severity vulnerability” in the TikTok app for Android that could enable attackers consider in excess of accounts when victims clicked on a malicious link.
“Attackers could have leveraged the vulnerability to hijack an account with no users’ awareness if a qualified person only clicked a specifically crafted link,” Dimitrios Valsamaras of the Microsoft 365 Defender Analysis Group reported in a produce-up.
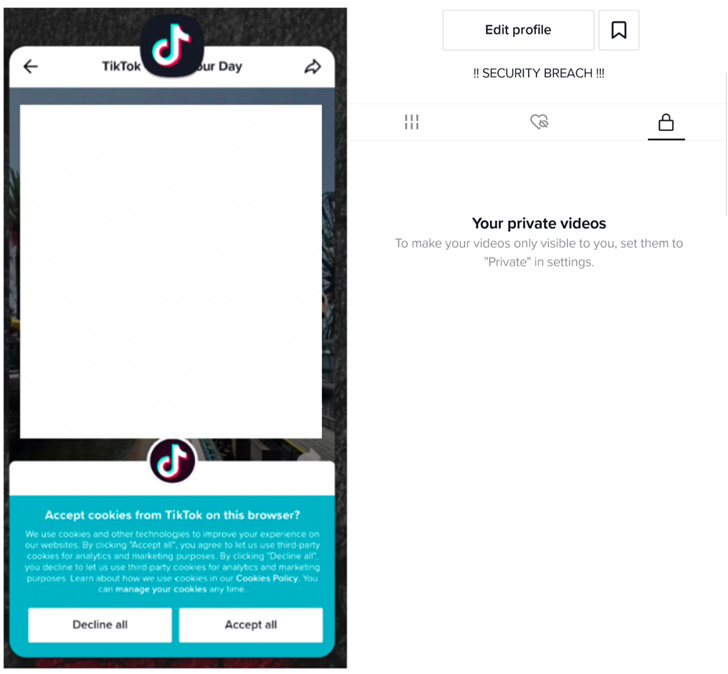
Profitable exploitation of the flaw could have permitted malicious actors to accessibility and modify users’ TikTok profiles and sensitive details, foremost to the unauthorized exposure of private videos. Attackers could also have abused the bug to ship messages and add films on behalf of people.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The issue, resolved in model 23.7.3, impacts two flavors of its Android application com.ss.android.ugc.trill (for East and Southeast Asian end users) and com.zhiliaoapp.musically (for end users in other countries besides for India, wherever it truly is banned). Put together, the applications have far more than 1.5 billion installations involving them.
Tracked as CVE-2022-28799 (CVSS rating: 8.8), the vulnerability has to do with the app’s managing of what is actually known as a deeplink, a particular hyperlink that makes it possible for applications to open up a precise source in one more application installed on the device relatively than directing consumers to a site.
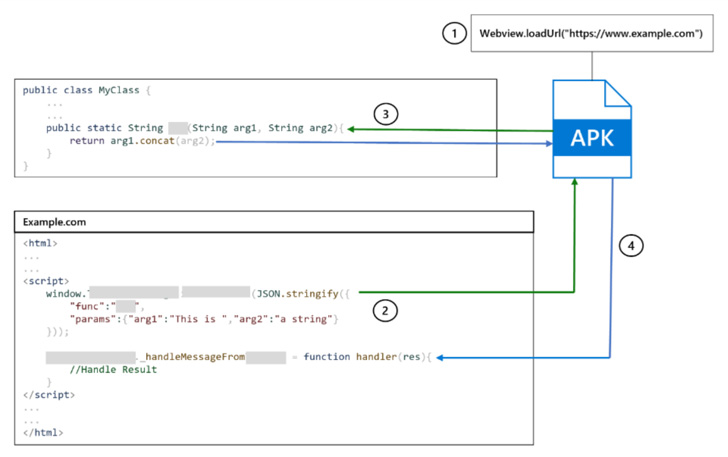
“A crafted URL (unvalidated deeplink) can force the com.zhiliaoapp.musically WebView to load an arbitrary web page,” according to an advisory for the flaw. “This may possibly enable an attacker to leverage an hooked up JavaScript interface for the takeover with one simply click.”
Put only, the flaw can make it feasible to circumvent the apps’s restrictions to reject untrusted hosts and load any internet site of the attacker’s selection through the Android Technique WebView, a system to display web material on other applications.

“The filtering will take location on the server-side and the choice to load or reject a URL is centered on the reply been given from a individual HTTP GET ask for,” Valsamaras stated, introducing the static investigation “indicated that it is doable to bypass the server-facet check by incorporating two further parameters to the deeplink.”
A consequence of this exploit designed to hijack WebView to load rogue internet sites is that it could permit the adversary to invoke over 70 exposed TikTok endpoints, properly compromising a user’s profile integrity. You will find no proof that the bug has been weaponized in the wild.
“From a programming standpoint, utilizing JavaScript interfaces poses significant risks,” Microsoft mentioned. “A compromised JavaScript interface can probably let attackers to execute code applying the application’s ID and privileges.”
Discovered this short article appealing? Follow THN on Facebook, Twitter and LinkedIn to read more unique written content we post.
Some pieces of this post are sourced from:
thehackernews.com


 Apple Releases iOS Update for Older iPhones to Fix Actively Exploited Vulnerability
Apple Releases iOS Update for Older iPhones to Fix Actively Exploited Vulnerability