An unpatched design flaw in the implementation of Microsoft Exchange’s Autodiscover protocol has resulted in the leak of approximately 100,000 login names and passwords for Windows domains around the globe.
“This is a critical security issue, considering the fact that if an attacker can control these domains or has the potential to ‘sniff’ targeted visitors in the identical network, they can capture domain credentials in basic textual content (HTTP essential authentication) that are being transferred above the wire,” Guardicore’s Amit Serper reported in a complex report.
“Furthermore, if the attacker has DNS-poisoning capabilities on a large scale (these types of as a nation-condition attacker), they could systematically syphon out leaky passwords by a large-scale DNS poisoning campaign primarily based on these Autodiscover TLDs [top-level domains].”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Trade Autodiscover provider allows users to configure programs these kinds of as Microsoft Outlook with minimal person enter, permitting just a combination of email addresses and passwords to be utilized to retrieve other predefined settings demanded to set up their email shoppers.
The weakness learned by Guardicore resides in a certain implementation of Autodiscover centered on the POX (aka “simple outdated XML”) XML protocol that results in the web requests to Autodiscover domains to be leaked exterior of the user’s domain but in the exact top-degree area.
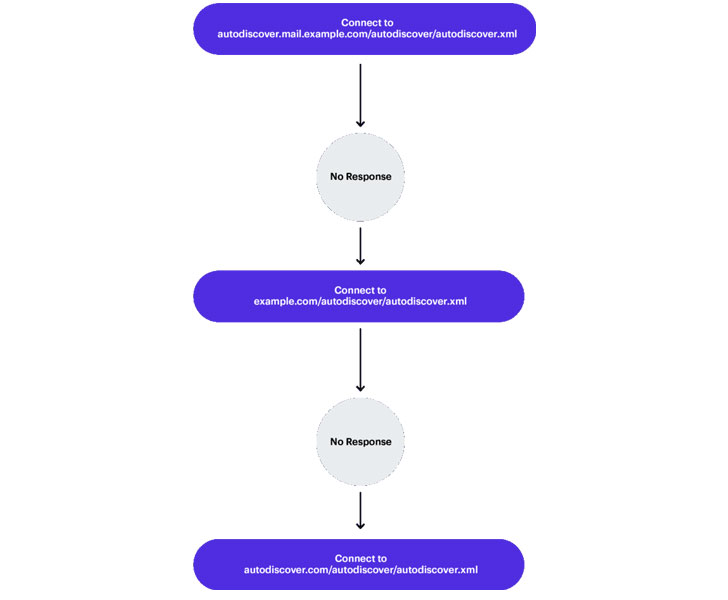
In a hypothetical case in point where a user’s email deal with is “[email protected],” the email customer leverages the Autodiscover company to assemble a URL to fetch the configuration info making use of any of the under combinations of the email area, a subdomain, and a path string, failing which it instantiates a “back-off” algorithm —
- https://Autodiscover.example.com/Autodiscover/Autodiscover.xml
- https://Autodiscover.case in point.com/Autodiscover/Autodiscover.xml
- https://case in point.com/Autodiscover/Autodiscover.xml
- https://illustration.com/Autodiscover/Autodiscover.xml
“This ‘back-off’ system is the offender of this leak mainly because it is often striving to resolve the Autodiscover portion of the area and it will usually test to ‘fail up,’ so to discuss,” Serper stated. “Indicating, the outcome of the future attempt to build an Autodiscover URL would be: ‘https://Autodiscover.com/Autodiscover/Autodiscover.xml.’ This suggests that whoever owns Autodiscover.com will get all of the requests that can’t achieve the unique area.”

Armed with this discovery and by registering a selection of Autodiscover prime-stage domains (e.g., Autodiscover.com[.]br, Autodiscover.com[.]cn, Autodiscover[.]in, etc.) as honeypots, Guardicore explained it was able to accessibility requests to Autodiscover endpoints from different domains, IP addresses, and clientele, netting 96,671 unique credentials despatched from Outlook, mobile email purchasers, and other programs interfacing with Microsoft’s Exchange server above a 4-thirty day period period amongst April 16, 2021, and August 25, 2021.
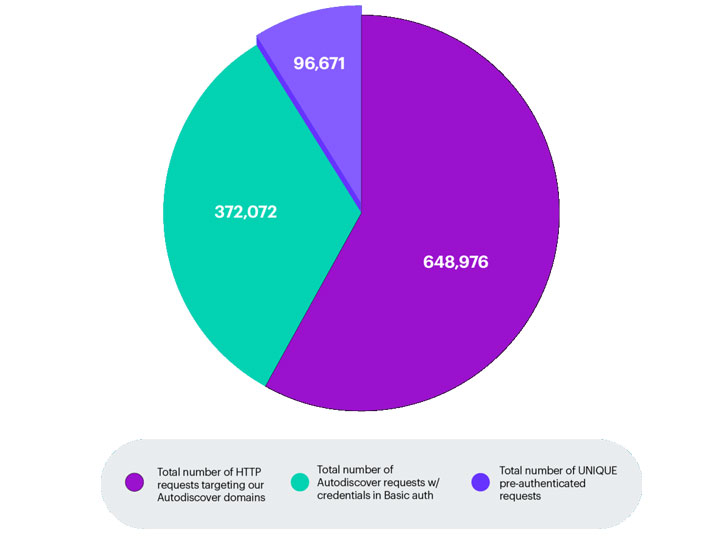
The domains of those people leaked qualifications belonged to many entities from numerous verticals spanning publicly traded firms in China, investment banking institutions, food items brands, electrical power vegetation, and true estate firms, the Boston-based cybersecurity organization noted.
To make matters worse, the scientists formulated an “ol’ switcheroo” attack that involved sending a request to the client to downgrade to a weaker authentication plan (i.e., HTTP Fundamental authentication) in spot of protected approaches like OAuth or NTLM, prompting the email application to send the domain credentials in cleartext.
“Quite often, attackers will try out to bring about customers to ship them their qualifications by applying various tactics, regardless of whether specialized or via social engineering,” Serper claimed. “On the other hand, this incident reveals us that passwords can be leaked exterior of the organization’s perimeter by a protocol that was intended to streamline the IT department’s operations with regards to email consumer configuration without the need of any person from the IT or security office even becoming conscious of it, which emphasises the significance of correct segmentation and Zero Trust.”
Found this article attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to read much more special material we publish.
Some elements of this posting are sourced from:
thehackernews.com

 FamousSparrow APT Wings in to Spy on Hotels, Governments
FamousSparrow APT Wings in to Spy on Hotels, Governments