Microsoft on Friday warned of lively attacks exploiting unpatched Trade Servers carried out by multiple danger actors, as the hacking marketing campaign is believed to have contaminated tens of countless numbers of enterprises, authorities entities in the U.S., Asia, and Europe.
The firm mentioned “it proceeds to see greater use of these vulnerabilities in attacks targeting unpatched methods by numerous destructive actors further than HAFNIUM,” signaling an escalation that the breaches are no for a longer period “limited and qualified” as was previously considered.
In accordance to independent cybersecurity journalist Brian Krebs, at least 30,000 entities throughout the U.S. — primarily small corporations, towns, metropolitan areas, and community governments — have been compromised by an “unusually intense” Chinese group that has set its sights on stealing e-mail from victim businesses by exploiting earlier undisclosed flaws in Exchange Server.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Victims are also getting documented from exterior the U.S., with email techniques belonging to companies in Norway and the Czech Republic impacted in a collection of hacking incidents abusing the vulnerabilities. The Norwegian Countrywide Security Authority claimed it has applied a vulnerability scan of IP addresses in the region to identify vulnerable Trade servers and “continually notify these corporations.”
The colossal scale of the ongoing offensive from Microsoft’s email servers also eclipses the SolarWinds hacking spree that came to light-weight final December, which is stated to have targeted as numerous as 18,000 buyers of the IT administration equipment company. But as it was with the SolarWinds hack, the attackers are most likely to have only absent right after higher-benefit targets primarily based on the first reconnaissance of the victim devices.
Unpatched Exchange Servers at Risk of Exploitation
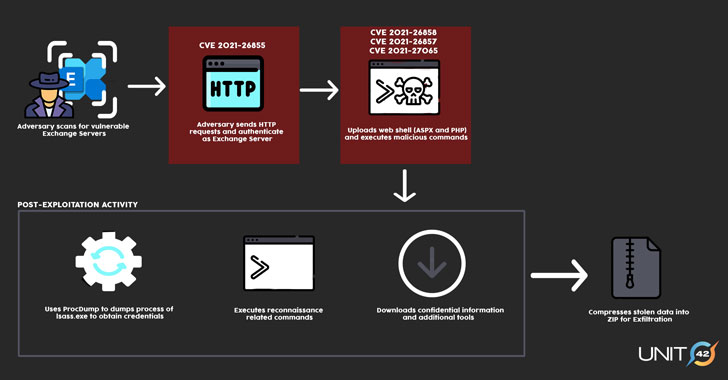
A thriving exploitation of the flaws will allow the adversaries to crack into Microsoft Trade Servers in concentrate on environments and subsequently allow for the installation of unauthorized web-primarily based backdoors to aid extended-time period obtain. With many threat actors leveraging these zero-working day vulnerabilities, the write-up-exploitation routines are expected to vary from just one group to the other based mostly on their motives.
The four security issues in query were being patched by Microsoft as portion of an emergency out-of-band security update very last Tuesday, when warning that “a lot of country-state actors and prison teams will move immediately to consider advantage of any unpatched methods.”
The U.S. Cybersecurity and Infrastructure Security Company (CISA), which released an unexpected emergency directive warning of “energetic exploitation” of the vulnerabilities, urged govt companies working susceptible variations of Exchange Server to both update the computer software or disconnect the products from their networks.
“CISA is aware of popular domestic and global exploitation of Microsoft Exchange Server vulnerabilities and urges scanning Exchange Server logs with Microsoft’s IoC detection device to aid decide compromise,” the company tweeted on March 6.
It’s worth noting that basically putting in the patches issued by Microsoft would have no outcome on servers that have currently been backdoored. Businesses that have been breached to deploy the web shell and other article-exploitation resources carry on to keep on being at risk of long term compromise till the artifacts are entirely rooted out from their networks.
A number of Clusters Spotted
FireEye’s Mandiant threat intelligence crew explained it “noticed multiple occasions of abuse of Microsoft Exchange Server in just at minimum one particular consumer ecosystem” considering that the commence of the calendar year. Cybersecurity agency Volexity, one particular of the companies credited with exploring the flaws, reported the intrusion strategies appeared to have began all over January 6, 2021.
Not a great deal is identified about the identities of the attackers, other than that Microsoft has mainly attributed the exploits with substantial self-confidence to a team it calls Hafnium, a expert government-backed group working out of China. Mandiant is tracking the intrusion action in a few clusters, UNC2639, UNC2640, and UNC2643, adding it expects the quantity to boost as a lot more attacks are detected.
In a assertion to Reuters, a Chinese govt spokesman denied the region was driving the intrusions.
“There are at minimum 5 different clusters of activity that surface to be exploiting the vulnerabilities,” mentioned Katie Nickels, director of menace intelligence at Purple Canary, while noting the discrepancies in the methods and infrastructure from that of the Hafnium actor.
In a person distinct occasion, the cybersecurity organization observed some of the compromised Trade servers had been deployed with a crypto-mining application identified as DLTminer, a malware documented by Carbon Black in 2019.
“One chance is that Hafnium adversaries shared or marketed exploit code, resulting in other groups remaining equipped to exploit these vulnerabilities,” Nickels mentioned. “One more is that adversaries could have reverse engineered the patches unveiled by Microsoft to independently determine out how to exploit the vulnerabilities.”
Microsoft Issues Mitigation Assistance
Microsoft has revealed new alternative mitigation guidance to aid Microsoft Exchange customers who want more time to patch their deployments, in addition to pushing out a new update for the Microsoft Basic safety Scanner (MSERT) software to detect web shells and releasing a script for examining HAFNIUM indicators of compromise. They can be located in this article.
“These vulnerabilities are significant and want to be taken seriously,” Mat Gangwer, senior director of managed threat reaction at Sophos explained. “They allow for attackers to remotely execute instructions on these servers with no the want for qualifications, and any threat actor could potentially abuse them.”
“The wide installation of Trade and its publicity to the internet signify that many corporations operating an on-premises Exchange server could be at risk,” Gangwer included.
Observed this article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to read far more exceptional information we put up.
Some areas of this post are sourced from:
thehackernews.com


 ‘Hundreds of thousands’ of victims in Microsoft Exchange Server attacks
‘Hundreds of thousands’ of victims in Microsoft Exchange Server attacks