The U.S. Cybersecurity and Infrastructure Security Agency is warning of active exploitation makes an attempt that leverage the most up-to-date line of “ProxyShell” Microsoft Trade vulnerabilities that have been patched previously this May perhaps, such as deploying LockFile ransomware on compromised programs.
Tracked as CVE-2021-34473, CVE-2021-34523, and CVE-2021-31207, the vulnerabilities enable adversaries to bypass ACL controls, elevate privileges on the Trade PowerShell backend, efficiently allowing the attacker to complete unauthenticated, remote code execution. Whilst the former two ended up resolved by Microsoft on April 13, a patch for CVE-2021-31207 was transported as aspect of the Windows maker’s May perhaps Patch Tuesday updates.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“An attacker exploiting these vulnerabilities could execute arbitrary code on a vulnerable device,” CISA reported.
The development arrives a minimal more than a 7 days right after cybersecurity scientists sounded the alarm on opportunistic scanning and exploitation of unpatched Trade servers by leveraging the ProxyShell attack chain.
Initially shown at the Pwn2Own hacking contest in April this calendar year, ProxyShell is part of a broader trio of exploit chains uncovered by DEVCORE security researcher Orange Tsai that incorporates ProxyLogon and ProxyOracle, the latter of which concerns two distant code execution flaws that could be employed to recuperate a user’s password in plaintext structure.
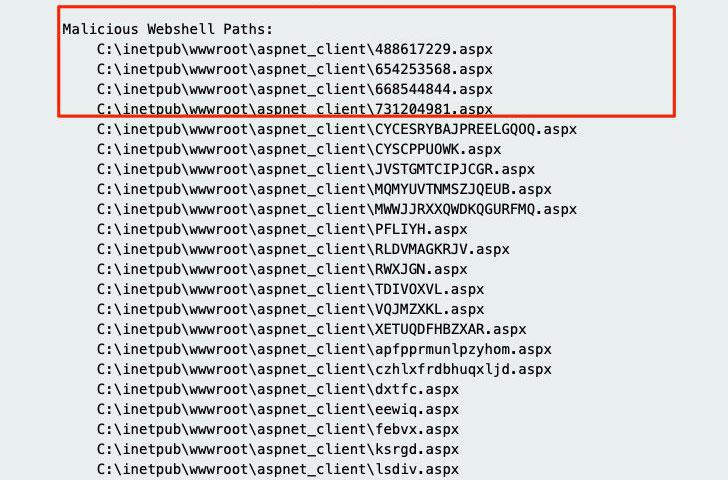
“They’re backdooring bins with webshells that drop other webshells and also executables that periodically phone out,” researcher Kevin Beaumont observed past week.

Now according to scientists from Huntress Labs, at least 5 distinct styles of web shells have been noticed as deployed to vulnerable Microsoft Exchange servers, with above about 100 incidents reported associated to the exploit among August 17 and 18. Web shells grant the attackers distant entry to the compromised servers, but it is just not distinct precisely what the goals are or the extent to which all the flaws have been utilised.
Far more than 140 web shells have been detected across no less than 1,900 unpatched Exchanger servers to date, Huntress Labs CEO Kyle Hanslovan tweeted, adding “impacted [organizations] hence considerably consist of setting up producing, seafood processors, industrial equipment, auto repair service retailers, a smaller household airport and a lot more.”
Uncovered this write-up fascinating? Follow THN on Facebook, Twitter and LinkedIn to browse a lot more unique content we article.
Some sections of this short article are sourced from:
thehackernews.com


 NYC Teachers’ Social Security Numbers Exposed
NYC Teachers’ Social Security Numbers Exposed