Microsoft’s 365 Defender Exploration Crew has comprehensive the most recent pressure of phishing attacks created to focus on the nascent technology underpinning Web3 – the so-called decentralised third generation of the internet.
Dubbed ‘ice phishing’, the attack strategy entails hijacking the regular approval course of action that handles the protected transaction of tokens, these kinds of as cryptocurrency, more than a blockchain.
Ice phishing was 1st observed by Microsoft concerning November and December 2021 when the Badger DAO system was hacked and $121 million worth of users’ belongings were being stolen.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Badger DAO is a system that enables people to deposit Bitcoin and generate curiosity on their deposits applying a variety of yield farming procedures. It takes advantage of a decentralised finance (DeFi) protocol named Badger and at this time has $978 million full volume locked, according to Microsoft.
The Ethereum blockchain, on which the Badger DAO attack occured, hosts cryptocurrencies that use the ERC-20 conventional to create and issue clever contracts that can be then utilised to securely transfer belongings over the blockchain.
This standard can be found as a established of functions that, when executed, facilitate a blockchain transaction. One particular of these features is to initiate a clever deal that moves belongings on behalf of the user.
The owner of the asset is instantly accredited to make the transaction but they can also delegate acceptance to additional entities this kind of as wise contracts. It truly is this procedure that ice phishing aims to exploit.
How ice phishing performs
Historical techniques of thieving assets from secured cryptocurrency wallets have typically relied on social engineering to deceive end users into relinquishing their non-public keys to the attacker, enabling them to entry their wallet and drain the cash.
Ice phishing does not include thieving a user’s non-public keys. As an alternative, it will involve tricking a user into signing a transaction that delegates approval of the user’s tokens to the attacker.
In the case of the Badger DAO attack, the platform’s front-close infrastructure was compromised which permitted the attacker to inject malicious code into the Badger smart deal front finish. This code asked for end users to sign transactions granting ERC-20 approvals to the attacker’s account.
As is normally the scenario with these sorts of platforms, the user interface (UI) for Badger DAO does not clearly show more than enough info to suggest no matter whether a transaction has been tampered with, in accordance to Microsoft.
Attackers both equally compromise these platforms’ infrastructures and leverage the fundamental UI to fool consumers into granting transaction approval to the attacker’s wallet.
Microsoft
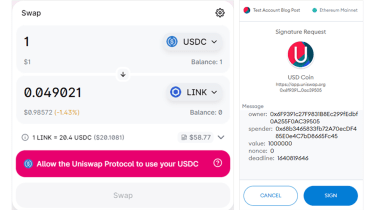
Working with a transaction on the Uniswap system – a decentralised token exchange letting customers to swap Ethereum-dependent cryptocurrency tokens for other tokens – as an instance, Microsoft showed the common UI introduced to the consumer, and how the information necessary to establish if a transaction has been tampered with is commonly concealed.
In the earlier mentioned case in point, the user isn’t in a position to identify if the ‘spender’ – the account to be authorised – is the router owned by the platform or an deal with owned by an attacker.
“Once the acceptance transaction has been signed, submitted, and mined, the spender can entry the resources,” stated Microsoft. “In situation of an ice phishing attack, the attacker can accumulate approvals more than a time period of time and then drain all victim’s wallets rapidly.
“This is accurately what happened with the Badger DAO attack that enabled the attacker to drain tens of millions of US pounds in November-December 2021.”
Long term Web3 challenges
Microsoft claimed the Web3 stack is even now in its infancy and as such, bears pitfalls for end users. The Badger DAO attack was considerable and a single of the largest hacks of its sort in conditions of the amount of assets stolen.
Attacks like these are likely to continue, said Microsoft, although transactions of this sort, on the blockchain, are public which will make investigating the incidents simpler.
Pinpointing these kinds of attacks is achievable and can even be automatic. A public blockchain also makes it possible for investigators to see how substantially has been stolen – a little something that is typically tough in regular, web2-dependent phishing attacks.
Some areas of this write-up are sourced from:
www.itpro.co.uk


 Google Bringing Privacy Sandbox to Android to Limit Sharing of User Data
Google Bringing Privacy Sandbox to Android to Limit Sharing of User Data