Microsoft has produced a new ransomware detection aspect for Azure that works by using device finding out to place possible attacks.
‘Fusion Detection for Ransomware’ will mail an alert to buyers when it observes steps that are “perhaps associated with ransomware functions”.
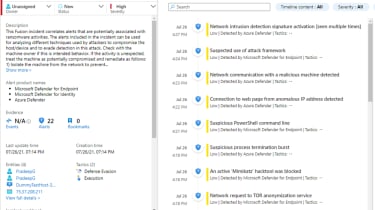
The alerts will inform customers of what was detected, and on which device, with the method correlating knowledge from other Azure products and services, these as Azure Defender, Microsoft Defender for Endpoint, Microsoft Defender for Identity, Microsoft Cloud Application Security, and Azure Sentinel scheduled analytics policies.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
At the time ransomware activities are detected and correlated by the Fusion’s device mastering product, a substantial severity incident with the label “Multiple alerts possibly linked to Ransomware action detected” will be brought on in the customer’s Azure Sentinel workspace (revealed in the impression down below).
Just after an inform has been despatched, Microsoft recommends end users test the product/host in question to see if its behaviour is “unforeseen”. If so, the user should really deal with the machine as “likely compromised” and take fast steps, these kinds of as isolating the device from the network, jogging complete anti-virus scans, and investigating the relaxation of the network for comparable signs.
Ransomware has turn into a lucrative occupation, in accordance to a modern report from Device 42, with ordinary payouts almost doubling more than the past calendar year. Given that 2020, payouts for successful ransomware attacks have amplified 82% to a file $570,000 in the 1st 50 percent of 2021. The improve adopted the past year’s 171% bounce to more than $312,000.
“Protecting against such attacks in the initial position would be the excellent option but with the new pattern of ‘ransomware as a service’ and human operated ransomware, the scope and the sophistication of attacks are escalating – attackers are making use of sluggish and stealth strategies to compromise network, which will make it more challenging to detect them in the initial location,” Microsoft security researcher Sylvie Liu wrote in a weblog submit.
Some elements of this article are sourced from:
www.itpro.co.uk


 Hackers Exploiting New Auth Bypass Bug Affecting Millions of Arcadyan Routers
Hackers Exploiting New Auth Bypass Bug Affecting Millions of Arcadyan Routers