The huge state-sponsored espionage campaign that compromised program maker SolarWinds also specific Microsoft, as the unfolding investigation into the hacking spree reveals the incident may well have been significantly additional wider in scope, sophistication, and effects than beforehand thought.
Information of Microsoft’s compromise was 1st claimed by Reuters, which also claimed Microsoft’s individual merchandise were being then utilized to strike other victims by leveraging its cloud choices, citing persons acquainted with the make any difference.
The Windows maker, nonetheless, denied the danger actor had infiltrated its output systems to phase further attacks from its customers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In a statement to The Hacker News through email, the enterprise mentioned —
“Like other SolarWinds buyers, we have been actively searching for indicators of this actor and can validate that we detected malicious SolarWinds binaries in our natural environment, which we isolated and removed. We have not uncovered evidence of obtain to manufacturing expert services or customer data. Our investigations, which are ongoing, have found totally no indications that our methods have been utilized to attack some others.”
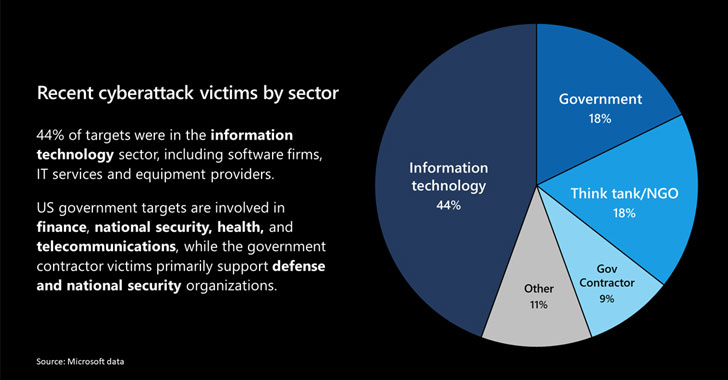
Characterizing the hack as “a instant of reckoning,” Microsoft president Brad Smith reported it has notified about 40 customers found in Belgium, Canada, Israel, Mexico, Spain, the UAE, the UK, and the US that were singled out by the attackers. 44% of the victims are in the information and facts technology sector, like software package companies, IT providers, and products companies.
CISA Issues New Advisory
The development will come as the US Cybersecurity and Infrastructure Security Company (CISA) released a new advisory, stating the “APT actor [behind the compromises] has demonstrated patience, operational security, and advanced tradecraft in these intrusions.”
“This threat poses a grave risk to the Federal Govt and condition, area, tribal, and territorial governments as very well as critical infrastructure entities and other private sector businesses,” it additional.
But in a twist, the company also stated it discovered more preliminary an infection vectors, other than the SolarWinds Orion platform, that have been leveraged by the adversary to mount the attacks, which includes a formerly stolen vital to circumvent Duo’s multi-factor authentication (MFA) to obtain the mailbox of a user by using Outlook Web App (OWA) support.
Digital forensics firm Volexity, which tracks the actor beneath the moniker Dark Halo, stated the MFA bypass was a single of the 3 incidents among late 2019 and 2020 aimed at a US-based believe tank.
The overall intrusion marketing campaign came to light before this 7 days when FireEye disclosed it experienced detected a breach that also pilfered its Red Crew penetration screening resources.
Considering that then, a variety of companies have been located to be attacked, including the US departments of Treasury, Commerce, Homeland Security, and Strength, the Countrywide Nuclear Security Administration (NNSA), and quite a few condition department networks.
Even though many aspects keep on to stay unclear, the revelation about new modes of attack raises extra questions about the stage of obtain the attackers were in a position to get throughout governing administration and corporate devices worldwide.
Microsoft, FireEye, and GoDaddy Generate a Killswitch
Above the final handful of times, Microsoft, FireEye, and GoDaddy seized command around just one of the key GoDaddy domains — avsvmcloud[.]com — that was utilised by the hackers to converse with the compromised units, reconfiguring it to create a killswitch that would protect against the SUNBURST malware from continuing to function on victims’ networks.
For its section, SolarWinds has not yet disclosed how particularly the attacker managed to obtain in depth accessibility to its systems to be able to insert malware into the company’s genuine software program updates.
Recent evidence, having said that, factors to a compromise of its make and software package launch technique. An estimated 18,000 Orion consumers are reported to have downloaded the updates containing the back again door.
The hacks are believed to be the function of APT29, a Russian menace team also recognised as Cozy Bear, which has been linked to a series of breaches of critical US infrastructure above the earlier calendar year.
The most up-to-date slew of intrusions has also led CISA, the US Federal Bureau of Investigation (FBI), and the Office environment of the Director of Countrywide Intelligence (ODNI) to issue a joint statement, stating the businesses are gathering intelligence in purchase to attribute, go after, and disrupt the responsible menace actors.
Calling for more powerful techniques to keep nation-states accountable for cyberattacks, Smith claimed the attacks symbolize “an act of recklessness that designed a major technological vulnerability for the United States and the earth.”
“In outcome, this is not just an attack on particular targets, but on the have confidence in and reliability of the world’s critical infrastructure in buy to progress 1 nation’s intelligence agency,” he included.
Uncovered this short article exciting? Adhere to THN on Facebook, Twitter and LinkedIn to go through much more exclusive content we put up.
Some components of this write-up are sourced from:
thehackernews.com


 Nuclear Weapons Agency Hacked in Widening Cyberattack – Report
Nuclear Weapons Agency Hacked in Widening Cyberattack – Report