Microsoft on Monday introduced the seizure of 42 domains employed by a China-based cyber espionage group that established its sights on corporations in the U.S. and 28 other international locations pursuant to a lawful warrant issued by a federal courtroom in the U.S. state of Virginia.
The Redmond corporation attributed the malicious functions to a team it pursues as Nickel, and by the wider cybersecurity business beneath the monikers APT15, Bronze Palace, Ke3Chang, Mirage, Playful Dragon, and Vixen Panda. The innovative persistent risk (APT) actor is thought to have been active considering the fact that at the very least 2012.
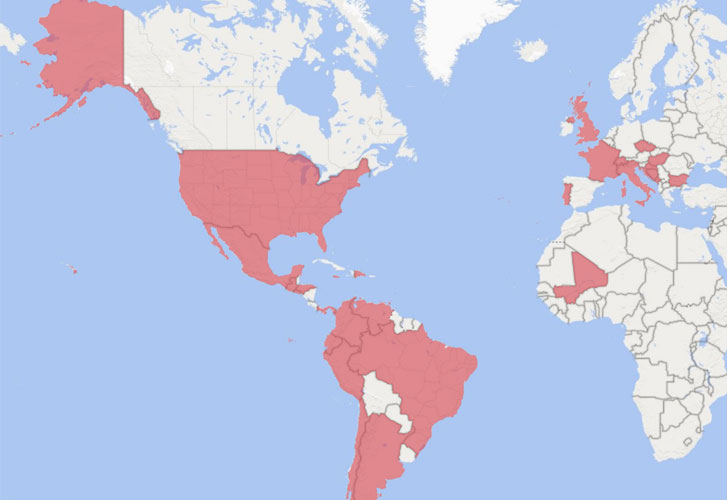
“Nickel has targeted organizations in both of those the private and community sectors, like diplomatic organizations and ministries of foreign affairs in North The us, Central America, South The usa, the Caribbean, Europe and Africa,” Microsoft’s Company Vice President for Customer Security and Have faith in, Tom Burt, said. “There is often a correlation amongst Nickel’s targets and China’s geopolitical pursuits.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The rogue infrastructure enabled the hacking crew to retain prolonged-expression accessibility to the compromised devices and execute attacks for intelligence collecting applications focusing on unnamed authorities agencies, assume tanks, and human legal rights corporations as part of a digital espionage marketing campaign relationship back to September 2019.
Microsoft painted the cyber assaults as “remarkably advanced” that utilized a multitude of techniques, which includes breaching remote obtain companies and exploiting vulnerabilities in unpatched VPN appliances as very well as Trade Server and SharePoint devices to “insert tough-to-detect malware that facilitates intrusion, surveillance and data theft.”
Upon attaining an preliminary foothold, Nickel has been found deploying credential dumping instruments and stealers this sort of as Mimikatz and WDigest to hack into target accounts, adopted by offering custom made malware that authorized the actor to preserve persistence on target networks in excess of extended periods of time and perform regularly scheduled exfiltration of documents, execute arbitrary shellcode, and obtain emails from Microsoft 365 accounts utilizing compromised qualifications.
The multiple backdoor families applied for command and command are staying tracked as Neoichor, Leeson, NumbIdea, NullItch, and Rokum.

The most recent wave of attacks provides to an extensive listing of surveillanceware campaigns mounted by the APT15 group in new yrs. In July 2020, cellular security company Lookout disclosed 4 trojanized respectable applications — named SilkBean, DoubleAgent, CarbonSteal, and GoldenEagle — that focused the Uyghur ethnic minority and the Tibetan group with the purpose of collecting and transmitting own user info to adversary-operated command-and-manage servers.
“As China’s impact around the planet carries on to improve and the nation establishes bilateral relations with far more countries and extends partnerships in assistance of China’s Belt and Road Initiative, we evaluate that China-centered threat actors will go on to target customers in govt, diplomatic, and NGO sectors to attain new insights, probable in pursuit of economic espionage or regular intelligence assortment goals,” Microsoft said.
Observed this article appealing? Follow THN on Fb, Twitter and LinkedIn to browse extra special content we write-up.
Some components of this write-up are sourced from:
thehackernews.com


 Latest Firefox 95 Includes RLBox Sandboxing to Protect Browser from Malicious Code
Latest Firefox 95 Includes RLBox Sandboxing to Protect Browser from Malicious Code