Microsoft on Friday shared far more of the practices, tactics, and methods (TTPs) adopted by the Russia-primarily based Gamaredon hacking group to aid a barrage of cyber espionage attacks aimed at various entities in Ukraine over the earlier six months.
The attacks are reported to have singled out governing administration, military services, non-federal government organizations (NGO), judiciary, regulation enforcement, and non-profit organizations with the main objective of exfiltrating sensitive info, retaining obtain, and leveraging it to shift laterally into connected companies.
The Windows maker’s Danger Intelligence Centre (MSTIC) is monitoring the cluster underneath the moniker ACTINIUM (beforehand as DEV-0157), sticking to its custom of figuring out country-point out routines by chemical aspect names.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Ukrainian authorities, in November 2021, publicly attributed Gamaredon to the Russian Federal Security Services (FSB) and related its functions to the FSB Place of work of Russia in the Republic of Crimea and the city of Sevastopol.

“Given that October 2021, ACTINIUM has focused or compromised accounts at companies critical to emergency reaction and ensuring the security of Ukrainian territory, as very well as corporations that would be concerned in coordinating the distribution of worldwide and humanitarian help to Ukraine in a crisis,” MSTIC scientists stated.
It’s well worth pointing out that the Gamaredon threat group represents a exclusive established of attacks divorced from last month’s cyber offensives that knocked out multiple Ukraine government agencies and corporate entities with destructive information-wiping malware disguised as ransomware.
The attacks largely leverage spear-phishing e-mails as an first access vector, with the messages carrying malware-laced macro attachments that use distant templates made up of malicious code when the recipients open up the rigged documents.
In an exciting tactic, the operators also embed a monitoring pixel-like “web bug” within the physique of the phishing message to monitor if a information has been opened, adhering to which, the an infection chain triggers a multi-stage course of action that culminates in the deployment of various binaries, which includes —
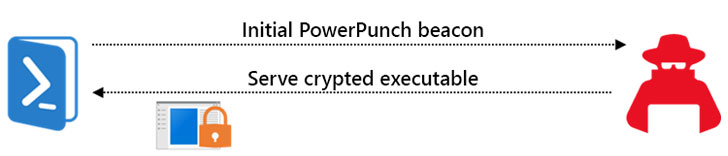
- PowerPunch – A PowerShell-based mostly dropper and downloader utilised to retrieve the upcoming-stage executables remotely
- Pterodo – A constantly evolving feature-wealthy backdoor that also sports a vary of abilities supposed to make evaluation much more complicated, and
- QuietSieve – A seriously-obfuscated .NET binary specifically geared toward information exfiltration and reconnaissance on the concentrate on host
“Though the QuietSieve malware spouse and children is mainly geared to the exfiltration of data from the compromised host, it can also acquire and execute a remote payload from the operator,” the researchers discussed, even though also contacting out its ability to acquire screenshots of the compromised host about each individual 5 minutes.
This is significantly from the only intrusion staged by the danger actor, which also struck an unnamed Western government organization in Ukraine very last thirty day period by way of a malware-laced resume for an active job listing with the entity posted on a nearby position portal. It also focused the country’s Condition Migration Provider (SMS) in December 2021.
The conclusions also get there as Cisco Talos, in its continuing investigation of the January incidents, disclosed details of an ongoing disinformation campaign making an attempt to attribute the defacement and wiper attacks to Ukrainian groups that day back at least nine months.
Discovered this short article exciting? Observe THN on Fb, Twitter and LinkedIn to examine more special content material we article.
Some parts of this article are sourced from:
thehackernews.com



 ‘Long Live Log4Shell’: CVE-2021-44228 Not Dead Yet
‘Long Live Log4Shell’: CVE-2021-44228 Not Dead Yet