New proof amidst the ongoing probe into the espionage campaign concentrating on SolarWinds has uncovered an unsuccessful attempt to compromise cybersecurity firm Crowdstrike and access the company’s email.
The hacking endeavor was reported to the corporation by Microsoft’s Danger Intelligence Center on December 15, which identified a 3rd-party reseller’s Microsoft Azure account to be producing “irregular calls” to Microsoft cloud APIs in the course of a 17-hour period of time numerous months back.
The undisclosed affected reseller’s Azure account handles Microsoft Workplace licensing for its Azure customers, together with CrowdStrike.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
While there was an endeavor by unidentified menace actors to study email, it was finally foiled as the company does not use Microsoft’s Business office 365 email services, CrowdStrike mentioned.
The incident arrives in the wake of the provide chain attack of SolarWinds unveiled previously this month, resulting in the deployment of a covert backdoor (aka “Sunburst”) by means of destructive updates of a network checking software package identified as SolarWinds Orion.
Considering the fact that the disclosure, Microsoft, Cisco, VMware, Intel, NVIDIA, and a quantity of US government organizations have confirmed discovering tainted Orion installations in their environments.
The enhancement comes a 7 days right after the Windows maker, by itself a SolarWinds purchaser, denied hackers had infiltrated its production systems to phase additional attacks in opposition to its end users and discovered proof of a different hacking team abusing Orion software to put in a different backdoor known as “Supernova.”
It also coincides with a new report from The Washington Publish currently, which alleges Russian government hackers have breached Microsoft cloud consumers and stolen e-mails from at minimum 1 personal-sector corporation by getting gain of a Microsoft reseller that manages cloud-accessibility services.
We have arrived at out to Microsoft, and we will update the story if we hear back again.
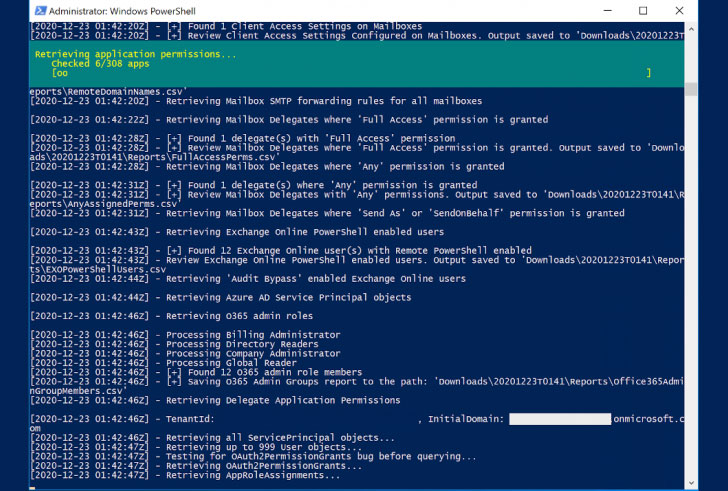
CrowdStrike has also unveiled CrowdStrike Reporting Tool for Azure (CRT), a absolutely free tool that aims to enable companies evaluate abnormal permissions in their Azure Lively Listing or Business office 365 environments and assist establish configuration weaknesses.
In addition, the US Cybersecurity Infrastructure and Security Company (CISA) has independently made a similar open up-source utility identified as Sparrow to help detect achievable compromised accounts and apps in Azure or Business 365 environments.
“The tool is intended for use by incident responders and is narrowly targeted on exercise that is endemic to the new identification- and authentication-dependent attacks witnessed in a number of sectors,” CISA claimed.
For its portion, SolarWinds has up to date its security advisory, urging prospects to update Orion Platform program to model 2020.2.1 HF 2 or 2019.4 HF 6 to mitigate the challenges affiliated with Sunburst and Supernova vulnerabilities.
Identified this posting interesting? Adhere to THN on Facebook, Twitter and LinkedIn to study extra exclusive content we post.
Some parts of this posting are sourced from:
thehackernews.com


 Attackers Abusing Citrix NetScaler Devices to Launch Amplified DDoS Attacks
Attackers Abusing Citrix NetScaler Devices to Launch Amplified DDoS Attacks