Microsoft has opened the lid on a massive-scale phishing-as-a-company (PHaaS) operation that is included in selling phishing kits and email templates as very well as furnishing hosting and automatic companies at a small charge, consequently enabling cyber actors to purchase phishing campaigns and deploy them with minimal initiatives.
“With more than 100 offered phishing templates that mimic recognized brand names and products and services, the BulletProofLink operation is responsible for numerous of the phishing campaigns that impression enterprises currently,” Microsoft 365 Defender Menace Intelligence Staff mentioned in a Tuesday report.
“BulletProofLink (also referred to as BulletProftLink or Anthrax by its operators in several sites, ads, and other advertising resources) is applied by several attacker groups in both a single-off or month-to-month membership-based mostly business enterprise products, generating a constant earnings stream for its operators.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
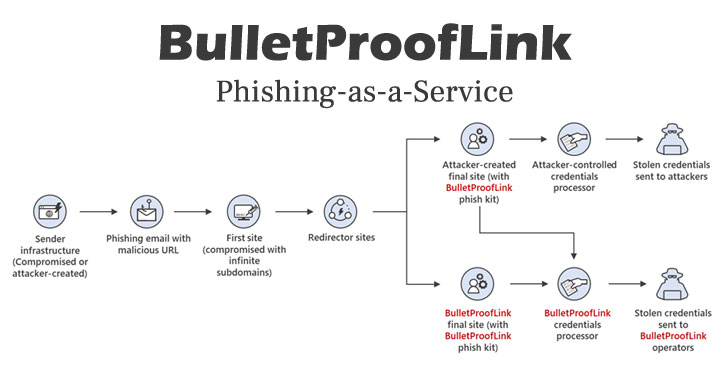
The tech large said it uncovered the procedure during its investigation of a credential phishing marketing campaign that utilised the BulletProofLink phishing package on either on attacker-managed sites or web pages presented by BulletProofLink as aspect of their service. The existence of the operation was initially produced community by OSINT Supporters in October 2020.
Phishing-as-a-service differs from common phishing kits in that unlike the latter, which are bought as a person-time payments to gain entry to packaged information that contains prepared-to-use email phishing templates, they are membership-primarily based and follow a software package-as-a-company product, whilst also growing on the capabilities to involve designed-in web page hosting, email shipping, and credential theft.
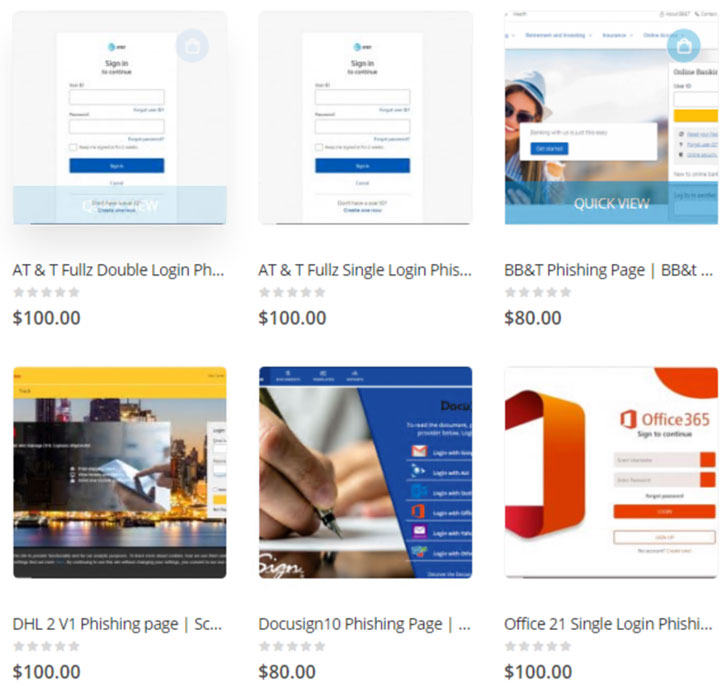
Considered to have been active since at minimum 2018, BulletProofLink is acknowledged to operate an on-line portal to advertise their toolset for as considerably as $800 a thirty day period and enable cybercrime gangs to register and spend for the services. Consumers can also avail of a 10% low cost ought to they decide to subscribe to their newsletter, not to point out pay out everywhere in between $80 to $100 for credential phishing templates that let them to steal credentials entered by unsuspected victims upon clicking a destructive URL in the email concept.

Troublingly, the stolen credentials are not only sent to the attackers but also to the BulletProofLink operators utilizing a system identified as “double theft” in a modus operandi that mirrors the double extortion attacks used by ransomware gangs.
“With phishing kits, it is trivial for operators to involve a secondary place for qualifications to be sent to and hope that the purchaser of the phish package does not alter the code to get rid of it,” the scientists mentioned. “This is accurate for the BulletProofLink phishing kit, and in conditions exactly where the attackers employing the company gained credentials and logs at the conclude of a week rather of conducting strategies them selves, the PhaaS operator preserved management of all qualifications they resell.”
Observed this write-up interesting? Stick to THN on Fb, Twitter and LinkedIn to study far more unique written content we post.
Some components of this report are sourced from:
thehackernews.com

 How Cynet’s Response Automation Helps Organizations Mitigate Cyber Threats
How Cynet’s Response Automation Helps Organizations Mitigate Cyber Threats