Microsoft on Wednesday mentioned it remediated a vulnerability in its Azure Container Scenarios (ACI) solutions that could have been exploited by a malicious actor “to obtain other customers’ data” in what the researcher described as the “initial cross-account container takeover in the public cloud.”
An attacker exploiting the weak spot could execute destructive instructions on other users’ containers, steal buyer strategies and visuals deployed to the system. The Windows maker did not share any extra particulars linked to the flaw, save that afflicted clients “revoke any privileged credentials that were being deployed to the system prior to August 31, 2021.”
Azure Container Circumstances is a managed provider that lets users to run Docker containers straight in a serverless cloud setting, without the need of demanding the use of virtual devices, clusters, or orchestrators.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
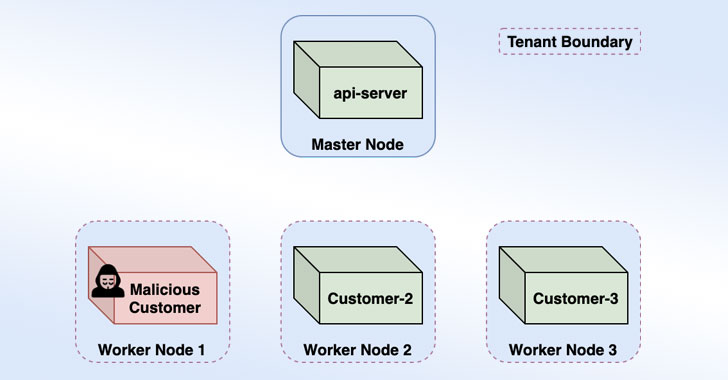
Palo Alto Networks’ Unit 42 risk intelligence crew dubbed the vulnerability “Azurescape,” referring to how an attacker can leverage the cross-tenant technique to escape their rogue ACI container, escalate privileges around a multitenant Kubernetes cluster, and just take regulate of impacted containers by executing malicious code.
Breaking out of the container, the researchers reported, was created attainable thanks to an out-of-date container runtime employed in ACI (runC v1..-rc2), thus generating it feasible to exploit CVE-2019-5736 (CVSS score: 8.6) to escape the container and get code execution with elevated privileges on the underlying host.
Microsoft claimed it notified find clients with containers working on the very same Kubernetes cluster as that of the destructive container created by Palo Alto Networks to show the attack. The cluster is claimed to have hosted 100 consumer pods and about 120 nodes, with the organization stating it had no proof undesirable actors experienced abused the flaw to carry out authentic-planet intrusions, adding its investigation “surfaced no unauthorized entry to client info.”
The disclosure is the next Azure-similar flaw to occur to mild in a span of two months, the 1st one staying a critical Cosmos database flaw that could have been probably exploited to grant any Azure consumer entire admin obtain to other customers’ databases occasions devoid of any authorization.
“This discovery highlights the need for cloud users to acquire a ‘defense-in-depth’ technique to securing their cloud infrastructure that involves ongoing checking for threats — inside of and exterior the cloud platform,” Device 42 scientists Ariel Zelivanky and Yuval Avrahami explained. “Discovery of Azurescape also underscores the need for cloud service vendors to supply sufficient accessibility for outside scientists to review their environments, looking for mysterious threats.”
Observed this write-up fascinating? Abide by THN on Fb, Twitter and LinkedIn to examine much more unique written content we post.
Some pieces of this posting are sourced from:
thehackernews.com

 Thousands of Fortinet VPN Account Credentials Leaked
Thousands of Fortinet VPN Account Credentials Leaked