Microsoft on Monday revealed new malware deployed by the hacking team behind the SolarWinds supply chain attack past December to provide further payloads and steal sensitive information and facts from Active Listing Federation Products and services (Advert FS) servers.
The tech giant’s Menace Intelligence Heart (MSTIC) codenamed the “passive and hugely qualified backdoor” FoggyWeb, building it the threat actor tracked as Nobelium’s newest tool in a extended checklist of cyber weaponry these as Sunburst, Sunspot, Raindrop, Teardrop, GoldMax, GoldFinder, Sibot, Flipflop, NativeZone, EnvyScout, BoomBox, and VaporRage.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
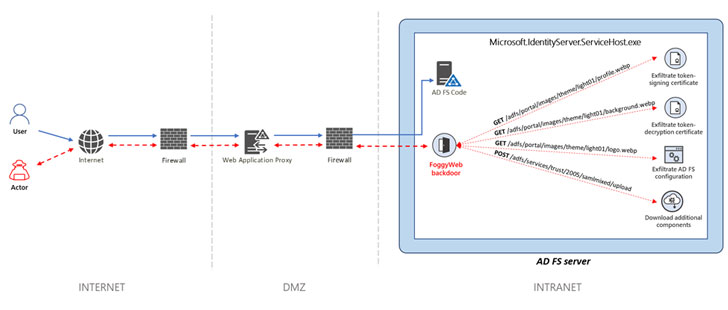
“The moment Nobelium obtains qualifications and successfully compromises a server, the actor relies on that access to preserve persistence and deepen its infiltration working with advanced malware and applications,” MSTIC scientists stated. “Nobelium takes advantage of FoggyWeb to remotely exfiltrate the configuration databases of compromised Advertisement FS servers, decrypted token-signing certification, and token-decryption certification, as properly as to obtain and execute supplemental parts.”
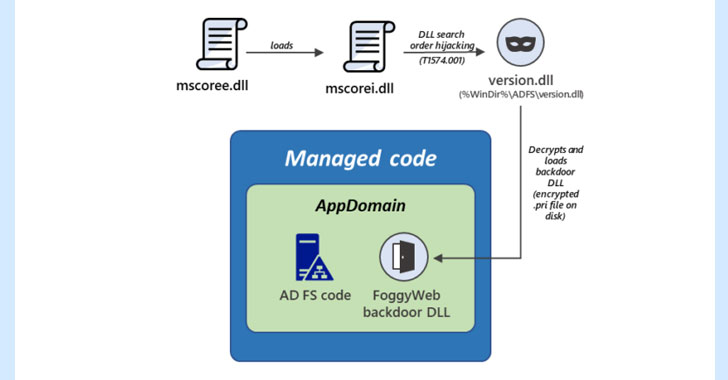
Microsoft stated it observed FoggyWeb in the wild as early as April 2021, describing the implant as a “malicious memory-resident DLL.”
Nobelium is the moniker assigned by the corporation to the nation-state hacking team greatly identified as APT29, The Dukes, or Cozy Bear — an highly developed persistent threat that has been attributed to Russia’s Foreign Intelligence Support (SVR) — and considered to have been behind the large-ranging attack targeting SolarWinds that arrived to mild in December 2020. The adversary guiding this marketing campaign is also currently being monitored less than a assortment of codenames like UNC2452 (FireEye), SolarStorm (Unit 42), StellarParticle (CrowdStrike), Dark Halo (Volexity), and Iron Ritual (Secureworks).

FoggyWeb, installed using a loader by exploiting a system identified as DLL lookup purchase hijacking, is able of transmitting sensitive details from a compromised Advertisement FS server as well as get and execute supplemental destructive payloads retrieved from a distant attacker-managed server. It is really also engineered to keep an eye on all incoming HTTP GET and Write-up requests sent to the server from the intranet (or internet) and intercept HTTP requests that are of fascination to the actor.
“Protecting Ad FS servers is vital to mitigating Nobelium attacks,” the scientists claimed. “Detecting and blocking malware, attacker activity, and other malicious artifacts on Ad FS servers can split critical techniques in acknowledged Nobelium attack chains. Buyers should really evaluate their Ad FS Server configuration and put into practice adjustments to safe these systems from attacks.”
Located this report interesting? Comply with THN on Facebook, Twitter and LinkedIn to browse extra exclusive information we write-up.
Some sections of this article are sourced from:
thehackernews.com

 Computer Scientist Jailed Over Dark Web Conspiracy
Computer Scientist Jailed Over Dark Web Conspiracy