Microsoft has warned of rising threats in the Web3 landscape, together with “ice phishing” strategies, as a surge in adoption of blockchain and DeFi systems emphasizes the need to create security into the decentralized web whilst it’s continue to in its early phases.
The firm’s Microsoft 365 Defender Exploration Workforce termed out various new avenues by way of which destructive actors may attempt to trick cryptocurrency users into supplying up their non-public cryptographic keys and have out unauthorized fund transfers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“1 facet that the immutable and public blockchain allows is comprehensive transparency, so an attack can be noticed and examined following it transpired,” Christian Seifert, principal investigate manager at Microsoft’s Security and Compliance group, mentioned. “It also allows assessment of the economical impact of attacks, which is complicated in traditional web2 phishing attacks.”
The theft of the keys could be carried out in numerous methods, like impersonating wallet software program, deploying malware on victims’ gadgets, typosquatting genuine intelligent agreement entrance finishes, and minting rogue electronic tokens for Airdrop ripoffs.
Yet another approach includes what Microsoft calls “ice phishing.” Relatively than thieving a user’s non-public keys, the method works by deceiving the target into “signing a transaction that delegates acceptance of the user’s tokens to the attacker.”
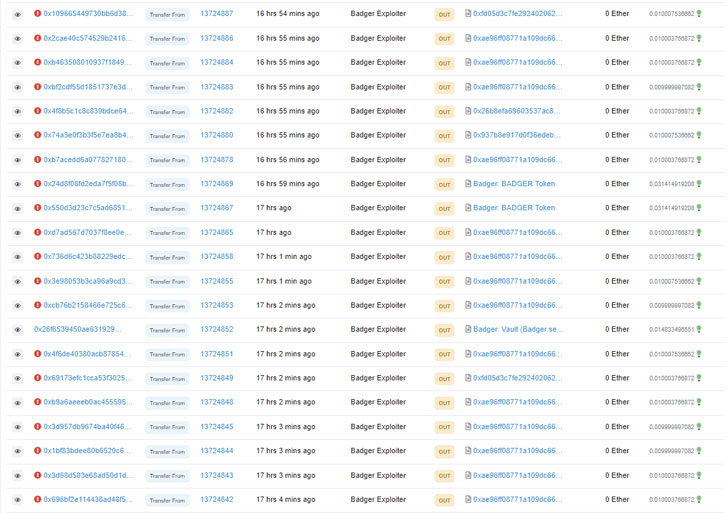
“Once the acceptance transaction has been signed, submitted, and mined, the spender can entry the funds,” Seifert elaborated. “In situation of an ‘ice phishing’ attack, the attacker can accumulate approvals in excess of a period of time of time and then drain all [the] victim’s wallets quickly.”
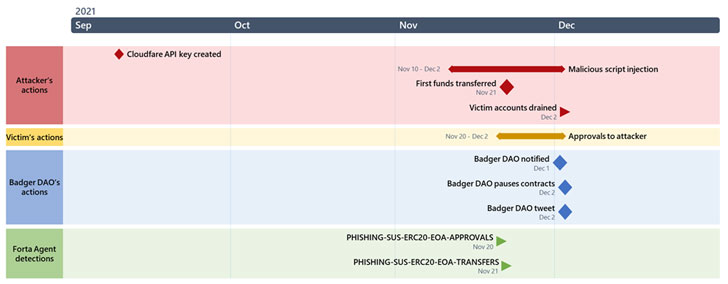
The significant-profile hack of DeFi system BadgerDAO, which arrived to mild in early December 2021, was 1 such occasion of ice phishing, whereby a maliciously injected snippet applying a compromised API essential enabled the adversary to siphon $121 million in cash.
“The attacker deployed the employee script by way of a compromised API critical that was produced without the need of the expertise or authorization of Badger engineers,” BadgerDAO said. “The attacker(s) made use of this API obtain to periodically inject malicious code into the Badger application these that it only impacted a subset of the user foundation.”
The script was programmed this kind of that it would intercept Web3 transactions from wallets around a specific balance and insert a ask for to transfer the victim’s tokens to an handle preferred by the attackers.
To mitigate threats influencing the blockchain technology, Microsoft is recommending people to evaluation and audit the clever contracts for suitable incident reaction or unexpected emergency abilities and periodically reassess and revoke token allowances.
Located this write-up fascinating? Abide by THN on Fb, Twitter and LinkedIn to study a lot more exceptional written content we write-up.
Some sections of this posting are sourced from:
thehackernews.com


 PseudoManuscrypt Malware Spreading the Same Way as CryptBot Targets Koreans
PseudoManuscrypt Malware Spreading the Same Way as CryptBot Targets Koreans