An notorious cross-platform crypto-mining malware has ongoing to refine and boost upon its procedures to strike both equally Windows and Linux running techniques by environment its sights on more mature vulnerabilities, when simultaneously latching on to a selection of spreading mechanisms to improve the performance of its strategies.
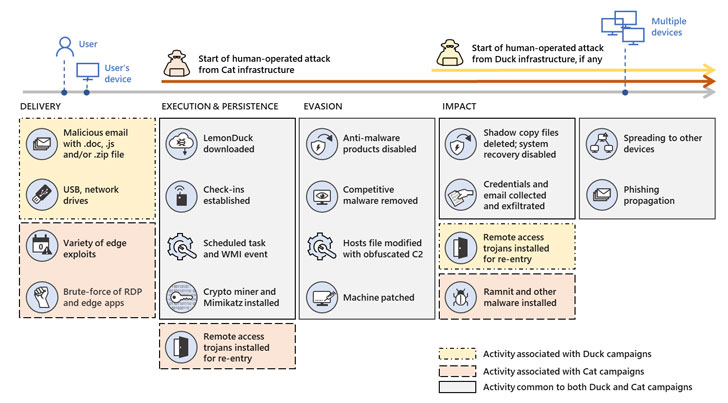
“LemonDuck, an actively updated and sturdy malware that’s mainly regarded for its botnet and cryptocurrency mining aims, adopted the very same trajectory when it adopted much more sophisticated habits and escalated its functions,” Microsoft mentioned in a technical produce-up released last 7 days. “These days, beyond working with means for its regular bot and mining routines, LemonDuck steals qualifications, removes security controls, spreads by way of e-mail, moves laterally, and finally drops more instruments for human-operated exercise.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The malware is notorious for its means to propagate quickly across an infected network to aid details theft and change the machines into cryptocurrency mining bots by diverting their computing assets to illegally mine cryptocurrency. Notably, LemonDuck functions as a loader for stick to-on attacks that entail credential theft and the set up of up coming-stage implants that could act as a gateway to a variety of destructive threats, such as ransomware.
LemonDuck’s functions ended up 1st noticed in China in May well 2019, prior to it started adopting COVID-19-themed lures in email attacks in 2020 and even the recently resolved “ProxyLogon” Trade Server flaws to acquire access to unpatched programs. One more tactic of be aware is its means to erase “other attackers from a compromised unit by getting rid of competing malware and protecting against any new infections by patching the identical vulnerabilities it made use of to acquire access.”

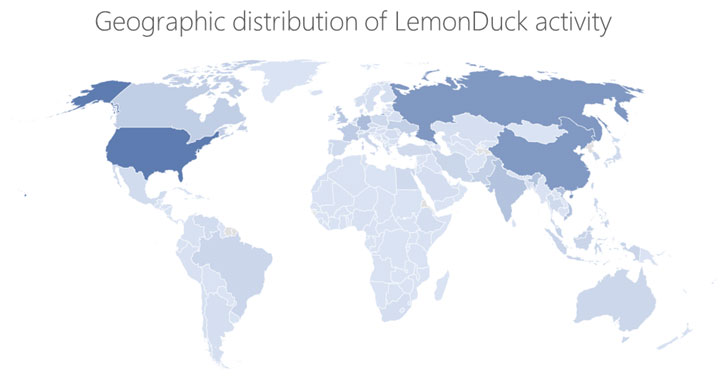
Attacks incorporating LemonDuck malware have been primarily centered on the producing and IoT sectors, with the U.S, Russia, China, Germany, the U.K., India, Korea, Canada, France, and Vietnam witnessing the most encounters.
Moreover, Microsoft outed the functions of a second entity that relies on LemonDuck for accomplishing “independent ambitions”, which the business codenamed “LemonCat.” The attack infrastructure linked with the “Cat” variant is reported to have emerged in January 2021, ultimately leading to its use in attacks exploiting vulnerabilities concentrating on Microsoft Exchange Server. Subsequent intrusions getting advantage of the Cat domains resulted in backdoor installation, credential, and details theft, and malware shipping, normally a Windows trojan known as Ramnit.
“The reality that the Cat infrastructure is used for far more hazardous strategies does not deprioritize malware infections from the Duck infrastructure,” Microsoft reported. “In its place, this intelligence provides important context for being familiar with this risk: the very same established of equipment, accessibility, and approaches can be re-made use of at dynamic intervals, to greater affect.”
Observed this report appealing? Abide by THN on Facebook, Twitter and LinkedIn to read through extra exclusive content we publish.
Some sections of this posting are sourced from:
thehackernews.com

 Nine traits you need to succeed as a cyber security leader
Nine traits you need to succeed as a cyber security leader