Microsoft on Thursday shared clean guidance on nonetheless one more vulnerability influencing the Windows Print Spooler assistance, stating that it’s doing the job to address it in an upcoming security update.
Tracked as CVE-2021-34481 (CVSS rating: 7.8), the issue fears a local privilege escalation flaw that could be abused to conduct unauthorized actions on the method. The organization credited security researcher Jacob Baines for exploring and reporting the bug.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“An elevation of privilege vulnerability exists when the Windows Print Spooler provider improperly performs privileged file operations. An attacker who successfully exploited this vulnerability could run arbitrary code with Program privileges,” the Windows maker claimed in its advisory. “An attacker could then set up systems check out, improve, or delete knowledge or develop new accounts with comprehensive user legal rights.”
Nevertheless, it truly is really worth pointing out that profitable exploitation of the vulnerability involves the attacker to have the capacity to execute code on a target system. In other text, this vulnerability can only be exploited regionally to attain elevated privileges on a device.
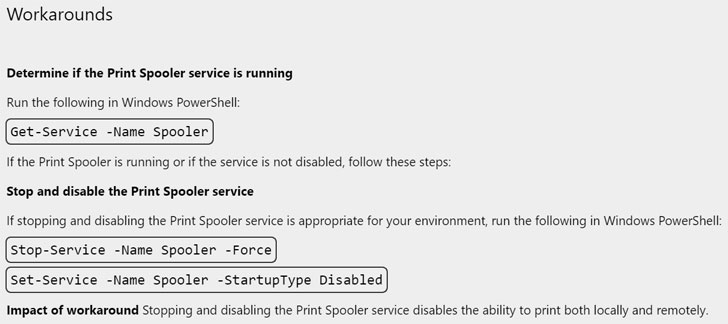
As workarounds, Microsoft is recommending people to end and disable the Print Spooler provider to prevent malicious actors from exploiting the vulnerability.
The advancement arrives times just after the Redmond-based organization rolled out patches to deal with a critical shortcoming in the exact component that it disclosed as being actively exploited to stage in-the-wild attacks.

Dubbed PrintNightmare (CVE-2021-34527), the vulnerability stems from a lacking permission check out in the Print Spooler that permits the set up of malicious print drivers to achieve distant code execution or nearby privilege escalation on susceptible systems.
Nevertheless, it later emerged that the out-of-band security update could be solely bypassed underneath specific ailments to get both of those nearby privilege escalation and distant code execution. Microsoft has given that said the fixes have been “functioning as created and is successful from the recognized printer spooling exploits and other general public reviews collectively currently being referred to as PrintNightmare.”
Located this posting exciting? Stick to THN on Fb, Twitter and LinkedIn to study additional exceptional material we submit.
Some parts of this article are sourced from:
thehackernews.com

 Zero-Day Attacks on Critical WooCommerce Bug Threaten Databases
Zero-Day Attacks on Critical WooCommerce Bug Threaten Databases