Microsoft’s risk intelligence division on Wednesday assessed that a subgroup of the Iranian threat actor tracked as Phosphorus is conducting ransomware attacks as a “form of moonlighting” for private gain.
The tech large, which is checking the activity cluster under the moniker DEV-0270 (aka Nemesis Kitten), mentioned it really is operated by a firm that functions under the general public aliases Secnerd and Lifeweb, citing infrastructure overlaps among the group and the two corporations.
“DEV-0270 leverages exploits for high-severity vulnerabilities to get obtain to devices and is recognised for the early adoption of freshly disclosed vulnerabilities,” Microsoft explained.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“DEV-0270 also thoroughly works by using living-off-the-land binaries (LOLBINs) during the attack chain for discovery and credential entry. This extends to its abuse of the created-in BitLocker resource to encrypt information on compromised units.”
The use of BitLocker and DiskCryptor by Iranian actors for opportunistic ransomware attacks arrived to light-weight before this Could, when Secureworks disclosed a set of intrusions mounted by a risk group it tracks under the title Cobalt Mirage with ties to Phosphorus (aka Cobalt Illusion) and TunnelVision.
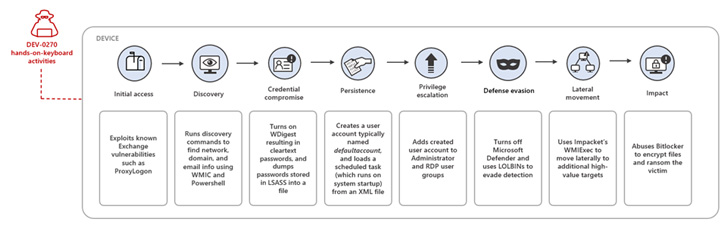
DEV-0270 is known to scan the internet to locate servers and devices inclined to flaws in Microsoft Exchange Server, Fortinet FortiGate SSL-VPN, and Apache Log4j for acquiring original access, adopted by network reconnaissance and credential theft pursuits.
Accessibility to the compromised network is reached by creating persistence by means of a scheduled job. DEV-0270 then escalates privileges to the procedure degree, permitting it to carry out article-exploitation actions these kinds of as disabling Microsoft Defender Antivirus to evade detection, lateral movement, and file encryption.

“The danger group normally works by using native WMI, net, CMD, and PowerShell commands and registry configurations to maintain stealth and operational security,” Microsoft reported. “They also put in and masquerade their customized binaries as respectable procedures to cover their presence.”
Buyers are advisable to prioritize patching of internet-dealing with Exchange servers to mitigate risk, limit network appliances like Fortinet SSL-VPN equipment from producing arbitrary connections to the internet, enforce powerful passwords, and sustain typical knowledge backups.
Identified this write-up intriguing? Stick to THN on Facebook, Twitter and LinkedIn to read extra special material we publish.
Some sections of this write-up are sourced from:
thehackernews.com


 Cisco Releases Security Patches for New Vulnerabilities Impacting Multiple Products
Cisco Releases Security Patches for New Vulnerabilities Impacting Multiple Products