Even as Microsoft expanded patches for the so-called PrintNightmare vulnerability for Windows 10 edition 1607, Windows Server 2012, and Windows Server 2016, it has arrive to light that the patch for the distant code execution exploit in the Windows Print Spooler service can be bypassed in particular scenarios, correctly defeating the security protections and allowing attackers to run arbitrary code on infected techniques.
On Tuesday, the Windows maker issued an crisis out-of-band update to tackle CVE-2021-34527 (CVSS rating: 8.8) after the flaw was unintentionally disclosed by scientists from Hong Kong-based cybersecurity firm Sangfor late previous thirty day period, at which level it emerged that the issue was distinctive from one more bug — tracked as CVE-2021-1675 — that was patched by Microsoft on June 8.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Various days in the past, two security vulnerabilities were located in Microsoft Windows’ existing printing system,” Yaniv Balmas, head of cyber study at Check out Issue, advised The Hacker Information. “These vulnerabilities enable a malicious attacker to gain full command on all windows environments that help printing.”
“These are mainly performing stations but, at moments, this relates to overall servers that are an integral component of incredibly well-liked organizational networks. Microsoft categorised these vulnerabilities as critical, but when they were revealed they were being capable to fix only one of them, leaving the door open up for explorations of the 2nd vulnerability,” Balmas added.
PrintNightmare stems from bugs in the Windows Print Spooler service, which manages the printing procedure inside regional networks. The primary worry with the menace is that non-administrator customers experienced the capacity to load their possess printer motorists. This has now been rectified.
“Immediately after putting in this [update] and afterwards Windows updates, consumers who are not directors can only set up signed print motorists to a print server,” Microsoft said, detailing the improvements made to mitigate the hazards related with the flaw. “Administrator qualifications will be expected to install unsigned printer motorists on a printer server going ahead.”
Write-up the update’s release, CERT/CC vulnerability analyst Will Dormann cautioned that the patch “only seems to deal with the Distant Code Execution (RCE by means of SMB and RPC) variants of the PrintNightmare, and not the Neighborhood Privilege Escalation (LPE) variant,” thereby allowing for attackers to abuse the latter to get Technique privileges on vulnerable units.

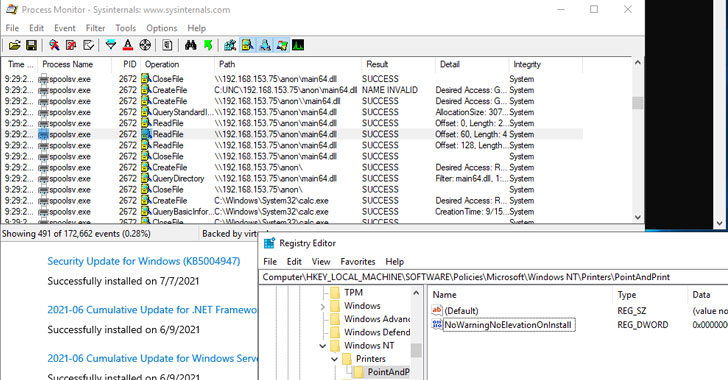
Now, more tests of the update has revealed that exploits focusing on the flaw could bypass the remediations completely to acquire both of those nearby privilege escalation and distant code execution. To obtain this, having said that, a Windows plan named ‘Point and Print Restrictions’ must be enabled (Pc ConfigurationPoliciesAdministrative TemplatesPrinters: Level and Print Limits), which can be potentially utilised to set up malicious printer motorists.
“Observe that the Microsoft update for CVE-2021-34527 does not successfully avert exploitation of programs exactly where the Place and Print NoWarningNoElevationOnInstall is set to 1,” Dormann claimed Wednesday. Microsoft, for its portion, clarifies in its advisory that “Position and Print is not straight similar to this vulnerability, but the technology weakens the nearby security posture in this kind of a way that exploitation will be probable.”
When Microsoft has advisable the nuclear choice of halting and disabling the Print Spooler assistance, an option workaround is to permit security prompts for Position and Print, and limit printer driver installation privileges to directors on your own by configuring the “RestrictDriverInstallationToAdministrators” registry benefit to avoid common consumers from setting up printer drivers on a print server.
Located this post attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to study extra special content we submit.
Some sections of this write-up are sourced from:
thehackernews.com

 Kaseya offers pre-patch instructions for on-prem VSA customers
Kaseya offers pre-patch instructions for on-prem VSA customers