If corporations want to get critical about software program security, they require to empower their engineers to perform a defensive function from cyberattacks as they craft their code.
The issue is, builders have not experienced the most inspiring introduction to security schooling more than the decades, and anything at all that can be finished to make their experience additional engaging, productive, and enjoyment is heading to be a powerful motivator in helping them gain precious secure coding capabilities.
And following dedicating cherished time to mastering new skills that can assistance beat attackers at their personal activity, the possibility to check these new powers is not very easily identified in a secure ecosystem.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
So, what is a battle-hardened, security-conscious engineer to do?
A new attribute unveiled on the Secure Code Warrior system, named ‘Missions,’ is a obstacle class that elevates consumers from the recall of realized security knowledge to the application of it in a actual-entire world simulation natural environment.
This scaffolded, microlearning strategy builds potent, safe coding competencies that are position-related and much extra entertaining than (vertically) watching endless training movies in the track record of a workday.
The initially readily available ‘Mission’ is a simulation of the GitHub Unicode breach. It is really not as simple as it may well seem on the surface area, and it’s a seriously intelligent vulnerability that is enjoyable to dissect. Security researcher 0xsha did a comprehensive circumstance study on how this very same bug can be applied to exploit Django by way of circumstance transformations even though also displaying how vulnerability habits can transform amongst programming languages.
There is a great deal extra to discover about this security issue, and in this article is a good place to get started.
GitHub’s Head-On (Circumstance Mapping) Collision
In a website publish from November 28, 2019, security investigation team Knowledge reported on a security bug they uncovered on GitHub. They outlined how they were equipped to employ a Scenario Mapping Collision in Unicode to bring about a password reset email supply to the wrong email address (or if you have been considering like an attacker, an email deal with of the threat actor’s picking).
Even though a security vulnerability is hardly ever fantastic information, security scientists who rock a whitehat do offer some mercy — not to point out the chance to avert disaster — if they find out probably exploitable problems in a codebase. Their weblogs and stories usually make for excellent examining, and it is really sort of interesting to find out about a new vulnerability and how it works.
In get to shift to the up coming degree of secure coding prowess, it is super highly effective not just to find common vulnerabilities, but also have a protected, fingers-on surroundings to recognize how to exploit them as very well.
Hold studying to find how a Circumstance Mapping Collision in Unicode can be exploited, how it appears to be like in true-time, and how you can take on the attitude of a security researcher and try out it out for oneself.

Unicode: Additional Than Just Emojis
“Unicode” may well not be on the radar of the ordinary human being, but the prospects are fantastic that most folks use it in some sort each working day. If you have made use of a web browser, any Microsoft program, or sent an emoji, then you have been up shut and personal with Unicode.
It is really a standard for dependable encoding and handling of textual content from most of the world’s creating devices, making certain that all people can (digitally) convey by themselves utilizing a one character established.
As it stands, there are in excess of 143,000 characters, so you happen to be included whether or not you are utilizing the Icelandic þ, or the Turkish dotless ı, or anything at all in in between.
Thanks to the sheer volume of characters Unicode has in its established, a way of converting characters to a different “equal” character is desired in numerous conditions. For instance, it seems practical that if you convert a Unicode string with a dotless “ı” to ASCII, that it ought to merely transform into an “i,” ideal?
With a wonderful volume of character, encoding arrives good accountability opportunity for catastrophe.
A scenario mapping collision in Unicode is a business enterprise logic flaw and can guide to an account takeover of accounts not shielded by 2FA. Verify out an case in point of this bug in a actual code snippet:
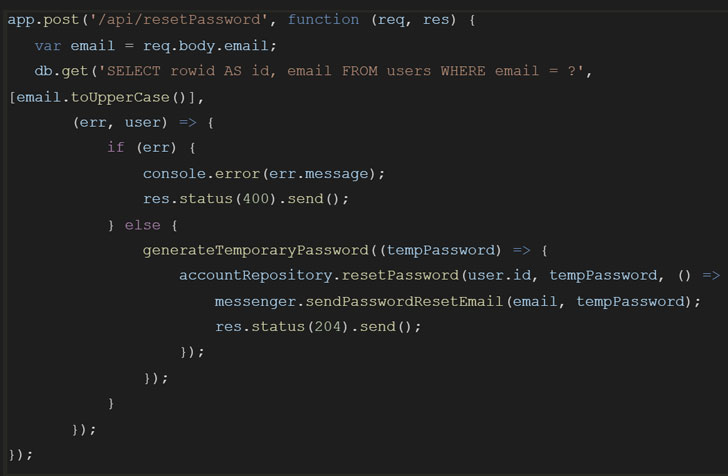
The logic goes anything like this:
Let us see what occurs with the illustration provided in the primary web site write-up, where by a user requests a password reset for the email John@GıtHub.com (be aware the Turkish dotless i):
Be aware that this process finishes up sending the really delicate email to the incorrect email tackle. Oops!
How to solid out this Unicode demon
The intriguing factor of this certain vulnerability is that there are many elements that make it susceptible:
In idea, you can take care of this unique issue in two strategies, as discovered in the weblog post from Wisdom:
When it arrives to hardening program, it is a excellent idea to depart very little to likelihood, employing as several layers of defense in area as feasible. For all you know, there may well be other ways to exploit this encoding – you might be just not mindful of them nevertheless. Anything you can do to reduce risk and shut windows that may perhaps be remaining open for an attacker is worthwhile.
Completely ready To Pilot Your Personal Mission?
It is really time to choose your protected coding and recognition competencies to the subsequent amount. Working experience this GitHub vulnerability in an immersive, secure simulation, wherever you can see the effects of lousy code in the two frontend and backend contexts. Attackers have an edge, so let us even the participating in subject and implement authentic abilities with a whitehat counter-punch.

Found this posting exciting? Stick to THN on Facebook, Twitter and LinkedIn to study a lot more exceptional content we put up.
Some pieces of this short article are sourced from:
thehackernews.com


 #EdgeLive: Defending Against the Growing Threat of DDoS Attacks
#EdgeLive: Defending Against the Growing Threat of DDoS Attacks