Well-liked Indian cellular payments company MobiKwik on Monday came below hearth right after 8.2 terabytes (TB) of details belonging to thousands and thousands of its customers commenced circulating on the dark web in the aftermath of a big data breach that arrived to light-weight previously this month.
The leaked information includes delicate private details this kind of as:
- customer names,
- hashed passwords,
- email addresses,
- household addresses,
- GPS spots,
- list of set up apps,
- partially-masked credit history card figures,
- connected financial institution accounts and affiliated account quantities,
- and even know your client (KYC) documents of 3.5 million customers.
Even worse, the leak also displays that MobiKwik does not delete the card info from its servers even just after a person has eliminated them, in what’s likely a breach of governing administration rules.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
New rules issued by India’s apex banking establishment, the Reserve Bank of India, prohibit on the internet merchants, e-commerce sites, and payment aggregators from storing card specifics of a shopper on-line. The guidelines are set to appear into result starting off July 2021.
As of July 2020, MobiKwik serves 120 million people and 3 million merchants across the nation.
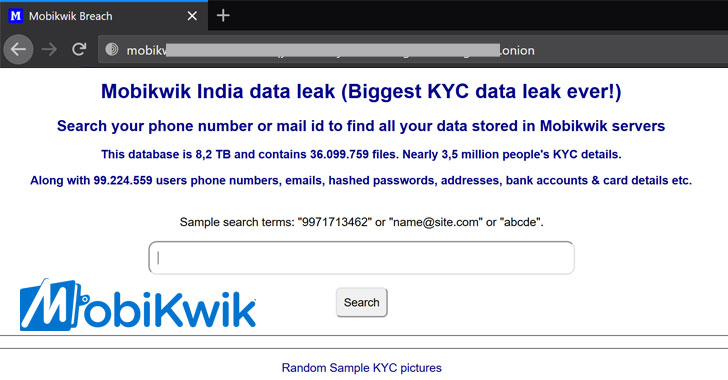
The info leak site, which is accessible via Tor browser and features of 36,099,759 information, came on line immediately after the digital wallet business vehemently denied the incident on March 4 subsequent a report by an unbiased security researcher Rajshekhar Rajaharia.
“A media-crazed so-named security researcher has frequently more than the previous week presented concocted information losing valuable time of our business even though desperately striving to grab media awareness,” MobiKwik tweeted. “We extensively investigated his allegations and did not come across any security lapses. The various sample textual content data files that he has been showcasing demonstrate absolutely nothing. Anyone can create these textual content files to falsely harass any organization.”
Nonetheless, numerous end users have confirmed to the contrary, locating their personalized facts in the “MobiKwik India information leak” web page, lending credence to the breach.
“Never ever *at any time* behave like @MobiKwik has in this thread from 25 days in the past,” Troy Hunt, security researcher and creator of breach notification resource Have I Been Pwned, explained in a tweet, contacting out the company MobiKwik’s handling of the condition.
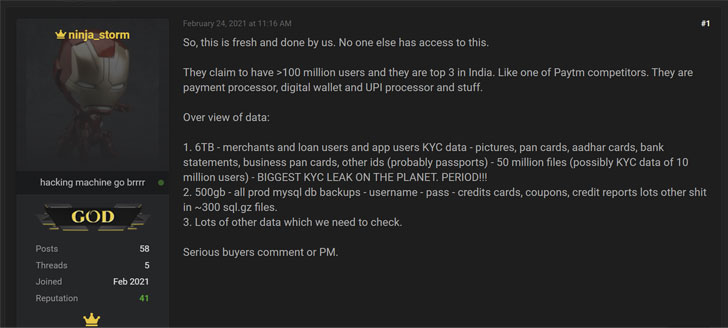
According to resources near to the incident, the compromise was at first marketed in a database leaking discussion board on February 24, with a hacker saying accessibility to 6TB info from an unnamed Paytm competitor.
Apparently, it appears that after Rajaharia disclosed the leak, outed the firm’s identification, and warned MobiKwik more than email, the business concurrently took steps to stop the hacker from downloading the details.
“We […] misplaced obtain to primary business servers, not shocking while… Cant obtain everything new,” the hacker claimed in a discussion board put up a working day afterwards, including that partial down load might have been corrupted.
“We hardly ever required any dollars in any case, so not unhappy. But one particular of the most significant hacks of KYC at any time shit!!! OR SO WE Believed. 🙁 So, I guess I mature old indicating I utilized to hack and shit. Fairly than essentially hacking and shit. Remarkable 1 thirty day period though!!!,” the hacker claimed, implying that the hack dated again to January, echoing Rajaharia’s tweets from March 4.
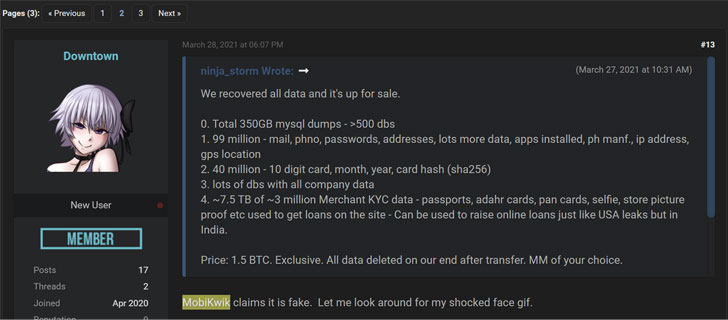
But a month afterwards, in a different listing on March 27, the hacker claimed, “we recovered all info and it can be up for sale,” supplying up what is alleged to be 8TB of their knowledge for 1.5 bitcoin ($85,684.65).
However, in an intriguing convert of functions, plans to put the details on sale surface to have been suspended till further notice. “Only sell this to enterprise immediately after owing verification that we are dealing with firm,” the hacker reported in an update, implying an extortion scheme.
It truly is not quickly clear how the threat actor managed to get unauthorized entry to MobiKwik’s servers, but the hacker reported, “it will be embarrassing for the corporation. tale for someother time..” (sic)
The Hacker Information has reached out to MobiKwik, and we will update the story if we get a response.
Located this write-up exciting? Abide by THN on Facebook, Twitter and LinkedIn to examine more distinctive articles we post.
Some elements of this short article are sourced from:
thehackernews.com

 Apple patches zero-day targeted for iPhones, iPads and its popular watches
Apple patches zero-day targeted for iPhones, iPads and its popular watches