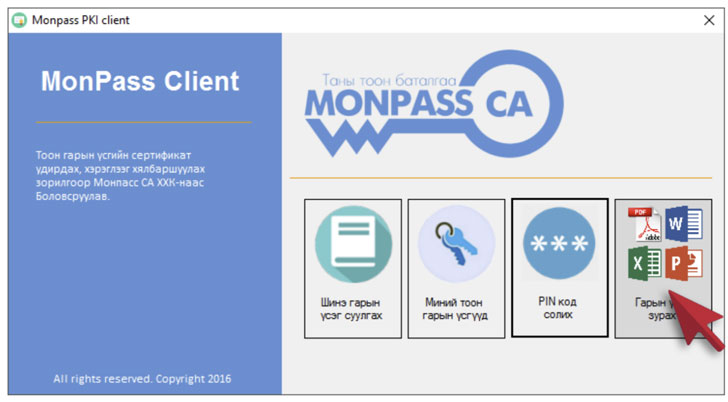
In still yet another occasion of application source chain attack, unidentified hackers breached the website of MonPass, one of Mongolia’s major certificate authorities, to backdoor its installer computer software with Cobalt Strike binaries.
The trojanized client was offered for down load in between February 8, 2021, and March 3, 2021, reported Czech cybersecurity application business Avast in a report posted Thursday.
In addition, a community webserver hosted by MonPass was infiltrated likely as quite a few as eight individual situations, with the researchers uncovering eight distinct web shells and backdoors on the compromised server.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Avast’s investigation into the incident commenced after it found the backdoored installer and the implant on 1 of its customers’ programs.
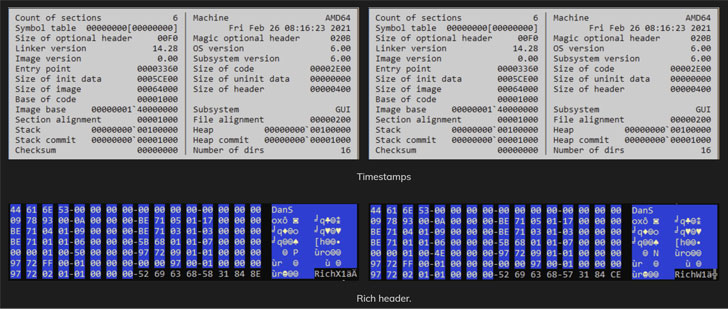
“The malicious installer is an unsigned [Portable Executable] file,” the scientists mentioned. “It starts off by downloading the reputable variation of the installer from the MonPass formal website. This legit edition is dropped to the ‘C:UsersPublic’ folder and executed underneath a new process. This ensures that the installer behaves as predicted, this means that a typical user is unlikely to observe anything at all suspicious.”
The modus operandi is also noteworthy for the use of steganography to transfer shellcode to the target machine, with the installer downloading a bitmap picture (.BMP) file from a distant server to extract and deploy an encrypted Cobalt Strike beacon payload.
MonPass was notified of the incident on April 22, just after which the certification authority took ways to tackle their compromised server and notify these who downloaded the backdoored consumer.

The incident marks the next time software program provided by a certification authority has been compromised to infect targets with destructive backdoors. In December 2020, ESET disclosed a campaign referred to as “Procedure SignSight,” whereby a electronic signature toolkit from the Vietnam Govt Certification Authority (VGCA) was tampered to include things like spy ware able of amassing technique information and facts and installing further malware.
The development also will come as Proofpoint, before this 7 days, disclosed the abuse of Cobalt Strike penetration screening software in threat actor campaigns has shot as a result of the roof, jumping 161% 12 months-about-calendar year from 2019 to 2020.
“Cobalt Strike is getting more and more popular among menace actors as an first accessibility payload, not just a 2nd-stage tool menace actors use the moment accessibility is realized, with legal risk actors making up the bulk of attributed Cobalt Strike strategies in 2020,” Proofpoint researchers mentioned.
Discovered this short article exciting? Observe THN on Fb, Twitter and LinkedIn to go through much more special articles we publish.
Some pieces of this posting are sourced from:
thehackernews.com


 CISA Offers New Mitigation for PrintNightmare Bug
CISA Offers New Mitigation for PrintNightmare Bug