Banking apps from Brazil are becoming specific by a a lot more elusive and stealthier variation of an Android remote obtain trojan (RAT) that is able of carrying out monetary fraud attacks by stealing two-factor authentication (2FA) codes and initiating rogue transactions from contaminated devices to transfer dollars from victims’ accounts to an account operated by the menace actor.
IBM X-Power dubbed the banking malware BrazKing, formerly referred to as PixStealer by Look at Point Research. The cellular RAT was very first observed around November 2018, in accordance to ThreatFabric.
“It turns out that its builders have been operating on making the malware much more agile than prior to, moving its core overlay system to pull bogus overlay screens from the command-and-handle (C2) server in genuine-time,” IBM X-Power researcher Shahar Tavor noted in a technological deep dive printed last 7 days. “The malware […] permits the attacker to log keystrokes, extract the password, take over, initiate a transaction, and seize other transaction authorization details to entire it.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

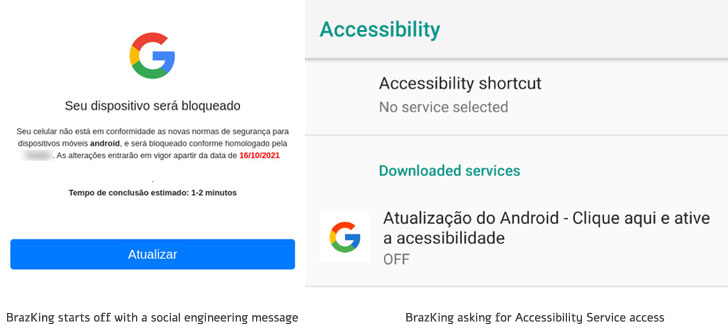
The an infection plan kicks off with a social engineering message that contains a link to an HTTPS site that warns possible victims about security issues in their gadgets, even though prompting an selection to update the operating procedure to the most up-to-date model. Even so, for the attacks to succeed, customers will have to explicitly empower a placing to install applications from unknown sources.
BrazKing, like its predecessor, abuses accessibility permissions to accomplish overlay attacks on banking applications, but alternatively of retrieving a fake display from a hardcoded URL and existing it on prime of the reputable app, the procedure is now executed on the server-aspect so that the list of specific applications can be modified without producing variations to the malware by itself.
“The detection of which app is remaining opened is now performed server aspect, and the malware frequently sends on-display screen content material to the C2. Credential grabbing is then activated from the C2 server, and not by an automated command from the malware,” Tavor said.
Banking trojans like BrazKing are specially insidious in that following set up they require only a solitary motion from the target, i.e., enabling Android’s Accessibility Provider, to fully unleash their destructive functionalities. Armed with the required permissions, the malware gathers intel from the contaminated machine, including reading through SMS messages, capturing keystrokes, and accessing contact lists.
“Accessibility Provider is long acknowledged to be the Achilles’ heel of the Android functioning technique,” ESET researcher Lukas Stefanko explained last 12 months.

On top rated of that, the malware also takes various actions to attempt to safeguard by itself once it has been set up to steer clear of detection and removal. BrazKing is built to keep an eye on people when they are launching an antivirus alternative or opening the app’s uninstall monitor, and if so, swiftly return them to the property screen right before any motion can be taken.
“Need to the consumer attempt to restore the machine to manufactory settings, BrazKing would rapidly tap the ‘Back’ and ‘Home’ buttons faster than a human could, avoiding them from getting rid of the malware in that way,” Tavor discussed.
The supreme objective of the malware is to allow for the adversary to interact with functioning applications on the device, preserve tabs on the apps the end users are viewing at any offered point of time, document keystrokes entered in banking apps, and screen fraudulent overlay screens to siphon the payment card’s PIN quantities and 2FA codes, and at some point accomplish unauthorized transactions.
“Major desktop banking trojans have lengthy deserted the client banking realms for larger bounties in BEC fraud, ransomware attacks and high-benefit individual heists,” Tavor reported. “This, collectively with the ongoing pattern of on the web banking transitioning to mobile, triggered a void in the underground cybercrime arena to be stuffed by cellular banking malware.”
Discovered this report exciting? Adhere to THN on Facebook, Twitter and LinkedIn to read a lot more distinctive material we submit.
Some sections of this write-up are sourced from:
thehackernews.com


 Fifth of UK security pros discriminated against in 2021
Fifth of UK security pros discriminated against in 2021