The politically motivated Moses Team hacker team has been noticed utilizing a tailor made multi-component toolset with the aim of carrying out espionage versus its targets as section of a new campaign that solely singles out Israeli businesses.
Initial publicly documented in late 2021, Moses Workers is thought to be sponsored by the Iranian governing administration, with attacks documented in opposition to entities in Israel, Italy, India, Germany, Chile, Turkey, the U.A.E., and the U.S.
Earlier this thirty day period, the hacker collective was noticed incorporating a beforehand undocumented remote accessibility trojan (RAT) referred to as “StrifeWater” that masquerades as the Windows Calculator application to evade detection.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Near evaluation reveals that the team has been energetic for more than a calendar year, a lot before than the group’s to start with official general public exposure, taking care of to remain underneath the radar with an very reduced detection rate,” conclusions from FortiGuard Labs expose.
The most current danger action includes an attack route that leverages the ProxyShell vulnerability in Microsoft Trade servers as an first infection vector to deploy two web shells, adopted by exfiltrating Outlook Facts Documents (.PST) from the compromised server.
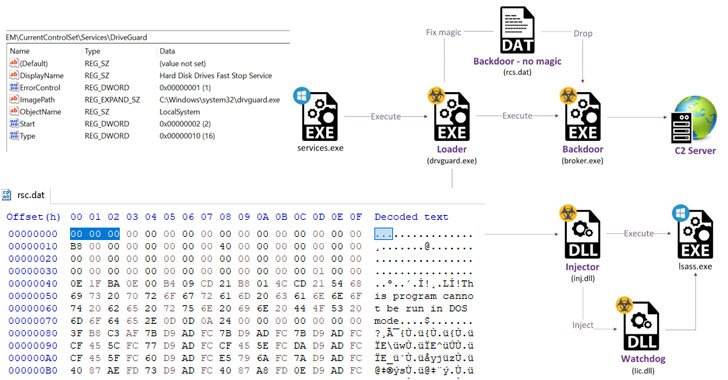
Subsequent phases of the an infection chain entail an endeavor to steal credentials by dumping the memory contents of a critical Windows system termed Area Security Authority Subsystem Assistance (Lsass.exe), right before dropping and loading the “StrifeWater” backdoor (broker.exe).
The installation of the “Broker” implant, which is made use of to execute commands fetched from a remote server, down load data files, and exfiltrate details from focus on networks, is facilitated by a loader that masquerades as a “Hard Disk Drives Quickly Halt Support” dubbed “DriveGuard” (drvguard.exe).
On leading of that, the loader is also accountable for launching a watchdog system (“lic.dll”) that makes sure its personal support is under no circumstances interrupted by restarting the DriveGuard each individual time it can be stopped as very well as ensuring that the loader is configured to run mechanically on procedure startup.
The broker backdoor, for its part, is also equipped to delete itself from the disk making use of a CMD command, seize screenshots, and update the malware to substitute the recent module on the system with a file gained from the server.
StrifeWater is also noteworthy for its tries to continue to be beneath the radar by posing as the Windows Calculator app (calc.exe), with FortiGuard Labs researchers identifying two older samples courting again to the conclusion of December 2020, suggesting that the marketing campaign has been operational for around a year.
The attribution to Moses Personnel is based on similarities in the web shells utilised in beforehand disclosed attacks and its sample of victimology.
“The group is really determined, capable, and set on harmful Israeli entities,” the researchers explained. “At this level, they continue on to count on 1-working day exploits for their preliminary intrusion section. Despite the fact that the attacks we discovered had been carried out for espionage applications, this does not negate the chance that the operators will later turn to harmful measures.”
Uncovered this posting exciting? Follow THN on Fb, Twitter and LinkedIn to browse far more distinctive material we publish.
Some elements of this posting are sourced from:
thehackernews.com


 U.S. Says Russian Hackers Stealing Sensitive Data from Defense Contractors
U.S. Says Russian Hackers Stealing Sensitive Data from Defense Contractors