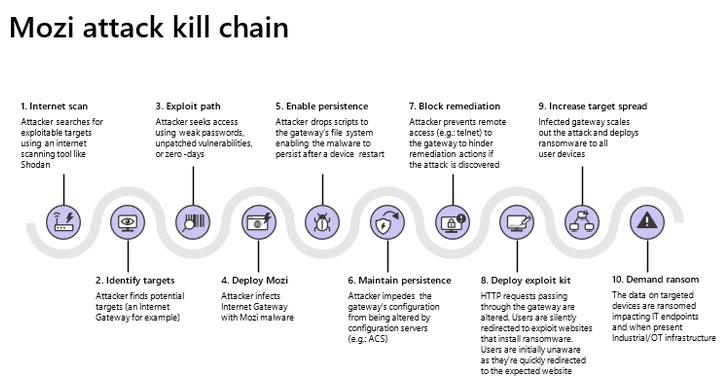
Mozi, a peer-to-peer (P2P) botnet recognised to goal IoT products, has obtained new abilities that let it to achieve persistence on network gateways produced by Netgear, Huawei, and ZTE, in accordance to new conclusions.
“Network gateways are a specially juicy goal for adversaries simply because they are excellent as initial entry factors to company networks,” researchers at Microsoft Security Risk Intelligence Heart and Section 52 at Azure Defender for IoT said in a technical publish-up. “By infecting routers, they can perform guy-in-the-middle (MITM) attacks—via HTTP hijacking and DNS spoofing—to compromise endpoints and deploy ransomware or cause security incidents in OT services.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Very first documented by Netlab 360 in December 2019, Mozi has a background of infecting routers and electronic online video recorders in purchase to assemble them into an IoT botnet, which could be abused for launching distributed denial-of-assistance (DDoS) attacks, knowledge exfiltration, and payload execution. The botnet is developed from the source code of many recognized malware families this sort of as Gafgyt, Mirai, and IoT Reaper.
Mozi spreads by means of the use of weak and default telnet passwords as properly as by unpatched IoT vulnerabilities, with the IoT malware speaking applying a BitTorrent-like Distributed Hash Desk (DHT) to record the contact information for other nodes in the botnet, the same mechanism utilized by file-sharing P2P purchasers. The compromised products listen for commands from controller nodes and also try to infect other vulnerable targets.
An IBM X-Power analysis published in September 2020 famous that Mozi accounted for virtually 90% of the observed IoT network site visitors from October 2019 via June 2020, indicating that risk actors are increasingly using edge of the increasing attack area provided by the IoT devices. In a separate investigation produced previous month, Elastic Security Intelligence and Analytics Team discovered that at minimum 24 countries have been focused to day, with Bulgaria and India foremost the pack.

Now fresh investigation from Microsoft’s IoT security staff has discovered that the malware “usually takes particular actions to increase its likelihood of survival upon reboot or any other attempt by other malware or responders to interfere with its procedure,” which includes acquiring persistence on targeted units and blocking TCP ports (23, 2323, 7547, 35000, 50023, and 58000) that are made use of to attain distant access to the gateway.
What’s additional, Mozi has been upgraded to help new instructions that permit the malware to hijack HTTP periods and have out DNS spoofing so as to redirect targeted visitors to an attacker-managed domain.
Businesses and customers employing Netgear, Huawei, and ZTE routers are encouraged to safe the equipment making use of potent passwords and update the units to the most up-to-date firmware. “Carrying out so will cut down the attack surfaces leveraged by the botnet and stop attackers from finding into a position where they can use the freshly learned persistence and other exploit methods,” Microsoft claimed.
Discovered this posting intriguing? Abide by THN on Fb, Twitter and LinkedIn to study extra exceptional material we article.
Some parts of this post are sourced from:
thehackernews.com

 Critical Flaw Found in Older Cisco Small Business Routers Won’t Be Fixed
Critical Flaw Found in Older Cisco Small Business Routers Won’t Be Fixed