Multiple botnets are targeting countless numbers of publicly uncovered and still unpatched Oracle WebLogic servers to deploy crypto miners and steal delicate data from infected techniques.
The attacks are taking aim at a lately patched WebLogic Server vulnerability, which was released by Oracle as section of its Oct 2020 Critical Patch Update and subsequently yet again in November (CVE-2020-14750) in the type of an out-of-band security patch.
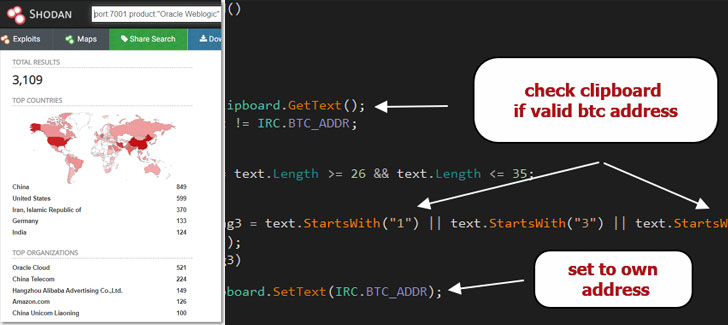
As of creating, about 3,000 Oracle WebLogic servers are obtainable on the Internet-based mostly on stats from the Shodan research engine.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Oracle WebLogic is a system for building, deploying, and functioning company Java applications in any cloud ecosystem as effectively as on-premises.
The flaw, which is tracked as CVE-2020-14882, has a CVSS score of 9.8 out of a highest ranking of 10 and has an effect on WebLogic Server versions 10.3.6.., 12.1.3.., 12.2.1.3., 12.2.1.4., and 14.1.1…
Though the issue has been tackled, the release of proof-of-strategy exploit code has built susceptible Oracle WebLogic cases a worthwhile target for threat actors to recruit these servers into a botnet that pilfers critical knowledge and deploy next stage malware payloads.
In accordance to Juniper Menace Labs, operators of the DarkIRC botnet are exploiting this RCE vulnerability to distribute laterally across the network, download documents, document keystrokes, steal qualifications, and execute arbitrary commands on compromised machines.
The malware also acts as a Bitcoin clipper that enables them to transform bitcoin wallet addresses copied to the clipboard to the operator’s bitcoin wallet tackle, making it possible for the attackers to reroute Bitcoin transactions.
What’s far more, a danger actor by the title of “Freak_OG” has been promoting the DarkIRC malware now on hacking discussion boards for $75 since August.
But it is not just DarkIRC that is exploiting the WebLogic Server vulnerability. In a individual campaign—spotted by ‘0xrb’ and specific by researcher Tolijan Trajanovski—evidence has emerged of a botnet that propagates by means of the WebLogic flaw to provide Monero cryptocurrency miner and Tsunami binaries.
Moreover applying SSH for lateral movement, the botnet has been found to achieve persistence through cron employment, get rid of competing mining applications, and even uninstall Endpoint detection and reaction (EDR) equipment from Alibaba and Tencent.
It truly is proposed that end users apply the Oct 2020 Critical Patch Update and the updates related with CVE-2020-14750 as shortly as attainable to mitigate challenges stemming from this flaw.
Oracle has also offered directions to harden the servers by protecting against external accessibility to inside purposes available on the Administration port.
Found this report intriguing? Observe THN on Facebook, Twitter and LinkedIn to read far more distinctive information we post.
Some parts of this posting are sourced from:
thehackernews.com


 CISO with a small security team? Learn from your peers’ experience with this free e-book
CISO with a small security team? Learn from your peers’ experience with this free e-book