The U.S. Cybersecurity and Infrastructure Security Company (CISA) on Tuesday produced an advisory concerning many security vulnerabilities affecting all versions of Honeywell Experion Course of action Awareness System C200, C200E, C300, and ACE controllers that could be exploited to attain distant code execution and denial-of-company (DoS) ailments.
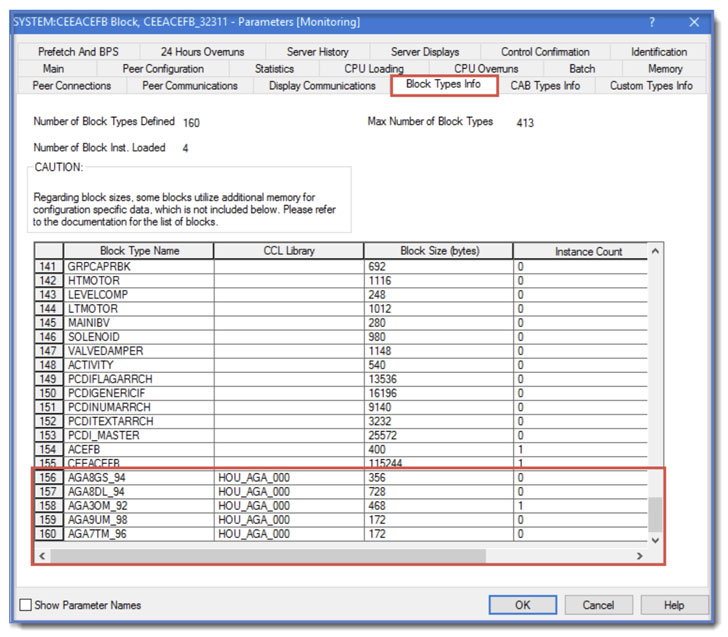
“A Management Ingredient Library (CCL) might be modified by a negative actor and loaded to a controller these that destructive code is executed by the controller,” Honeywell pointed out in an impartial security notification revealed earlier this February. Credited with discovering and reporting the flaws are Rei Henigman and Nadav Erez of industrial cybersecurity business Claroty.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Experion Procedure Know-how Method (PKS) is a distributed regulate technique (DCS) that is created to control big industrial processes spanning a range of sectors ranging from petrochemical refineries to nuclear electricity plants the place superior trustworthiness and security is important.
The list of three flaws is as follows –
- CVE-2021-38397 (CVSS rating: 10.) – Unrestricted Add of File with Harmful Style
- CVE-2021-38395 (CVSS score: 9.1) – Poor Neutralization of Distinctive Components in Output Made use of by a Downstream Ingredient
- CVE-2021-38399 (CVSS rating: 7.5) – Relative Path Traversal
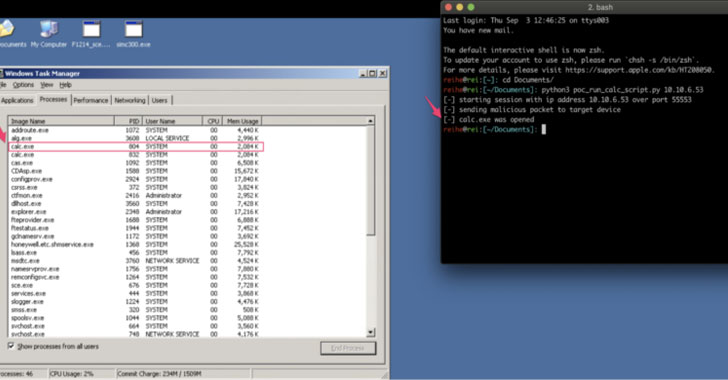
In accordance to Claroty, the issues hinge on the obtain code method which is crucial to plan the logic running in the controller, hence enabling an attacker to mimic the system and add arbitrary CLL binary files. “The unit then masses the executables without executing checks or sanitization, providing an attacker the skill to add executables and operate unauthorized indigenous code remotely with no authentication,” scientists Henigman and Erez claimed.

In a nutshell, prosperous exploitation of the shortcomings could permit a malicious party to accessibility unauthorized information and directories, and worse, remotely execute arbitrary code and result in a denial-of-services ailment. To protect against loading a modified CCL with destructive code to a controller, Honeywell has included more security enhancements by cryptographically signing every single CCL binary which is validated prior to its use.
Buyers are urged to update or patch as soon as achievable in buy to mitigate these vulnerabilities totally.
Located this write-up attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to go through far more exceptional articles we post.
Some sections of this write-up are sourced from:
thehackernews.com

 IP Surveillance Bugs in Axis Gear Allow RCE, Data Theft
IP Surveillance Bugs in Axis Gear Allow RCE, Data Theft