The U.S. Cybersecurity and Infrastructure Security Company (CISA) on Tuesday produced an advisory with regards to a number of security vulnerabilities influencing all versions of Honeywell Experion Approach Knowledge Method C200, C200E, C300, and ACE controllers that could be exploited to obtain remote code execution and denial-of-service (DoS) problems.
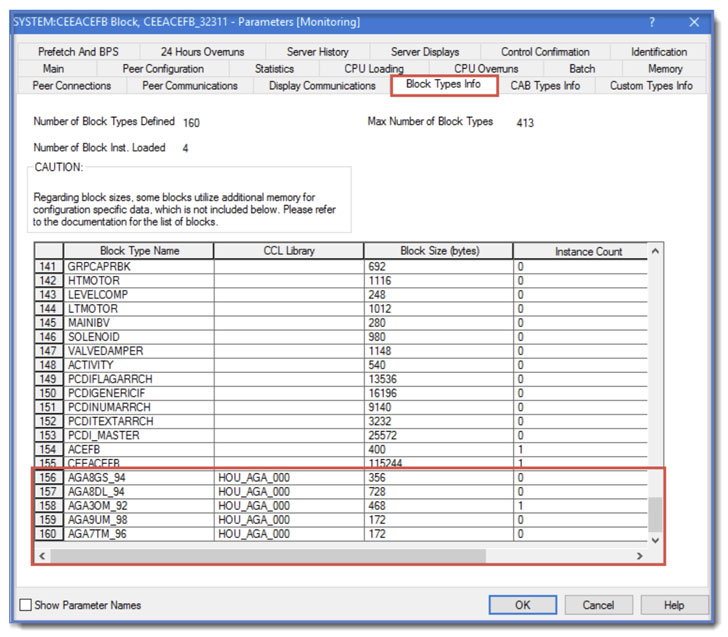
“A Manage Component Library (CCL) may well be modified by a terrible actor and loaded to a controller this kind of that malicious code is executed by the controller,” Honeywell observed in an independent security notification released previously this February. Credited with discovering and reporting the flaws are Rei Henigman and Nadav Erez of industrial cybersecurity firm Claroty.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Experion Procedure Knowledge Method (PKS) is a distributed regulate system (DCS) which is intended to management big industrial processes spanning a assortment of sectors ranging from petrochemical refineries to nuclear energy vegetation exactly where higher reliability and security is crucial.
The list of 3 flaws is as follows –
- CVE-2021-38397 (CVSS score: 10.) – Unrestricted Upload of File with Risky Form
- CVE-2021-38395 (CVSS score: 9.1) – Poor Neutralization of Unique Things in Output Used by a Downstream Ingredient
- CVE-2021-38399 (CVSS rating: 7.5) – Relative Path Traversal
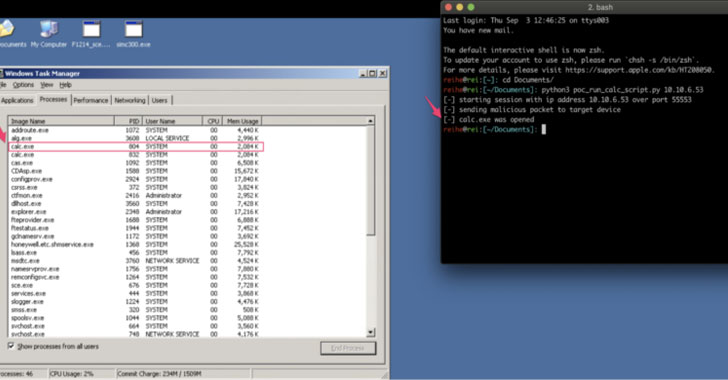
According to Claroty, the issues hinge on the down load code treatment that’s critical to software the logic managing in the controller, as a result enabling an attacker to mimic the approach and upload arbitrary CLL binary files. “The device then masses the executables with no accomplishing checks or sanitization, providing an attacker the potential to upload executables and run unauthorized native code remotely devoid of authentication,” researchers Henigman and Erez claimed.

In a nutshell, productive exploitation of the shortcomings could permit a destructive party to obtain unauthorized files and directories, and even worse, remotely execute arbitrary code and result in a denial-of-assistance affliction. To stop loading a modified CCL with destructive code to a controller, Honeywell has included additional security enhancements by cryptographically signing just about every CCL binary which is validated prior to its use.
Users are urged to update or patch as quickly as possible in purchase to mitigate these vulnerabilities fully.
Discovered this post fascinating? Follow THN on Facebook, Twitter and LinkedIn to browse far more unique material we submit.
Some pieces of this posting are sourced from:
thehackernews.com

 IP Surveillance Bugs in Axis Gear Allow RCE, Data Theft
IP Surveillance Bugs in Axis Gear Allow RCE, Data Theft