At the very least a few unique sophisticated persistent risk (APT) groups from throughout the environment have launched spear-phishing strategies in mid-March 2022 working with the ongoing Russo-Ukrainian war as a entice to distribute malware and steal sensitive info.
The strategies, undertaken by El Machete, Lyceum, and SideWinder, have specific a variety of sectors, together with energy, economical, and governmental sectors in Nicaragua, Venezuela, Israel, Saudi Arabia, and Pakistan.
“The attackers use decoys ranging from official-searching paperwork to news article content or even work postings, based on the targets and area,” Verify Position Study reported in a report. “A lot of of these entice documents employ destructive macros or template injection to attain an original foothold into the qualified companies, and then launch malware attacks.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
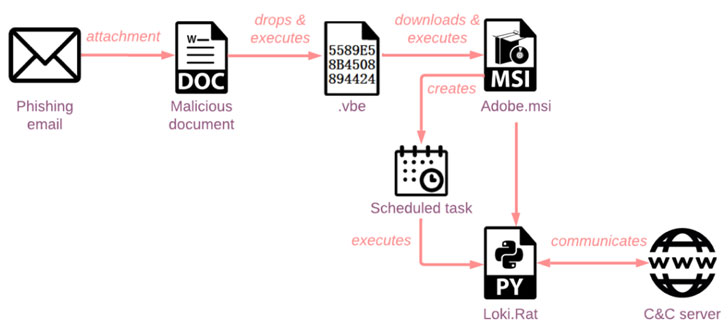
The infection chains of El Machete, a Spanish-speaking danger actor initial documented in August 2014 by Kaspersky, entail the use of macro-laced decoy documents to deploy an open-source distant access trojan called Loki.Rat which is capable of harvesting keystrokes, qualifications, and clipboard details as very well as carrying out file functions and executing arbitrary commands.
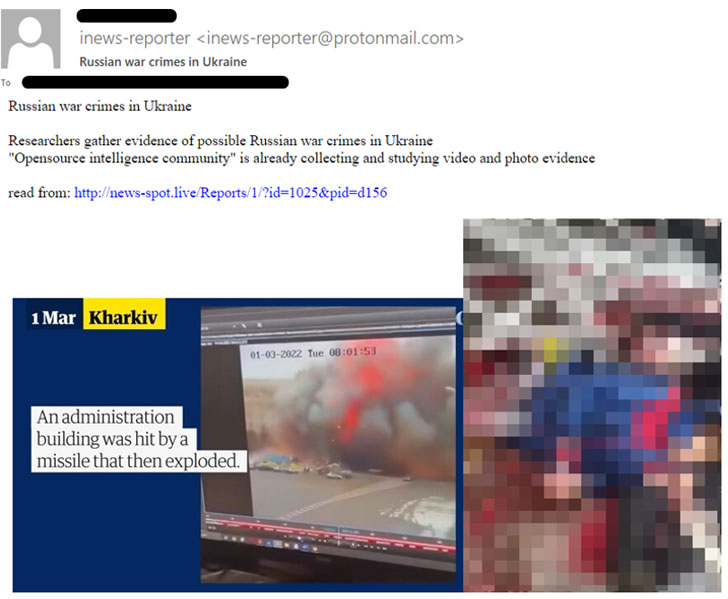
A second campaign is from the Iranian APT team recognised as Lyceum that Test Issue stated launched a phishing attack utilizing an email purportedly about “Russian war crimes in Ukraine” to supply to start with-phase .NET and Golang droppers, which are then employed to deploy a backdoor for running data files retrieved from a distant server.
A different case in point is SideWinder, a point out-sponsored crew that is explained to run in aid of Indian political passions and with a precise target on its neighbors China and Pakistan. The attack sequence, in this case, employs a weaponized document that exploits the Equation Editor flaw in Microsoft Place of work (CVE-2017-11882) to distribute information thieving malware.
The findings echo similar warnings from Google’s Risk Evaluation Group (TAG), which disclosed that nation-condition-backed risk teams from Iran, China, North Korea, and Russia and various other criminal and monetarily inspired actors are leveraging war-connected themes in phishing campaigns, on the web extortion tries, and other destructive pursuits.
“Whilst the attention of the general public does not generally linger on a one issue for an extended period of time, the Russian-Ukrainian war is an apparent exception,” the Israeli corporation explained. “This war has an effect on many regions all around the world and has likely considerably-reaching ramifications. As a result, we can expect that APT threat actors will go on to use this crisis to conduct specific phishing campaigns for espionage purposes.”
Identified this article appealing? Comply with THN on Fb, Twitter and LinkedIn to study extra unique written content we publish.
Some sections of this post are sourced from:
thehackernews.com




 Brokenwire Hack Could Let Remote Attackers Disrupt Charging for Electric Vehicles
Brokenwire Hack Could Let Remote Attackers Disrupt Charging for Electric Vehicles