A malware recognised for concentrating on macOS running system has been up to date once yet again to increase much more characteristics to its toolset that allows it to amass and exfiltrate sensitive knowledge stored in a assortment of applications, together with apps these as Google Chrome and Telegram, as section of more “refinements in its ways.”
XCSSET was uncovered in August 2020, when it was uncovered focusing on Mac developers making use of an unusual means of distribution that included injecting a destructive payload into Xcode IDE assignments which is executed at the time of setting up undertaking documents in Xcode.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The malware arrives with numerous abilities, this kind of as studying and dumping Safari cookies, injecting malicious JavaScript code into various web sites, stealing facts from apps, these kinds of as Notes, WeChat, Skype, Telegram, and encrypting consumer data files.
Previously this April, XCSSET acquired an up grade that enabled the malware authors to focus on macOS 11 Huge Sur as perfectly as Macs working on M1 chipset by circumventing new security procedures instituted by Apple in the most current functioning method.
“The malware downloads its individual open up instrument from its C2 server that will come pre-signed with an advertisement-hoc signature, whilst if it ended up on macOS versions 10.15 and reduce, it would however use the system’s designed-in open up command to run the apps,” Pattern Micro researchers earlier observed.
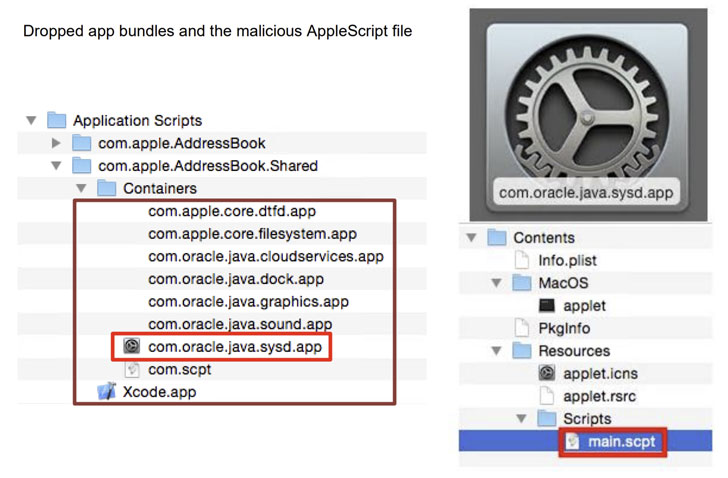
Now in accordance to a new generate-up released the cybersecurity organization on Thursday, it has been discovered that XCSSET runs a malicious AppleScript file to compress the folder containing Telegram knowledge (“~/Library/Group Containers/6N38VWS5BX.ru.keepcoder.Telegram”) into a ZIP archive file, ahead of uploading it to a remote server below their manage, as a result enabling the danger actor to log in making use of the target accounts.

With Google Chrome, the malware tries to steal passwords stored in the web browser — which are in flip encrypted using a master password termed “protected storage essential” — by tricking the person into granting root privileges through a fraudulent dialog box, abusing the elevated permissions to run an unauthorized shell command to retrieve the learn key from the iCloud Keychain, adhering to which the contents are decrypted and transmitted to the server.
Apart from Chrome and Telegram, XCSSET also has the capacity to plunder valuable facts from a selection of applications like Evernote, Opera, Skype, WeChat, and Apple’s possess Contacts and Notes apps by retrieving said data from their respective sandbox directories.
“The discovery of how it can steal info from several applications highlights the diploma to which the malware aggressively attempts to steal numerous types of details from afflicted programs,” the researchers said.
Located this post fascinating? Adhere to THN on Fb, Twitter and LinkedIn to study more exceptional material we write-up.
Some parts of this post are sourced from:
thehackernews.com

 Kaseya Obtains Universal Decryptor for REvil Ransomware
Kaseya Obtains Universal Decryptor for REvil Ransomware