
Although we are recovering from the worst pandemic, cyber threats have shown no indicator of downshifting, and cybercriminals are continue to not brief of malicious and advanced ways to obtain their plans.
The World Risk Landscape Report indicates a drastic increase in subtle cyberattacks focusing on digital infrastructures, businesses, and folks in 2021. Threats can take distinctive varieties with the intent to commit fraud and problems businesses and men and women. Ransomware, DDoS attacks, phishing, malware, and person-in-the-center attacks stand for the greatest threat to companies right now.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
When new threats emerge, attackers get edge of them – nevertheless, most enterprises are only aware of the present-day threats.
Corporations battle to deal with these threats thanks to their useful resource sophistication and their lack of understanding of evolving menace landscapes. For these good reasons, businesses want visibility on the state-of-the-art threats specially focusing on their infrastructure. This report will outline the evolution in the cyber threat landscape 2021.
Evolving Menace Landscape – Discover Out What You Really don’t Know
1 — Ransomware
Ransomware is however a common and evolving cyber security danger with many hugely publicized incidents. Ransomware incidents have an effect on organizations, firms, and folks ensuing in economic reduction, operational disruptions, and info exfiltration. Compromise as a result of internet-dealing with vulnerabilities & misconfigurations, 3rd parties & managed services providers, Distant Desktop Protocol (RDP) and phishing e-mail remain the most typical infection vectors.
The incidence of extortion schemes has enhanced from one to numerous techniques in the course of 2021. After to begin with encrypting delicate info from the target and threatening to reveal it publicly except if a ransom is paid, attackers are now focusing on the victim’s partners and clients for ransom to optimize their revenue.
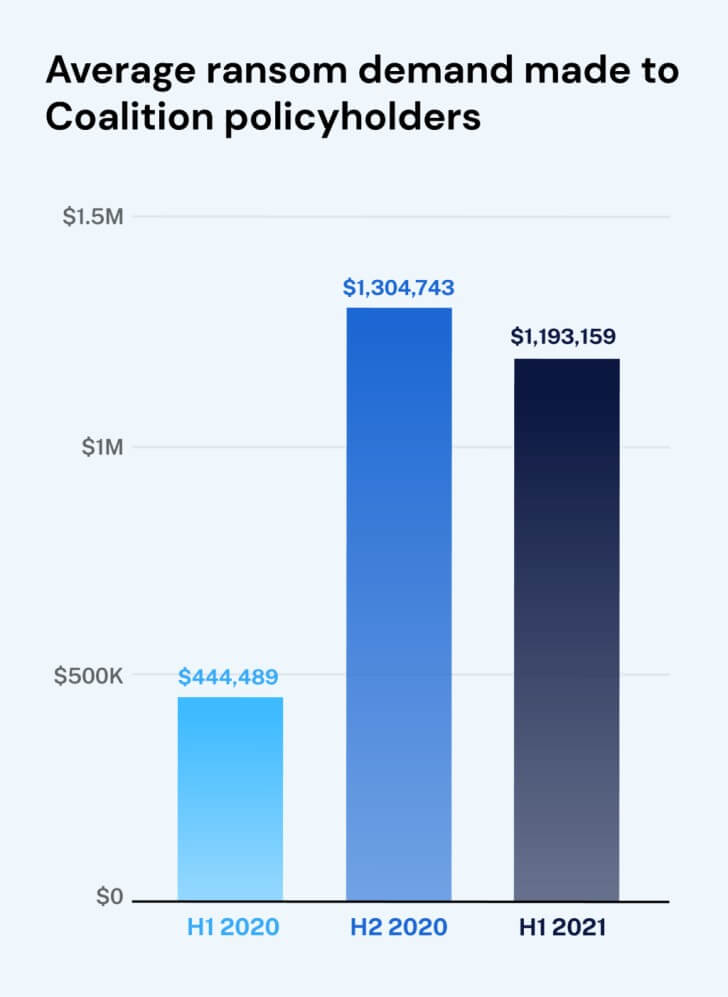
New exploration from Coalition uncovered that there was a 170% improve in the average ransom desire in the initial 50 % of 2021 in contrast to previous calendar year.
 Impression resource: venturebeat
Impression resource: venturebeat
It is likely to strike $100 million in 2022 – in accordance to the ENISA Danger Landscape 2021.
What’s more, cryptocurrency gets to be the option of spend-out approach simply because it claims a safe, rapid, and nameless channel for income transactions. Also, attackers shifted from Bitcoin to Monero as their selection owing to its increased anonymity.
Tips to protect against remaining a victim:
- Security consciousness schooling
- Use safe websites
- Protection-in-depth cybersecurity technique
- Vulnerability evaluation & penetration screening
2 — Cryptojacking
Another attack development in 2021 is cryptojacking, which is linked with the growing instability in the cryptocurrency current market. Offered the anonymity of cryptocurrencies, it has become a hassle-free and appealing means of exchange by attackers. In this attack, cybercriminals deploy hidden cryptojacking software package on to the target’s products, which steals from a cryptocurrency wallet. Siloscape, a new malware, which emerged in June 2021 targets Windows containers and generates destructive containers, hundreds cryptocurrency miners, which detect and steal cryptocurrency.
Tips to counteract cryptojacking:
- Apply web filters and blacklist IP addresses from cryptomining IP pools
- Acquire patches against effectively-known exploits
- Employ a strong vulnerability administration application
3 — Details Breaches
Delicate knowledge becoming stolen from businesses or consumers is practically nothing new, but how risk actors approach it has developed. Just as corporations embrace new systems to survive in the digital landscape, threat actors also harness advanced methods to exploit attacks – Deepfake technology, for instance.
Even though it is really not a new strategy, it has developed significantly. With MI and AI, Deepfake technology permits the digital generation of an individual’s likeness, which can then be made use of to impersonate the sufferer. AI and ML instruments make it possible to make synthetic variations of any voice or any movie.
Cybercube’s security researchers alerted that deep fake audio and video clip content material could develop into a big cyber menace to enterprises globally. Also, the popular destruction affiliated with this pretended content material is anticipated to raise in the coming years. It is also envisioned that the enhanced dependence on movie-primarily based interaction is the significant factor that motivates attackers to concentrate more on Deepfake technology.
Recommendations for Deepfake Monitoring and Elimination:
- Improved digital archiving to establish the bogus video and fake voice clips
- Implement Content material Authenticity Initiative to validate the creator as very well as origin of data
4 — Botnets
Newer botnets continue on to emerge as aged types maintain reworking to sidestep the recent security alternatives. This is mainly because cyber-criminals see a new paradigm with botnets-as-a-company in which bonnets can be leased/marketed to organizations or folks for nefarious makes use of and money gains.
Also, the existence of botnets in the cloud and mobile surroundings proposes a new likelihood that they may shortly be able to learn and exploit the weak spot on their individual in the patterns of person interactions. The amplified adoption of IoT and the absence of security when they are developed as nicely as deployed presents a further feasible frontier for botnet proliferation.
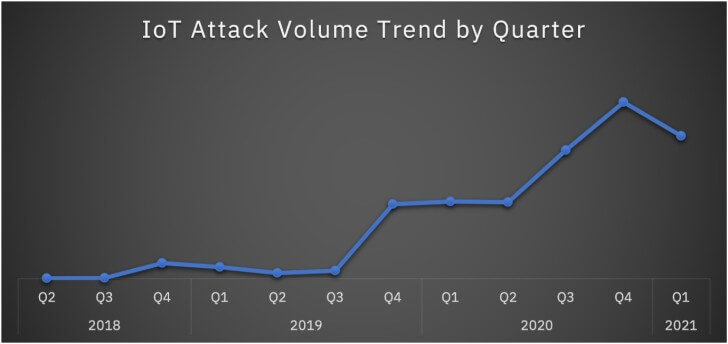
A latest report exposed there is a 500% increase in all round IoT attacks by prominent IoT botnets like Mirai and Mozi.
 Impression resource: Security Intelligence
Impression resource: Security Intelligence
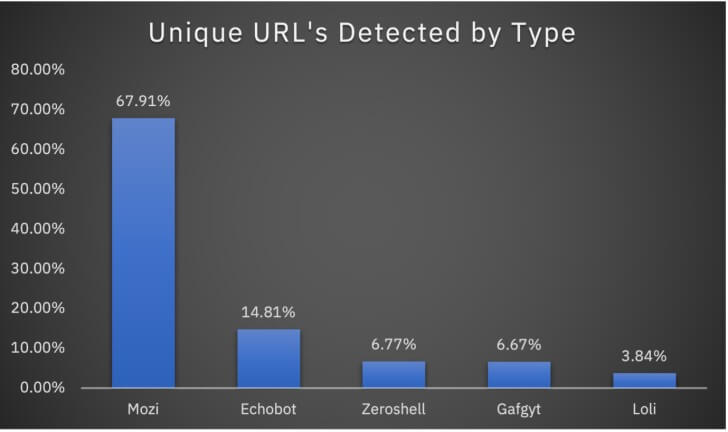
In 2020, the Mozi botnet attackaccounted for 89% of the IoT attacks – according to X-Pressure analysis. In addition to Mozi, several other botnets keep on to target the IoT landscape. Ecobot, Zeroshell, Gafgyt, and Loli are 4 notable botnets impacting firms all in excess of the planet.
 Impression source: Security Intelligence
Impression source: Security Intelligence
Tips to combat again:
- Make use of penetration testing
- Change your default IoT setting when putting in any new gadget
- Implement a strong patch administration application
- Exercise efficient bot security and mitigation technique
The Big Picture
New cyber threats are getting detected all the time, and they possess the possible to have an effect on any running system, including Linux, Windows, iOS, Mac OS, and Android. Additionally, new threats vectors are evolving thanks to likely vulnerabilities in the continual adoption of distant doing work and a rising selection of IoT devices staying linked.
This cyber danger landscape evolution has forced enterprises to improve their vulnerability management system, security tools, procedures, and capabilities to stay forward. Indusface AppTrana, a entirely managed Web Software and API protection (WAAP)addresses these problems and speeds up risk detection and response.
If you want to be proactive and actionable in shielding your details, remain informed of the current cyber security danger landscape!
Identified this posting attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to go through far more exclusive written content we write-up.
Some sections of this posting are sourced from:
thehackernews.com


 Iran’s Lyceum Hackers Target Telecoms, ISPs in Israel, Saudi Arabia, and Africa
Iran’s Lyceum Hackers Target Telecoms, ISPs in Israel, Saudi Arabia, and Africa