SolarWinds, the company checking software provider who located by itself at the epicenter of the most consequential source chain attacks, explained as several as 18,000 of its high-profile prospects could possibly have installed a tainted edition of its Orion products.
The acknowledgment arrives as section of a new submitting made by the firm to the US Securities and Trade Fee on Monday.
The Texas-based mostly business serves additional than 300,000 prospects throughout the world, which includes every single branch of the US navy and four-fifths of the Fortune 500 providers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The “incident was probable the result of a remarkably innovative, qualified and manual provide chain attack by an outdoors country point out,” SolarWinds reported in the regulatory disclosure, adding it “presently thinks the precise selection of prospects that may possibly have experienced an set up of the Orion products and solutions that contained this vulnerability to be less than 18,000.”
The corporation also reiterated in its security advisory that in addition to 2019.4 HF 5 and 2020.2 versions of SolarWinds Orion System, no other variations of the checking program or other non-Orion items were being impacted by the vulnerability.
Specifics regarding how the hackers penetrated SolarWinds’ possess network are continue to fuzzy, but the company pointed out in its submitting that it was alerted to a compromise of its Microsoft Place of work 365 email and office productivity accounts that it is presently investigating to determine how extended it existed and if the weak spot was “connected with the attack on its Orion program construct program.”
Troublingly, according to a report from security researcher Vinoth Kumar, it also seems that a publicly-obtainable SolarWinds GitHub repository was leaking FTP qualifications of the area “downloads.solarwinds.com,” as a result letting an attacker to probably add a malicious executable disguised as Orion computer software updates to the downloads portal. Even even worse, the FTP server was secured by a trivial password.
Pursuing Kumar’s liable disclosure final yr, the organization dealt with the misconfiguration on November 22, 2019.
The growth comes a working day immediately after cybersecurity firm FireEye mentioned it discovered a nine-thirty day period-prolonged worldwide intrusion marketing campaign concentrating on general public and non-public entities that introduce malicious code into genuine application updates for SolarWinds’ Orion application to crack into the companies’ networks and set up a backdoor named SUNBURST (“SolarWinds.Orion.Core.BusinessLayer.dll”).
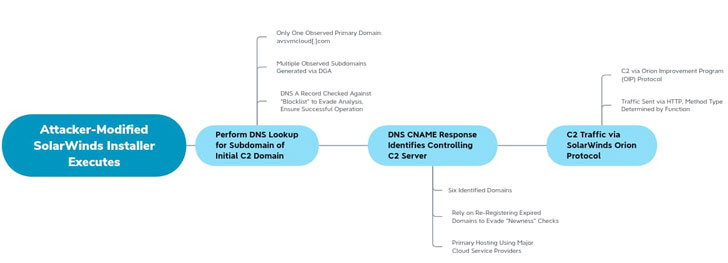
“The destructive DLL phone calls out to a distant network infrastructure using the domains avsvmcloud.com. to prepare feasible 2nd-stage payloads, move laterally in the business, and compromise or exfiltrate knowledge,” Microsoft mentioned in a generate-up.
The US Division of Homeland Security was breached, as were being the departments of Commerce and Treasury, Reuters claimed yesterday. The espionage marketing campaign also included the December 8 cyberattack on FireEye, even though it can be not right away distinct no matter whether the intrusion and exfiltration was a immediate consequence of a rogue SolarWinds update.
“The marketing campaign demonstrates top-tier operational tradecraft and resourcing dependable with state-sponsored threat actors,” claimed FireEye CEO Kevin Mandia. “These compromises are not self-propagating each individual of the attacks have to have meticulous arranging and manual conversation.”
When the fallout brought on by the hacking campaign is still unidentified, fingers have been pointed at APT29, a hacking collective affiliated with the Russian foreign intelligence service. FireEye, which is tracking the marketing campaign as “UNC2452,” has not connected the attack to Russia.
For its portion, SolarWinds is anticipated to issue a next hotfix afterwards today that replaces the susceptible part and adds several excess security enhancements.
“The SUNBURST marketing campaign signifies a uniquely distressing intrusion celebration with implications for a number of industries and network operators,” DomainTools’ Senior Security Researcher, Joe Slowik, said.
“The ubiquity of SolarWinds in massive networks, combined with the probably long dwell time of intrusions facilitated by this compromise, indicate victims of this marketing campaign need to have not only recuperate their SolarWinds instance, but may want to carry out common password resets, device recovery, and very similar restoration activity to fully evict an intruder.”
“By means of continual monitoring of network visitors and an comprehension of what hosts are speaking, defenders can leverage attacker weaknesses and dependencies to prevail over these usually complicated problems,” he included.
Identified this post exciting? Follow THN on Fb, Twitter and LinkedIn to read through much more unique information we post.
Some sections of this report are sourced from:
thehackernews.com


 Best VPN services 2020
Best VPN services 2020