As 5G networks are getting step by step rolled out in important towns throughout the earth, an examination of its network architecture has discovered a variety of possible weaknesses that could be exploited to carry out a slew of cyber assaults, which include denial-of-support (DoS) attacks to deprive subscribers of Internet entry and intercept details website traffic.
The conclusions form the foundation of a new “5G Standalone core security investigate” published by London-based cybersecurity organization Favourable Technologies currently, precisely six months right after the organization launched its “Vulnerabilities in LTE and 5G Networks 2020” report in June detailing significant affect flaws in LTE and 5G protocols.
“Vital factors of network security consist of appropriate configuration of devices, as effectively as authentication and authorization of network aspects,” Positive Technologies reported.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“In the absence of these elements, the network gets vulnerable [to] subscriber denial of services due to exploitation of vulnerabilities in the PFCP protocol,” and other shortcomings that could lead to the disclosure of special subscriber identifiers and profile info, and even use Internet products and services at a user’s expenditure without the need of their knowledge.
Security Positive aspects of 5G
Just one of the vital security gains presented by 5G is safety from stingray surveillance and encryption of International Cellular Subscriber Identity (IMSI) figures — exclusive identifiers that arrive with each and every SIM card for the intent of figuring out end users of a cellular network.
The 5G Core (5GC) also updates the IT protocol stack by utilizing Transmission Command Protocol (TCP) as the transport layer protocol in place of Stream Control Transmission Protocol (SCTP), HTTP/2 as a substitute for Diameter protocol for application layer security, and an added TLS layer for encrypted communication among all network functions.
Deployed possibly in standalone or non-standalone modes relying on their reliance on 4G Evolved Packet Core (EPC) technology, the 5G mobile network is a framework consisting of as a lot of as 9 network capabilities (NFs) that are responsible for registering subscribers, taking care of periods and subscriber profiles, storing subscriber information, and connecting the buyers (UE or person devices) to the internet through a base station (gNB).
But the scientists say this very stack of systems probably opens the door to attacks on subscribers and the operator’s network that could be exploited to phase male-in-the-middle and DoS attacks.
DoS and MitM Attacks
A problematic component of the process architecture is the interface devoted to session management (Session Management Function or SMF) through a protocol called Packet Forwarding Command Protocol (PFCP).
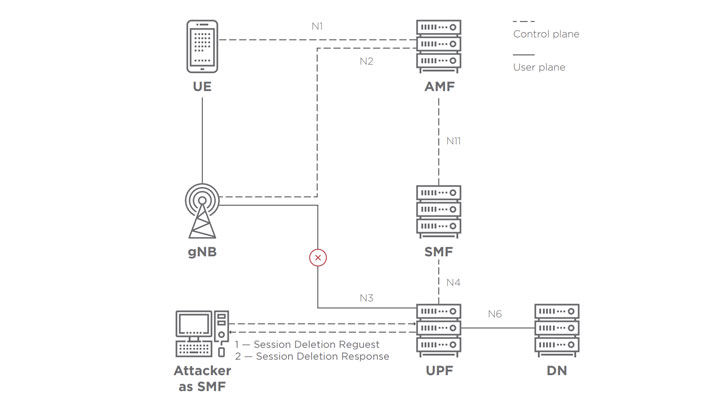
A negative actor can pick out to deliver a session deletion or modification ask for PFCP packet, creating a DoS situation that, in turn, qualified prospects to disruption of internet obtain (CVSS rating 6.1) and even interception of web targeted traffic (CVSS score 8.3).
Constructive Technologies also identified issues with the part of the 5G regular that governs Network Repository Operate (NRF), which allows registration and discovery of NFs in the handle aircraft, noting that the adversaries could insert an already present network perform in the repository to provide subscribers via an NF below their handle and entry consumer data (CVSS score 8.2).
In a various scenario, the lack of authorization in NRF could be abused to deregister critical factors by deleting their corresponding NF profiles from the retail outlet, ensuing in loss of assistance to subscribers.
Secretly Spy on Subscribers’ Place
Also of take note are a pair of subscriber authentication vulnerabilities that can be leveraged to disclose the Membership Long lasting Identifier (SUPI) allotted to just about every subscriber and provide the end-consumer using the leaked authentication facts by spoofing a foundation station.
Independently, a design and style quirk in the Consumer Information Administration (UDM) module that manages subscriber profile data could permit an adversary with “entry to the applicable interface […] hook up to the UDM directly or by impersonating a network support, and then extract all the necessary information and facts,” which include spot data (CVSS rating 7.4).
“Obtain to these info would severely jeopardize security: it permits the attacker to secretly spy on the subscriber, though the latter will never ever know what is likely on,” the scientists explained.
Last but not least, an attacker can impersonate the Accessibility and Mobility Administration Purpose (AMF) module that will take care of subscriber registration on the network by making use of a subscriber’s identification information and facts to develop new stealthy internet periods for which the subscriber will be billed (CVSS rating 8.2).
The Require for Evaluation, Monitoring, and Protection
There is certainly no doubting the security improvements made available by 5G, but it’s also critical that the 5G regular is sufficiently scrutinized as the selection of 5G network consumers carry on to mature every yr.
“Operators often make glitches in tools configuration with implications for security,” the scientists concluded. “An critical position is performed by machines sellers, which are responsible for the technical implementation of all the architected network safety characteristics.
“To avert the penalties of this sort of attacks, operators need to use timely protection actions, such as good configuration of machines, use of firewalls on the network edge, and security checking,” the scientists said.
Located this post appealing? Abide by THN on Fb, Twitter and LinkedIn to examine much more special material we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com


 What is Geocoding? — How to Find Coordinates of An Address
What is Geocoding? — How to Find Coordinates of An Address