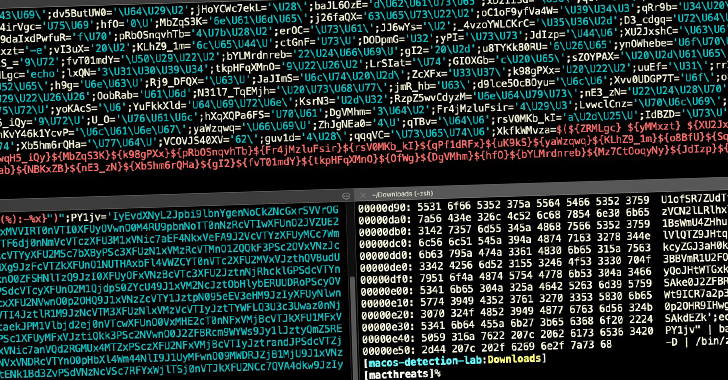
A new wave of attacks involving a infamous macOS adware loved ones has advanced to leverage around 150 exceptional samples in the wild in 2021 on your own, some of which have slipped previous Apple’s on-product malware scanner and even signed by its very own notarization company, highlighting the destructive software package ongoing attempts to adapt and evade detection.
“AdLoad,” as the malware is acknowledged, is a single of a number of widespread adware and bundleware loaders concentrating on macOS given that at minimum 2017 which is capable of backdooring an influenced method to obtain and install adware or probably unwelcome systems (PUPs), as nicely as amass and transmit info about victim devices.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The new iteration “proceeds to affect Mac consumers who depend entirely on Apple’s developed-in security manage XProtect for malware detection,” SentinelOne danger researcher Phil Stokes stated in an examination revealed previous 7 days. “As of today, however, XProtect arguably has around 11 unique signatures for AdLoad [but] the variant employed in this new campaign is undetected by any of individuals procedures.”
The 2021 model of AdLoad latches on to persistence and executable names that use a distinctive file extension sample (.system or .support), enabling the malware to get all-around additional security protections incorporated by Apple, in the end ensuing in the set up of a persistence agent, which, in switch, triggers an attack chain to deploy destructive droppers that masquerade as a bogus Participant.app to put in malware.
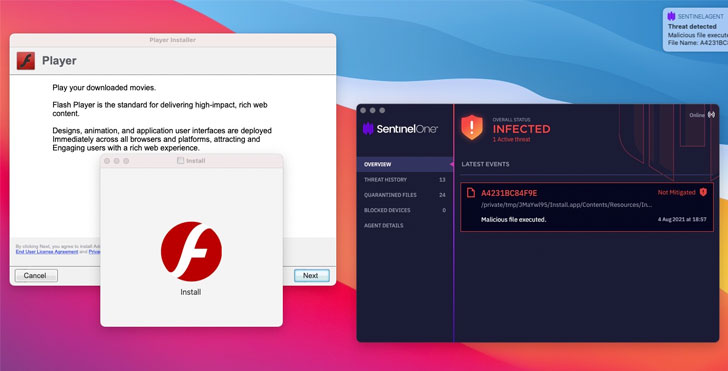
What is actually a lot more, the droppers are signed with a valid signature working with developer certificates, prompting Apple to revoke the certificates “inside of a matter of times (in some cases hours) of samples staying noticed on VirusTotal, presenting some belated and non permanent security from even further infections by those distinct signed samples by suggests of Gatekeeper and OCSP signature checks,” Stokes mentioned.

SentinelOne said it detected new samples signed with refreshing certificates in a few of hours and days, contacting it a “activity of whack-a-mole.” Initially samples of AdLoad are stated to have appeared as early as November 2020, with standard even further occurrences across the to start with fifty percent of 2021, adopted by a sharp uptick all through July and, in unique, the early weeks of August 2021.
AdLoad is between the malware family members, along with Shlayer, that’s been regarded to bypass XProtect and infect Macs with other destructive payloads. In April 2021, Apple dealt with an actively exploited zero-working day flaw in its Gatekeeper assistance (CVE-2021-30657) that was abused by the Shlayer operators to deploy unapproved computer software on Macs.
“Malware on macOS is a problem that the device producer is having difficulties to cope with,” Stokes said. “The fact that hundreds of special samples of a properly-identified adware variant have been circulating for at least 10 months and still continue to continue to be undetected by Apple’s constructed-in malware scanner demonstrates the necessity of incorporating even further endpoint security controls to Mac gadgets.”
Uncovered this write-up interesting? Comply with THN on Facebook, Twitter and LinkedIn to browse more distinctive articles we submit.
Some parts of this post are sourced from:
thehackernews.com

 New Glowworm Attack Recovers Device’s Sound from Its LED Power Indicator
New Glowworm Attack Recovers Device’s Sound from Its LED Power Indicator