Amazon previously this April addressed a critical vulnerability in its Kindle e-e-book reader platform that could have been potentially exploited to just take entire manage above a user’s device, ensuing in the theft of sensitive facts by just deploying a destructive e-book.
“By sending Kindle users a solitary destructive e-e book, a menace actor could have stolen any info saved on the machine, from Amazon account qualifications to billing details,” Yaniv Balmas, head of cyber exploration at Look at Position, stated in an emailed statement. “The security vulnerabilities let an attacker to focus on a really specific audience.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In other terms, if a menace actor desired to target a particular team of individuals or demographic, it truly is possible for the adversary to pick a preferred e-ebook in a language or dialect that’s greatly spoken amid the group to tailor and orchestrate a very specific cyber attack.
Upon responsibly disclosing the issue to Amazon in February 2021, the retail and amusement big revealed a deal with as aspect of its 5.13.5 version of Kindle firmware in April 2021.
Attacks exploiting the flaw begin by sending a destructive e-e-book to an supposed target, who, upon the reserve, triggers the infection sequence sans any interaction, letting the undesirable actor to delete the user’s library, gain complete access to the Amazon account, or change the Kindle into a bot for placing other devices in the target’s neighborhood network.
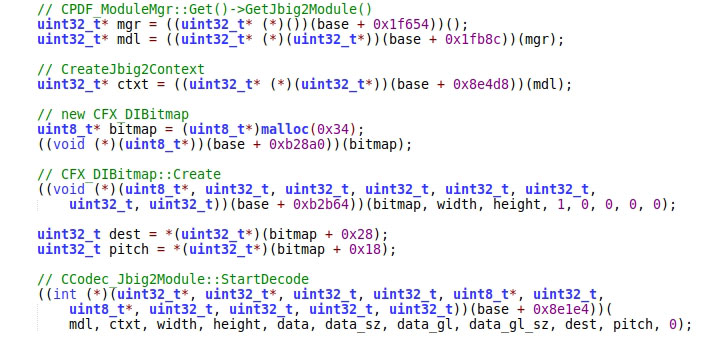 Heap overflow vulnerability in the JBIG2Globals decoding algorithm
Heap overflow vulnerability in the JBIG2Globals decoding algorithm
The issue resides in the firmware’s e-book parsing framework, exclusively in the implementation associated with how PDF files are opened, allowing an attacker to execute a malicious payload on the product.
This is made possible, thanks to a heap overflow vulnerability in the PDF rendering purpose (CVE-2021-30354), which can be leveraged to obtain arbitrary publish primitive, and a nearby privilege escalation flaw in the Kindle software manager assistance (CVE-2021-30355) that enables the risk actor to chain the two flaws to run malware-laced code as a root person.

Previously this January, Amazon fixed equivalent weaknesses — collectively named “KindleDrip” — that could have authorized an attacker to take command of victims’ equipment by delivering a malicious e-guide to the targets and make unauthorized buys.
“Kindle, like other IoT equipment, are normally considered of as innocuous and disregarded as security risks,” Balmas explained. “These IoT devices are vulnerable to the very same attacks as pcs. Everyone should really be informed of the cyber risks in making use of everything connected to the computer system, in particular one thing as ubiquitous as Amazon’s Kindle.”
Located this article exciting? Adhere to THN on Fb, Twitter and LinkedIn to study far more exceptional content we write-up.
Some pieces of this short article are sourced from:
thehackernews.com


 Microsoft tests experimental “Super Duper Secure Mode” for Edge browser
Microsoft tests experimental “Super Duper Secure Mode” for Edge browser