The operators at the rear of the BlackRock cellular malware have surfaced back again with a new Android banking trojan termed ERMAC that targets Poland and has its roots in the notorious Cerberus malware, according to the latest investigate.
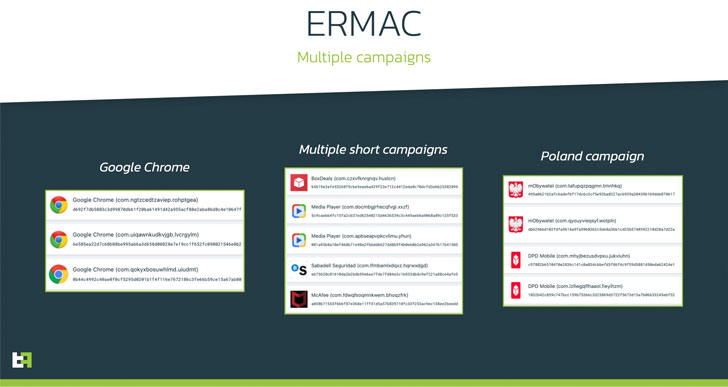
“The new trojan previously has lively distribution strategies and is concentrating on 378 banking and wallet apps with overlays,” ThreatFabric’s CEO Cengiz Han Sahin said in an emailed statement. Initial campaigns involving ERMAC are thought to have started in late August underneath the guise of the Google Chrome app.
Given that then, the attacks have expanded to contain a variety of applications such as banking, media players, shipping solutions, governing administration purposes, and antivirus answers like McAfee.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Practically totally dependent on the infamous banking trojan Cerberus, the Dutch cybersecurity firm’s conclusions arrive from discussion board posts produced by an actor named DukeEugene previous month on August 17, inviting future prospects to “rent a new android botnet with large performance to a slender circle of men and women” for $3,000 a thirty day period.
DukeEugene is also regarded as the actor powering the BlackRock campaign that arrived to light-weight in July 2020. That includes an array of details theft abilities, the infostealer and keylogger originate from a different banking pressure known as Xerxes — which by itself is a pressure of the LokiBot Android banking Trojan — with the malware’s supply code produced public by its author close to May perhaps 2019.
Cerberus, in September 2020, experienced its possess supply code introduced as a totally free remote accessibility trojan (RAT) on underground hacking message boards pursuing a unsuccessful auction that sought $100,000 for the developer.

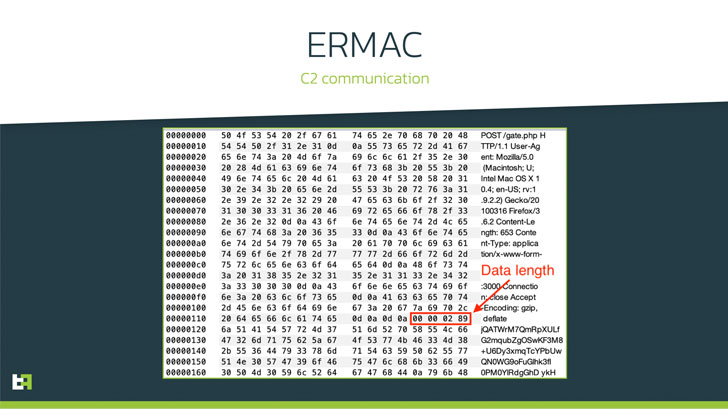
ThreatFabric also highlighted the cessation of clean BlackRock samples considering that the emergence of ERMAC, boosting the risk that “DukeEugene switched from using BlackRock in its operations to ERMAC.” Apart from sharing similarities with Cerberus, the freshly uncovered pressure is notable for its use of obfuscation procedures and Blowfish encryption plan to connect with the command-and-handle server.
ERMAC, like its progenitor and other banking malware, is designed to steal get in touch with data, textual content messages, open arbitrary programs, and trigger overlay attacks in opposition to a multitude of money apps to swipe login qualifications. In addition, it has formulated new options that allow the destructive software package to apparent the cache of a unique application and steal accounts stored on the machine.
“The story of ERMAC demonstrates just one far more time how malware source code leaks can lead not only to slow evaporation of the malware loved ones but also deliver new threats/actors to the risk landscape,” the scientists mentioned. “Whilst it lacks some powerful options like RAT, it stays a threat for cellular banking users and fiscal institutions all in excess of the entire world.”
Discovered this write-up attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to read more unique material we submit.
Some components of this short article are sourced from:
thehackernews.com

 How Does DMARC Prevent Phishing?
How Does DMARC Prevent Phishing?