Researchers have found a new Android banking malware that targets Brazil’s Itaú Unibanco with the assistance of lookalike Google Enjoy Retailer pages to carry out fraudulent economical transactions on sufferer devices without their expertise.
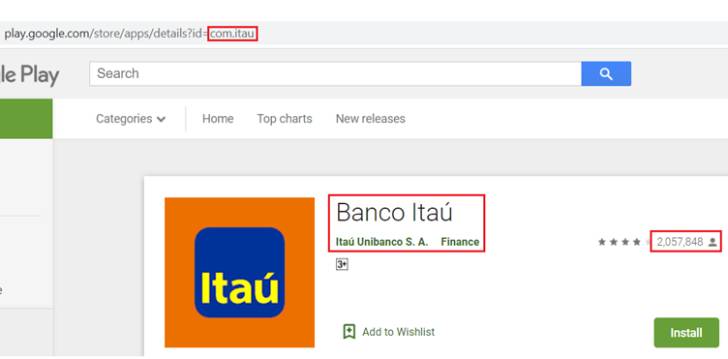
“This application has a related icon and identify that could trick users into considering it is a genuine app related to Itaú Unibanco,” Cyble researchers said in a report revealed last 7 days. “The [threat actor] has created a bogus Google Engage in Retail store page and hosted the malware that targets Itaú Unibanco on it less than the title ‘sincronizador.apk.'”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The tactic of leveraging bogus application shop webpages as a entice is not new. In March, Meta (beforehand Fb) disclosed information of an attack marketing campaign that employed its system as portion of a broader procedure to spy on Uyghur Muslims making use of rogue 3rd-party internet websites that employed replica domains for common information portals and internet sites designed to resemble third-party Android application stores, where attackers put bogus keyboard, prayer, and dictionary apps that may possibly attractiveness to the targets.
In the latest instance noticed by Cyble, the phony URL not only impersonates the official Android application marketplace, but also hosts the malware-laced Itaú Unibanco application, in addition to professing that the app has experienced 1,895,897 downloads.
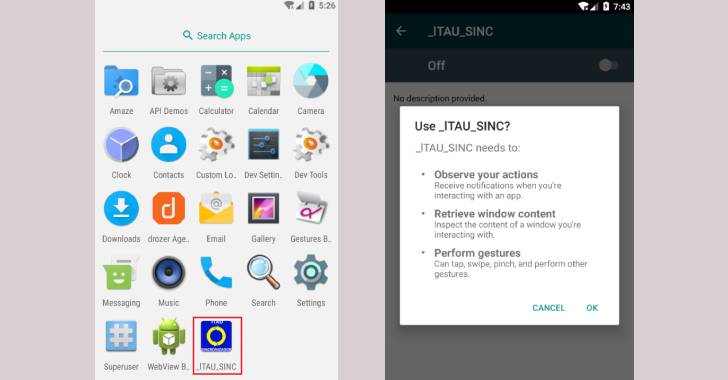
Consumers who set up and start the imposter application from the intended Google Participate in Retail store website page are subsequently prompted to help accessibility companies as perfectly as other intrusive permissions that enable the malware to accessibility notifications, retrieve window written content, and perform faucet and swipe gestures.
The objective of the trojan, for each the scientists, is to conduct fraudulent monetary transactions on the genuine Itaú Unibanco software by tampering with the user’s input fields, signing up for a lengthy checklist of banking malware that abuse the accessibility API. Google, for its portion, has started imposing new limitations to restrict the use of these types of permissions that allow apps to capture sensitive facts from Android gadgets.
This is far from the 1st time the Sao Paulo-centered financial expert services company has arrive underneath the radar of economically-enthusiastic risk groups. Previously this April, ESET exposed a new banking trojan dubbed Janeleiro that was noticed placing company users in Brazil at least because 2019 across many sectors such as engineering, health care, retail, producing, finance, transportation, and governing administration.
“Risk Actors continually adapt their solutions to stay clear of detection and uncover new strategies to goal customers as a result of progressively sophisticated techniques. Such malicious applications often masquerade as legit purposes to trick consumers into installing them,” the researchers stated.
“Users should put in purposes only soon after verifying their authenticity and set up them completely from the official Google Enjoy Retail outlet and other trustworthy portals to avoid this kind of attacks.”
Found this short article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to study additional unique material we submit.
Some sections of this report are sourced from:
thehackernews.com



 Russia Fines Google $100m Over “Illegal” Content
Russia Fines Google $100m Over “Illegal” Content