On-line account generation poses a challenge for engineers and process architects: if you place up too lots of barriers, you risk turning away genuine buyers. Make it way too effortless, and you risk fraud or bogus accounts.
The Problem with Identity Verification
The standard model of on-line identification – username/email and password – has very long outlived its usefulness. This is how multi-factor or two-factor authentication (MFA or 2FA) has arrive into engage in, to patch up vulnerabilities of the so-referred to as information-dependent design, normally by SMS passcode to confirm possession of a cellular phone selection.
The simplicity of SMS-based verification has taken applications by storm – it really is the default selection, as most people have a cell phone. Nevertheless lousy actors have uncovered how to exploit this verification approach, top to the menace of SIM swap fraud, which is alarmingly uncomplicated to pull off and mounting promptly in incidents.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
There’s been no lack of effort and hard work in getting a far more safe factor that is nevertheless universal. For case in point, biometrics are potent, but not just about every person has a smartphone that can get a fingerprint or facial area ID. Authenticator applications are a sturdy choice, but they’re sophisticated and not appropriate for casual consumers. In the same way, hardware tokens are very safe, but only for the very tech-minded: it really is not practical for the average buyer to acquire and have one.
Introducing SIM-primarily based Verification
In some cases the most straightforward alternative is already in our palms. SMS by yourself may not be secure, but cellular phone numbers tethered to a SIM card are: they are a distinctive pairing that is tough to tamper with or copy.
SIM-dependent authentication is an identity breakthrough. It is now achievable to prevent fraud and bogus accounts whilst seamlessly verifying cell customers employing the most cryptographically protected identifier they presently have – the SIM card embedded in their cell units.
The Most recent Strategy to Reduce Account Takeovers and SIM Swap Fraud
If you might be worried about SIM swap fraud as a menace to your buyers, you would be ideal. SIM swap fraud is a escalating issue with significant money effects – FinTechs and cryptocurrency wallets have been specially targeted, but any system that works by using SMS to confirm id is at risk. All it requires is just one compromised consumer to trigger key help issues and model destruction.
SIM-dependent authentication presents a very simple correct, with an instant, actionable response. Fraudsters try to obtain their victims’ accounts ordinarily inside 24 hrs, so by examining for SIM swap exercise inside of the final 7 times, SubscriberCheck by tru.ID can detect them at the gate.
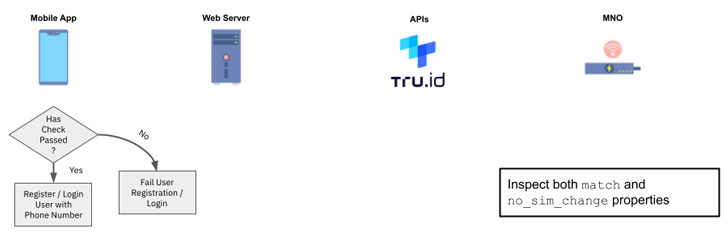
If there has been a adjust of SIM card, that adjust will be flagged, and you can apply action-up security person journeys or protect against accessibility completely.
How the SIM-Authentication API Operates
The SIM card within just the phone is by now authenticated with the Cellular Network Operator (MNO). SIM authentication makes it possible for cell shoppers to make and obtain phone phone calls and join to the Internet.
SubscriberCheck from tru.ID hooks into the very same authentication system as MNOs. As a outcome, the tru.ID API does two things. First of all, it verifies that the cell selection is active and paired to the SIM card on the mobile phone. As portion of this verification, the API also retrieves details if the SIM card associated with the phone variety has lately changed. These checks can be built-in very easily with APIs and SDKs.
Effective and personal: Listed here is How to use SubscriberCheck
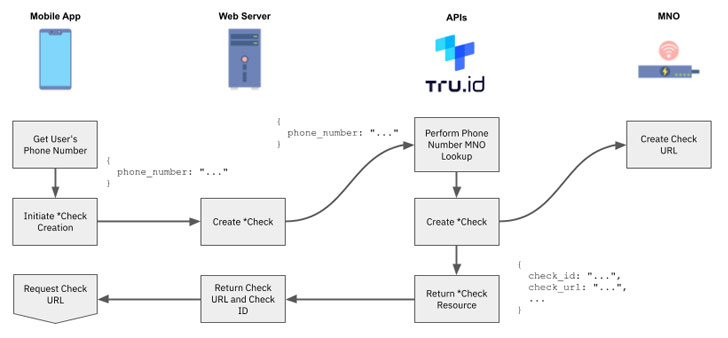
1 — Examination the tru.ID API with a phone range you’d like to confirm and check SIM standing on.
2 — The tru.ID platform performs a lookup on the phone amount to ascertain which MNO it is linked with.
3 — tru.ID then asks that MNO for a unique Check URL that will be applied as portion of a mobile authentication workflow.
4 — The tru.ID platform outlets that MNO Look at URL and returns a tru.ID Examine URL.
5 — Ask for the tru.ID Examine URL inside of the mobile software utilizing the tru.ID SDK for Android, 6, iOS, or React Indigenous. It is really significant to use the SDK because it forces the web request around the authenticated cellular details session.
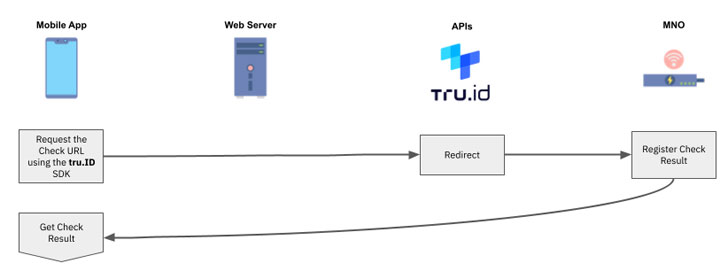
6 — The MNO will get the web request by way of a redirect from the tru.ID system. The MNO then decides if the phone selection related with the authenticated cell information session matches the phone quantity connected with the asked for Test URL. If it does, then the phone range has been properly verified.
7 — At this issue the tru.ID system also performs a SIM card improve lookup and shops the final result.
8 — As soon as the Look at URL ask for has done and the SIM improve facts retrieved, the cell application can request the result of the phone verification from the tru.ID API.
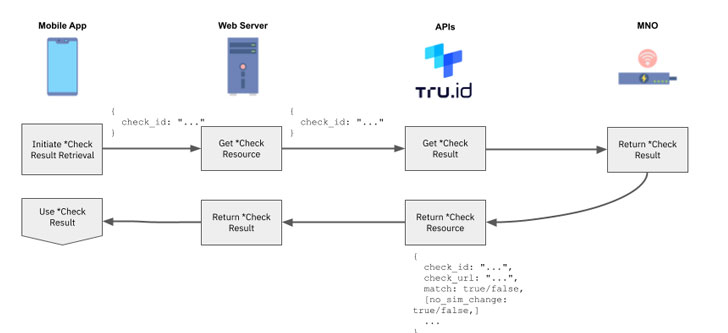
9 — Use the phone verification match and SIM card alter `no_sim_change` properties in your application logic.
How to Get Started
Of program, viewing is believing. You can start testing now for free and make your initially API connect with inside of minutes – just indicator up with tru.ID and test the documentation for your tutorial to receiving began.
Identified this write-up interesting? Abide by THN on Facebook, Twitter and LinkedIn to go through more exclusive written content we article.
Some sections of this short article are sourced from:
thehackernews.com


 Google now requires app developers to verify their address and use 2FA
Google now requires app developers to verify their address and use 2FA