A new hugely able and persistent threat actor has been focusing on main large-profile community and personal entities in the U.S. as portion of a collection of qualified cyber intrusion attacks by exploiting internet-facing Microsoft Internet Information and facts Expert services (IIS) servers to infiltrate their networks.
Israeli cybersecurity organization Sygnia, which recognized the marketing campaign, is monitoring the advanced, stealthy adversary less than the moniker “Praying Mantis” or “TG2021.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
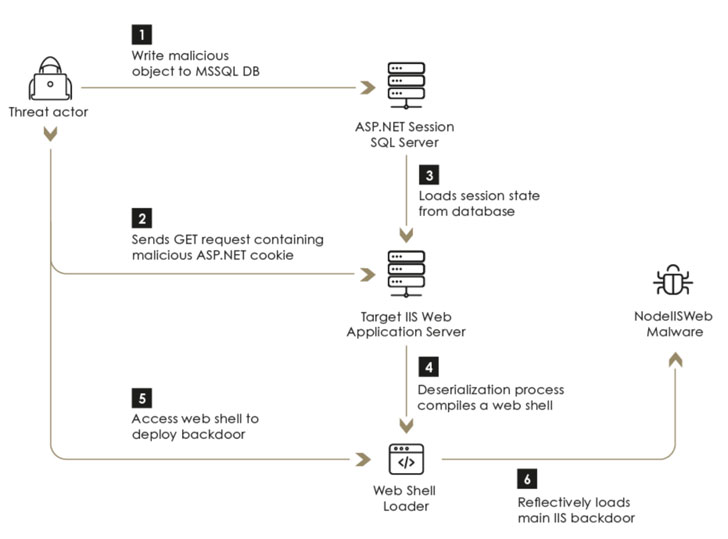
“TG1021 uses a tailor made-made malware framework, created close to a popular main, tailor-built for IIS servers. The toolset is absolutely volatile, reflectively loaded into an afflicted machine’s memory and leaves little-to-no trace on contaminated targets,” the scientists mentioned. “The threat actor also uses an more stealthy backdoor and a number of post-exploitations modules to execute network reconnaissance, elevate privileges, and move laterally in just networks.”
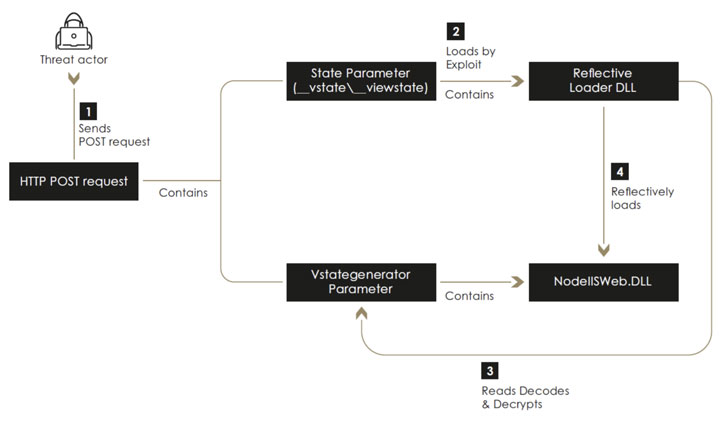
Besides exhibiting abilities that exhibit a important effort and hard work to prevent detection by actively interfering with logging mechanisms and efficiently evading commercial endpoint detection and response (EDR) programs, the menace actor has been known to leverage an arsenal of ASP.NET web software exploits to get an original foothold and backdoor the servers by executing a subtle implant named “NodeIISWeb” that is made to load customized DLLs as perfectly as intercept and take care of HTTP requests obtained by the server.
The vulnerabilities are taken benefit of by the actor incorporate:
- Checkbox Survey RCE Exploit (CVE-2021-27852)
- VIEWSTATE Deserialization Exploit
- Altserialization Insecure Deserialization
- Telerik-UI Exploit (CVE-2019-18935 and CVE-2017-11317)

Curiously, Sygnia’s investigation into TG1021’s practices, techniques, and strategies (TTPs) have unearthed “important overlaps” to individuals of a country-sponsored actor named “Copy-Paste Compromises,” as in-depth in an advisory unveiled by the Australian Cyber Security Centre (ACSC) in June 2020, which described a cyber campaign concentrating on community-experiencing infrastructure largely by means of the use of unpatched flaws in Telerik UI and IIS servers. Nevertheless, a official attribution is nevertheless to be made.
“Praying Mantis, which has been noticed focusing on superior-profile public and private entities in two major Western markets, exemplifies a growing craze of cyber criminals using innovative, country-point out attack strategies to target professional organizations,” the researchers mentioned. “Continuous forensics activities and well timed incident reaction are necessary to determining and effectively defending networks from attacks by comparable danger actors.”
Found this report appealing? Abide by THN on Facebook, Twitter and LinkedIn to browse much more distinctive information we submit.
Some sections of this write-up are sourced from:
thehackernews.com

 PyPI Python Package Repository Patches Critical Supply Chain Flaw
PyPI Python Package Repository Patches Critical Supply Chain Flaw