A “perhaps devastating and challenging-to-detect risk” could be abused by attackers to accumulate users’ browser fingerprinting info with the intention of spoofing the victims with out their knowledge, so efficiently compromising their privacy.
Teachers from Texas A&M University dubbed the attack technique “Gummy Browsers,” likening it to a nearly 20-yr-aged “Gummy Fingers” procedure that can impersonate a user’s fingerprint biometrics.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
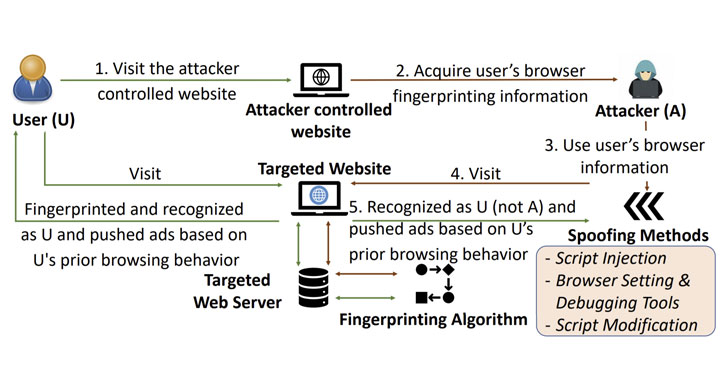
“The notion is that the attacker 𝐴 very first tends to make the consumer 𝑈 link to his web site (or to a very well-identified web site the attacker controls) and transparently collects the information from 𝑈 that is employed for fingerprinting functions (just like any fingerprinting site 𝑊 collects this facts),” the researchers outlined. “Then, 𝐴 orchestrates a browser on his have equipment to replicate and transmit the exact same fingerprinting info when connecting to 𝑊, fooling 𝑊 to imagine that 𝑈 is the one requesting the company somewhat than 𝐴.”
Browser fingerprinting, also termed equipment fingerprinting, refers to a monitoring method that is utilized to uniquely establish internet buyers by collecting characteristics about the software program and hardware of a remote computing program — these kinds of as the decision of browser, timezone, default language, display screen resolution, add-ons, installed fonts, and even tastes — as well as behavioral properties that emerge when interacting with the web browser of the system.
Consequently in the event, the website populates focused adverts centered on only the users’ browser fingerprints, it could final result in a scenario where the distant adversary can profile any concentrate on of fascination by manipulating their personal fingerprints to match that of the victim for prolonged intervals of time, all the though the user and the site stay oblivious to the attack.
By exploiting the fact that the server treats the attacker’s browser as the victim’s browser, not only would the previous receive exact or equivalent ads like that of the impersonated target, it also will allow the destructive actor to infer delicate information and facts about the consumer (e.g., gender, age team, health and fitness ailment, interests, salary level, and so on.) and establish a private behavioral profile.
In experimental tests, the researchers identified that the attack technique reached regular false-beneficial rates of higher than .95, indicating that most of the spoofed fingerprints have been misrecognized as genuine ones, efficiently tricking the digital fingerprinting algorithms. A consequence of this sort of an attack is a breach of ad privacy and a bypass of defensive mechanisms put in location to authenticate users and detect fraud.
“The impression of Gummy Browsers can be devastating and lasting on the on the web security and privacy of the consumers, specifically supplied that browser-fingerprinting is beginning to get commonly adopted in the actual earth,” the researchers concluded. “In light of this attack, our get the job done raises the dilemma of no matter whether browser fingerprinting is safe and sound to deploy on a big scale.”
Discovered this short article appealing? Follow THN on Facebook, Twitter and LinkedIn to browse far more distinctive articles we article.
Some areas of this article are sourced from:
thehackernews.com

 Hardware-grade enterprise authentication without hardware: new SIM security solution for IAM
Hardware-grade enterprise authentication without hardware: new SIM security solution for IAM