Cybersecurity researchers have disclosed an unpatched security vulnerability in the protocol utilized by Microsoft Azure Lively Directory that prospective adversaries could abuse to stage undetected brute-drive attacks.
“This flaw makes it possible for risk actors to execute single-factor brute-pressure attacks versus Azure Active Listing (Azure Ad) without generating sign-in activities in the qualified organization’s tenant,” scientists from Secureworks Counter Menace Unit (CTU) mentioned in a report posted on Wednesday.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Azure Lively Listing is Microsoft’s company cloud-dependent identification and obtain management (IAM) remedy created for single indication-on (SSO) and multi-factor authentication. It is really also a main ingredient of Microsoft 365 (previously Place of work 365), with abilities to offer authentication to other programs by using OAuth.
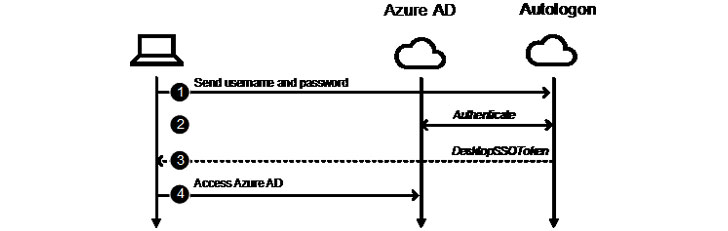
The weak point resides in the Seamless One Indicator-On characteristic that allows workers to routinely signal when employing their company gadgets that are connected to enterprise networks devoid of having to enter any passwords. Seamless SSO is also an “opportunistic feature” in that if the system fails, the login falls again to the default habits, whereby the user wants to enter their password on the indicator-in web site.
To reach this, the system relies on the Kerberos protocol to search up the corresponding person item in Azure Advertisement and issue a ticket-granting ticket (TGT), permitting the user to obtain the source in issue. But for users of Trade On line with Business clients older than the Business office 2013 May perhaps 2015 update, the authentication is carried by a password-centered endpoint identified as “UserNameMixed” that possibly generates an access token or an error code depending on regardless of whether the qualifications are valid.

It’s these mistake codes exactly where the flaw stems from. Whilst effective authentication activities make indicator-ins logs upon sending the entry tokens, “Autologon’s authentication to Azure Ad is not logged,” making it possible for the omission to be leveraged for undetected brute-power attacks via the UserNameMixed endpoint.
Secureworks mentioned it notified Microsoft of the issue on June 29, only for Microsoft to accept the conduct on July 21 as “by design.” We have achieved out to the business for further comment, and we will update the story if we listen to again.
Identified this report fascinating? Stick to THN on Fb, Twitter and LinkedIn to read far more special articles we submit.
Some sections of this short article are sourced from:
thehackernews.com


 Incentivizing Developers is the Key to Better Security Practices
Incentivizing Developers is the Key to Better Security Practices