Cybersecurity researchers have identified various security vulnerabilities in Zimbra email collaboration application that could be possibly exploited to compromise email accounts by sending a destructive message and even realize a entire takeover of the mail server when hosted on a cloud infrastructure.
The flaws — tracked as CVE-2021-35208 and CVE-2021-35208 — were being found and documented in Zimbra 8.8.15 by researchers from code high quality and security solutions provider SonarSource in Might 2021. Mitigations have given that been produced in Zimbra variations 8.8.15 Patch 23 and 9.. Patch 16.
- CVE-2021-35208 (CVSS rating: 5.4) – Stored XSS Vulnerability in ZmMailMsgView.java
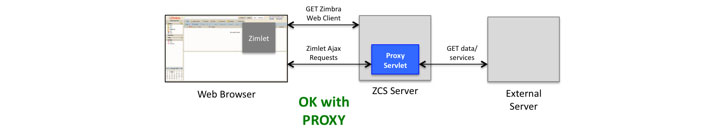
- CVE-2021-35209 (CVSS rating: 6.1) – Proxy Servlet Open up Redirect Vulnerability
“A mix of these vulnerabilities could empower an unauthenticated attacker to compromise a entire Zimbra webmail server of a focused group,” explained SonarSource vulnerability researcher, Simon Scannell, who determined the security weaknesses. “As a end result, an attacker would gain unrestricted accessibility to all despatched and gained e-mails of all employees.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Zimbra is a cloud-dependent email, calendar, and collaboration suite for enterprises and is available the two as an open-resource edition and a commercially supported model with more functions this kind of as a proprietary connector API to synchronize mail, calendar, and contacts to Microsoft Outlook, between other people. It truly is used by around 200,000 firms across 160 nations.
CVE-2021-35208 worries a cross-web page scripting (XSS) vulnerability in the Calendar Invite ingredient that can be induced in a victim’s browser on viewing a specifically-crafted email information containing a JavaScript payload that, when executed, grants accessibility to the target’s total inbox as perfectly as the web shopper session, which can then be abused to launch further attacks.
The issue stems from the fact that the Zimbra web customers — an Ajax-centered desktop consumer, a static HTML client, and a cellular-optimized consumer — execute the sanitization of the HTML written content of incoming emails on the server-aspect and in a method that allows a negative actor to inject rogue JavaScript code.
“The downside of making use of server-facet sanitization is that all three clients may renovate the trusted HTML of an email later on to screen it in their exceptional way,” Scannell stated. “Transformation of already sanitized HTML inputs can lead to corruption of the HTML and then to XSS attacks.”

On the other hand, CVE-2021-35208 relates to a server aspect request forgery (SSRF) attack whereby an authenticated member of an business can chain the flaw with the aforementioned XSS issue to redirect the HTTP customer applied by Zimbra to an arbitrary URL and extract sensitive information and facts from the cloud, including Google Cloud API entry tokens and IAM credentials from AWS, foremost to its compromise.
“Zimbra would like to alert its customers that it is attainable for them to introduce an SSRF security vulnerability in the Proxy Servlet,” the organization pointed out in its advisory. “If this servlet is configured to allow for a individual area (by means of zimbraProxyAllowedDomains configuration placing), and that area resolves to an inner IP handle (these as 127…1), an attacker could maybe obtain companies running on a different port on the identical server, which would ordinarily not be exposed publicly.”
Discovered this posting appealing? Follow THN on Facebook, Twitter and LinkedIn to go through additional distinctive content material we article.
Some areas of this post are sourced from:
thehackernews.com


 Three Zero-Day Bugs Plague Kaseya Unitrends Backup Servers
Three Zero-Day Bugs Plague Kaseya Unitrends Backup Servers