A recently uncovered wave of malware attacks has been noticed applying a assortment of strategies to enslave vulnerable devices with uncomplicated-to-guess administrative qualifications to co-choose them into a network with the objective of illegally mining cryptocurrency.
“The malware’s principal tactic is to unfold by using advantage of vulnerable devices and weak administrative qualifications. Once they’ve been infected, these units are then utilized to mine cryptocurrency,” Akamai security researcher Larry Cashdollar claimed in a create-up posted previous week.
The PHP malware — codenamed “Capoae” (short for “Сканирование,” the Russian word for “Scanning”) — is mentioned to be shipped to the hosts through a backdoored addition to a WordPress plugin known as “down load-keep track of,” which receives installed right after productively brute-forcing WordPress admin credentials. The attacks also require the deployment of a Golang binary with decryption performance, with the obfuscated payloads retrieved by leveraging the trojanized plugin to make a GET ask for from an actor-controlled area.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
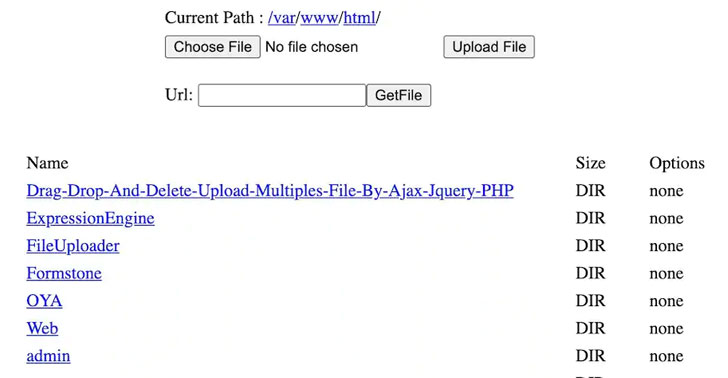
Also provided is a attribute to decrypted and execute additional payloads, when the Golang binary requires advantage of exploits for numerous remote code execution flaws in Oracle WebLogic Server (CVE-2020-14882), NoneCms (CVE-2018-20062), and Jenkins (CVE-2019-1003029 and CVE-2019-1003030) to brute drive its way into units working SSH and ultimately start the XMRig mining program.

What is far more, the attack chain stands out for its persistence methods, which includes selecting a genuine-wanting procedure path on the disk where method binaries are most likely to be identified as properly as making a random 6-character filename which is then subsequently made use of to copy alone into the new place on the method just before deleting the malware upon execution.
“The Capoae campaign’s use of a number of vulnerabilities and techniques highlights just how intent these operators are on obtaining a foothold on as several machines as feasible,” Cashdollar explained. “The very good news is, the identical tactics we endorse for most businesses to retain techniques and networks protected continue to utilize in this article.”
“Do not use weak or default credentials for servers or deployed programs,” Cashdollar included. “Ensure you are maintaining people deployed programs up to date with the most current security patches and look at in on them from time to time. Preserving an eye out for larger than typical process resource use, odd/sudden running procedures, suspicious artifacts and suspicious access log entries, etc., will support you probably recognize compromised machines.”
Identified this write-up exciting? Adhere to THN on Fb, Twitter and LinkedIn to study much more special articles we put up.
Some elements of this write-up are sourced from:
thehackernews.com

 MoD data breach ‘put lives of Afghan interpreters at risk’
MoD data breach ‘put lives of Afghan interpreters at risk’