A threat actor thought to be functioning on behalf of Chinese state-sponsored interests was just lately noticed focusing on a Russia-based defense contractor included in building nuclear submarines for the naval arm of the Russian Armed Forces.
The phishing attack, which singled out a standard director doing the job at the Rubin Style and design Bureau, leveraged the notorious “Royal Street” Wealthy Text Structure (RTF) weaponizer to produce a formerly undocumented Windows backdoor dubbed “PortDoor,” according to Cybereason’s Nocturnus threat intelligence staff.
“Portdoor has various functionalities, like the means to do reconnaissance, focus on profiling, shipping of extra payloads, privilege escalation, system manipulation static detection antivirus evasion, one particular-byte XOR encryption, AES-encrypted details exfiltration and extra,” the scientists mentioned in a create-up on Friday.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

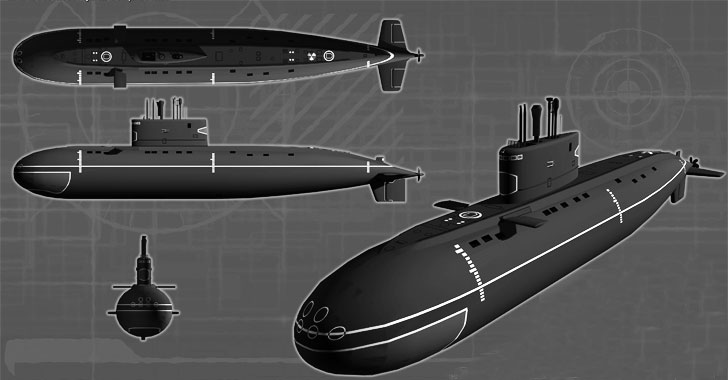
Rubin Design and style Bureau is a submarine style heart located in Saint Petersburg, accounting for the structure of more than 85% of submarines in the Soviet and Russian Navy considering the fact that its origins in 1901, includin
 Written content of the weaponized RTF documentg many generations of strategic missile cruiser submarines.
Written content of the weaponized RTF documentg many generations of strategic missile cruiser submarines.
Above the decades, Royal Highway has gained its spot as a software of preference between an array of Chinese threat actors these as Goblin Panda, Rancor Group, TA428, Tick, and Tonto Staff. Recognized for exploiting numerous flaws in Microsoft’s Equation Editor (CVE-2017-11882, CVE-2018-0798, and CVE-2018-0802) as much back as late 2018, the attacks choose the type of targeted spear-phishing campaigns that utilize malicious RTF documents to supply customized malware to unsuspecting significant-benefit targets.
This freshly identified attack is no distinctive, with the adversary employing a spear-phishing email tackled to the submarine style and design agency as an preliminary infection vector. This email arrives embedded with a malware-laced document, which, when opened, drops an encoded file called “e.o” to fetch the PortDoor implant. The encoded payload dropped by previous versions of Royal Highway commonly go by the name of “8.t,” implying a new variant of the weaponizer in use.
Stated to be engineered with obfuscation and persistence in head, PortDoor operates the backdoor gamut with a extensive assortment of capabilities that let it to profile the sufferer equipment, escalate privileges, download, and execute arbitrary payloads been given from an attacker-managed server, and export the final results back again to the server.
“The an infection vector, social engineering fashion, use of RoyalRoad in opposition to equivalent targets, and other similarities amongst the freshly identified backdoor sample and other known Chinese APT malware all bear the hallmarks of a menace actor functioning on behalf of Chinese state-sponsored interests,” the researchers mentioned.
Found this write-up interesting? Abide by THN on Fb, Twitter and LinkedIn to examine much more unique content we put up.
Some areas of this report are sourced from:
thehackernews.com

 Standoff with researchers may emerge as GitHub floats stricter policies
Standoff with researchers may emerge as GitHub floats stricter policies