Consideration readers, if you are using Google Chrome browser on your Windows, Mac, or Linux computers, you need to update it promptly to the most up-to-date version Google produced before these days.
Google on Wednesday rolled out an urgent update for Chrome browser to tackle 14 freshly found security issues, which includes a zero-working day flaw that it says is being actively exploited in the wild.
Tracked as CVE-2021-30551, the vulnerability stems from a form confusion issue in its V8 open up-supply and JavaScript motor. Sergei Glazunov of Google Task Zero has been credited with getting and reporting the flaw.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

While the lookup giant’s Chrome staff issued a terse statement acknowledging “an exploit for CVE-2021-30551 exists in the wild,” Shane Huntley, Director of Google’s Risk Investigation Team, hinted that the vulnerability was leveraged by the very same actor that abused CVE-2021-33742, an actively exploited remote code execution flaw in Windows MSHTML system that was dealt with by Microsoft as section of its Patch Tuesday update on June 8.
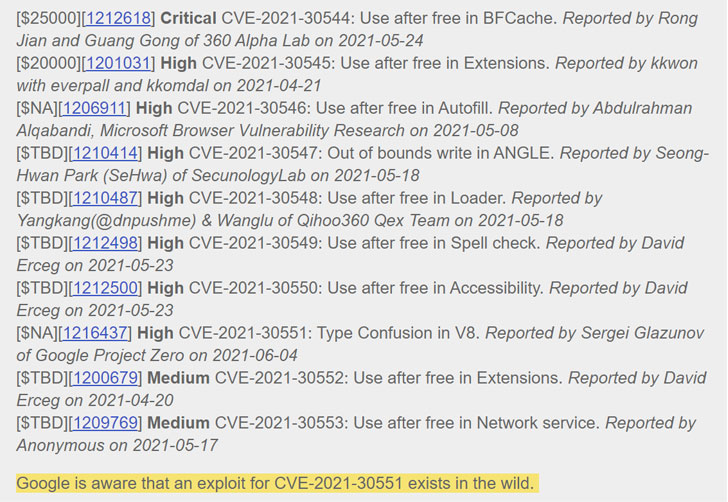
The two zero-times are explained to have been furnished by a business exploit broker to a country-condition actor, which used them in limited attacks versus targets in Eastern Europe and the Center East, Huntley claimed.
Additional complex facts about the character of the attacks are to be launched in the coming weeks so as to let a the vast majority of the end users to set up the update and protect against other threat actors from generating exploits targeting the flaw.

With the hottest repair, Google has addressed a overall of 7 zero-times in Chrome given that the get started of the yr —
- CVE-2021-21148 – Heap buffer overflow in V8
- CVE-2021-21166 – Item recycle issue in audio
- CVE-2021-21193 – Use-following-free of charge in Blink
- CVE-2021-21206 – Use-immediately after-absolutely free in Blink
- CVE-2021-21220 – Insufficient validation of untrusted enter in V8 for x86_64
- CVE-2021-21224 – Form confusion in V8
Chrome consumers can update to the most up-to-date variation (91..4472.101) by heading to Options > Support > About Google Chrome to mitigate the risk related with the flaw.
Identified this write-up fascinating? Follow THN on Fb, Twitter and LinkedIn to study far more exclusive articles we post.
Some sections of this write-up are sourced from:
thehackernews.com


 Infoblox ups integration across on-premises, cloud and remote office environments
Infoblox ups integration across on-premises, cloud and remote office environments