Attention viewers, if you are employing Google Chrome browser on your Windows, Mac, or Linux computer systems, you need to have to update your web browsing software package immediately to the newest edition Google launched previously right now.
Google introduced Chrome model 86..4240.111 currently to patch quite a few security high-severity issues, which include a zero-working day vulnerability that has been exploited in the wild by attackers to hijack targeted desktops.
Tracked as CVE-2020-15999, the actively exploited vulnerability is a variety of memory-corruption flaw named heap buffer overflow in Freetype, a well-liked open up supply software package advancement library for rendering fonts that will come packaged with Chrome.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The vulnerability was found and reported by security researcher Sergei Glazunov of Google Task Zero on October 19 and is matter to a 7-day public disclosure deadline because of to the flaw becoming below active exploitation.
Glazunov also promptly noted the zero-working day vulnerability to FreeType builders, who then formulated an unexpected emergency patch to handle the issue on October 20 with the launch of FreeType 2.10.4.
Devoid of revealing technological specifics of the vulnerability, the technical guide for Google’s Task Zero Ben Hawkes warned on Twitter that though the staff has only spotted an exploit concentrating on Chrome consumers, it really is achievable that other assignments that use FreeType could possibly also be susceptible and are encouraged to deploy the repair integrated in FreeType edition 2.10.4.
“Whilst we only observed an exploit for Chrome, other consumers of freetype ought to adopt the correct discussed in this article: https://savannah.nongnu.org/bugs/?59308 — the deal with is also in present-day steady launch of FreeType 2.10.4,” Hawkes writes.
In accordance to details shared by Glazunov, the vulnerability exists in the FreeType’s purpose “Load_SBit_Png,” which processes PNG illustrations or photos embedded into fonts. It can be exploited by attackers to execute arbitrary code just by using specifically crafted fonts with embedded PNG photos.
“The issue is that libpng makes use of the authentic 32-little bit values, which are saved in `png_struct`. For that reason, if the initial width and/or height are larger than 65535, the allotted buffer would not be capable to match the bitmap,” Glazunov spelled out.
Glazunov also printed a font file with a proof-of-principle exploit.
Google introduced Chrome 86..4240.111 as Chrome’s “stable” variation, which is readily available to all people, not just to opted-in early adopters, saying that the enterprise is knowledgeable of stories that “an exploit for CVE-2020-15999 exists in the wild,” but did not expose further more facts of the lively attacks.
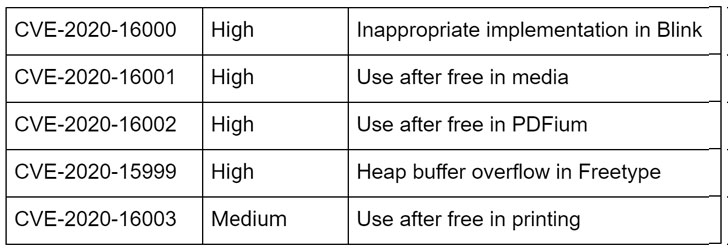
Besides the FreeType zero-working day vulnerability, Google also patched four other flaws in the most current Chrome update, a few of which are large-risk vulnerabilities—an inappropriate implementation bug in Blink, a use just after free of charge bug in Chrome’s media, and use just after totally free bug in PDFium—and just one medium-risk use after totally free issue in browser’s printing functionality.
Though the Chrome web browser automatically notifies users about the latest accessible edition, users are encouraged to manually induce the update course of action by likely to “Enable → About Google Chrome” from the menu.
Identified this write-up attention-grabbing? Comply with THN on Fb, Twitter and LinkedIn to study much more distinctive content material we submit.
Some sections of this article are sourced from:
thehackernews.com


 #GlobalEthicsDay2020: New Security Incident Response Ethics Guidelines Released
#GlobalEthicsDay2020: New Security Incident Response Ethics Guidelines Released